
In today’s world, where data breaches and cyber threats are ever-present, the importance of information security assessments stands out more than ever. These evaluations act as a vital line of defense, allowing organizations to pinpoint vulnerabilities, evaluate risks, and ensure compliance with regulations.
But how can businesses effectively tackle the complexities of conducting a thorough assessment? This guide not only clarifies the process but also outlines the essential steps for mastering information security assessments. By doing so, it empowers organizations to strengthen their defenses and protect sensitive data.
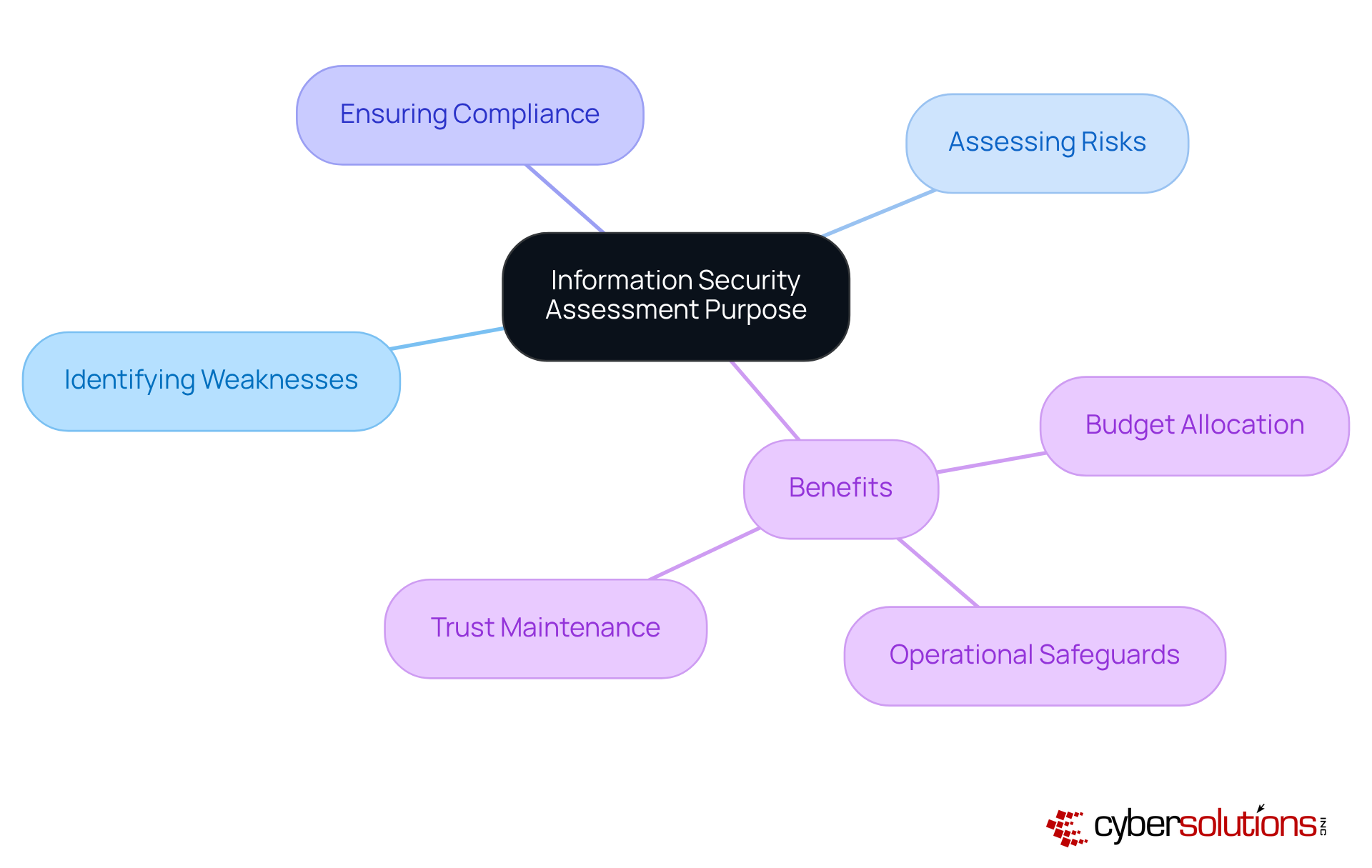
An information security assessment is not just a procedure; it’s a vital strategy that evaluates a company’s safety stance by pinpointing weaknesses, assessing risks, and ensuring compliance with relevant regulations. Did you know that 42% of firms believe their budgets are adequately funded? This statistic underscores a growing recognition of the importance of information security. An information security assessment is essential for building and maintaining trust with clients and stakeholders. For instance, companies like Jaguar Land Rover have faced significant breaches, illustrating the urgent need for comprehensive assessments.
Understanding the purpose of these evaluations, including an information security assessment, allows organizations to prioritize their security measures and allocate resources effectively. Security experts emphasize that regular assessments not only enhance protective frameworks but also assist organizations in identifying vulnerabilities. As the landscape evolves, the importance of conducting thorough assessments cannot be overstated. They are crucial for any organization aiming to safeguard its assets and uphold its reputation.
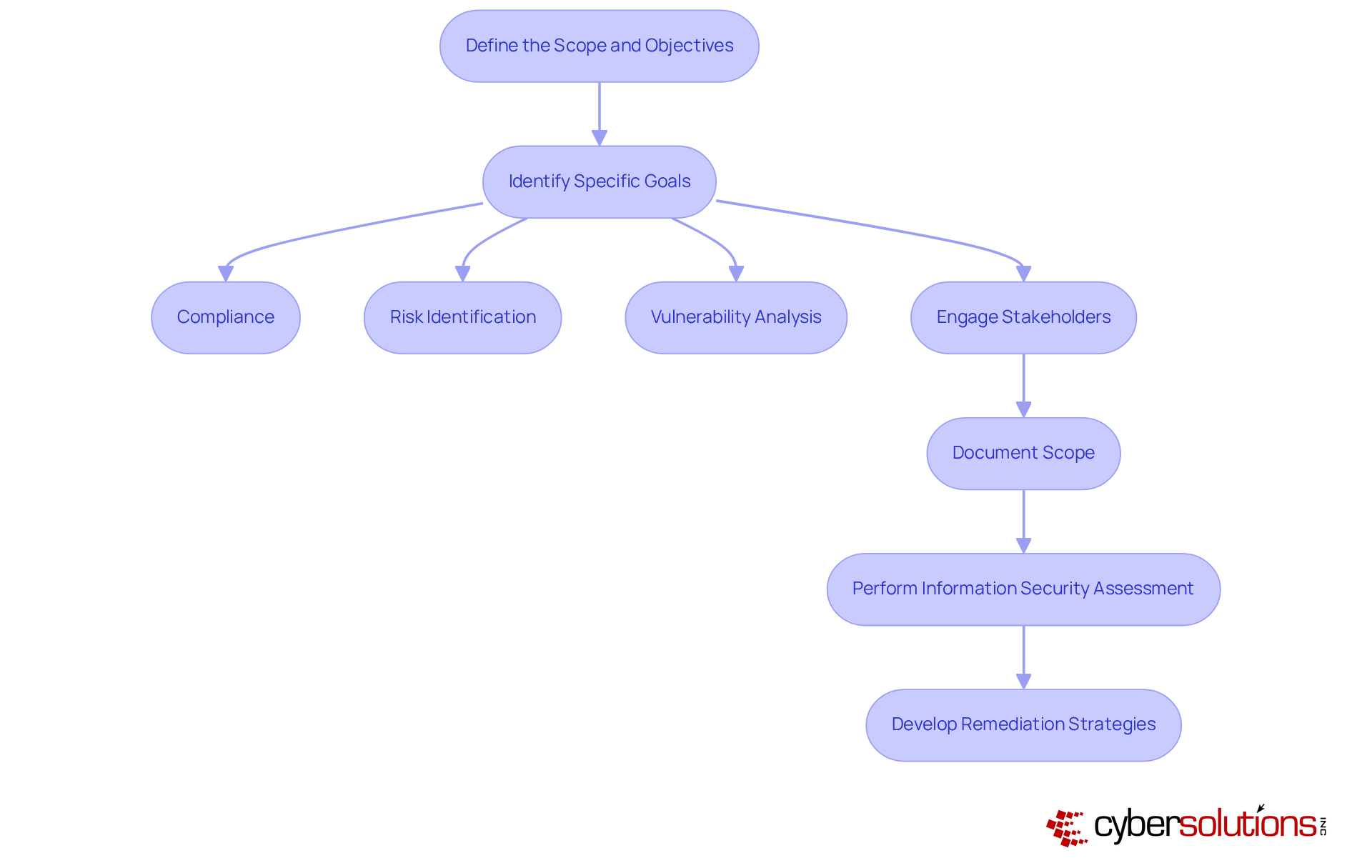
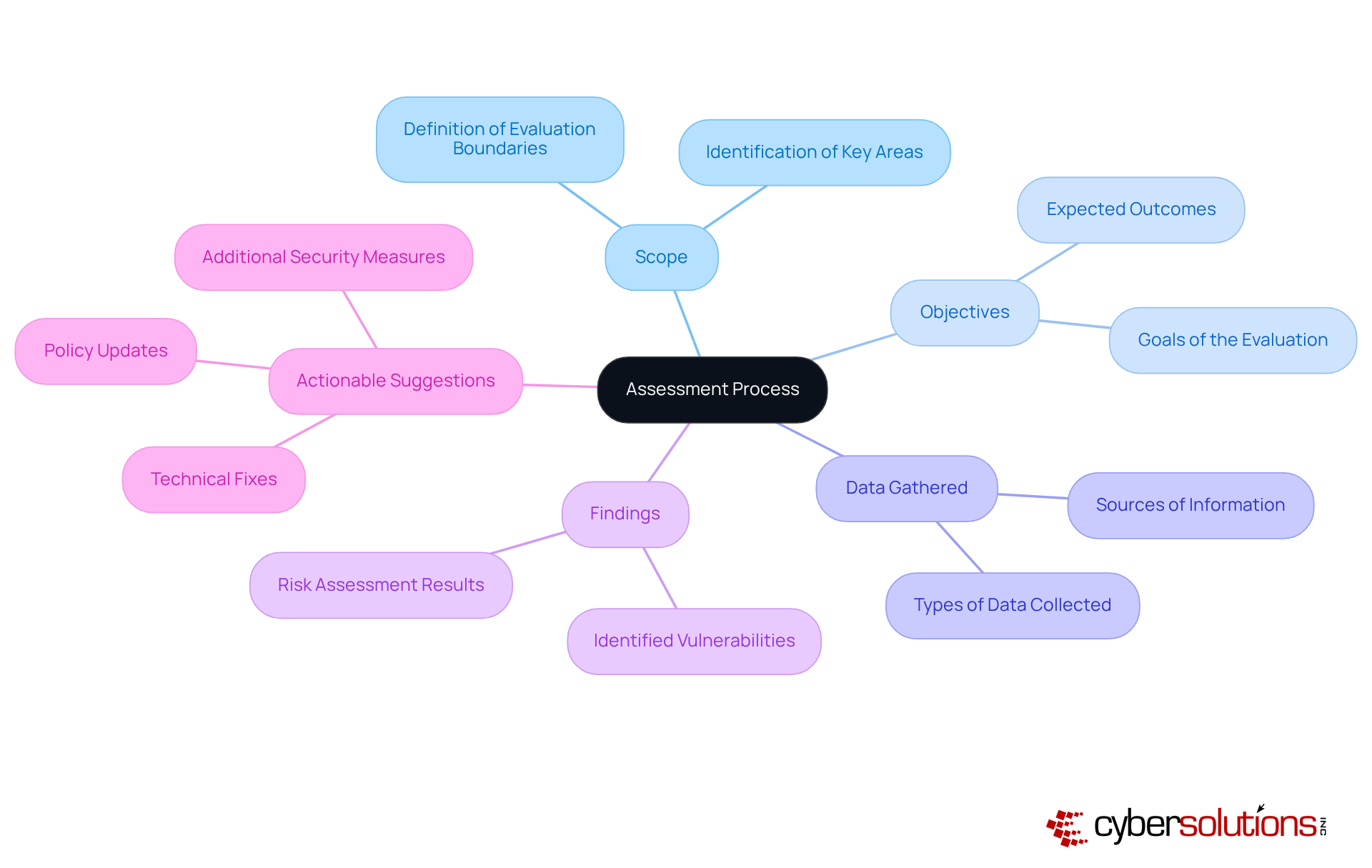
Recognizing the critical importance of cybersecurity in today's landscape is essential for any organization. The assets that require protection—sensitive data, systems, and networks—are under constant threat. Therefore, it's vital to outline the scope and objectives of your assessment clearly. Start by identifying specific goals, such as:
Engaging stakeholders is crucial; their feedback ensures that the evaluation aligns with organizational priorities. Clearly document the scope, specifying what will and will not be included in the evaluation. This clarity maintains focus throughout the process. Additionally, perform an assessment to evaluate your current cybersecurity posture and identify gaps in your systems. This assessment will inform tailored remediation strategies, including necessary policy updates, system upgrades, and process improvements to achieve compliance with regulations.
By preparing comprehensive documentation—policies and procedures—you can effectively demonstrate compliance during audits. Consider conducting a simulated audit to ensure your organization is fully prepared for the official CMMC evaluation. This proactive approach allows you to address any outstanding concerns and seek professional advice throughout the process, ultimately enhancing your security posture.
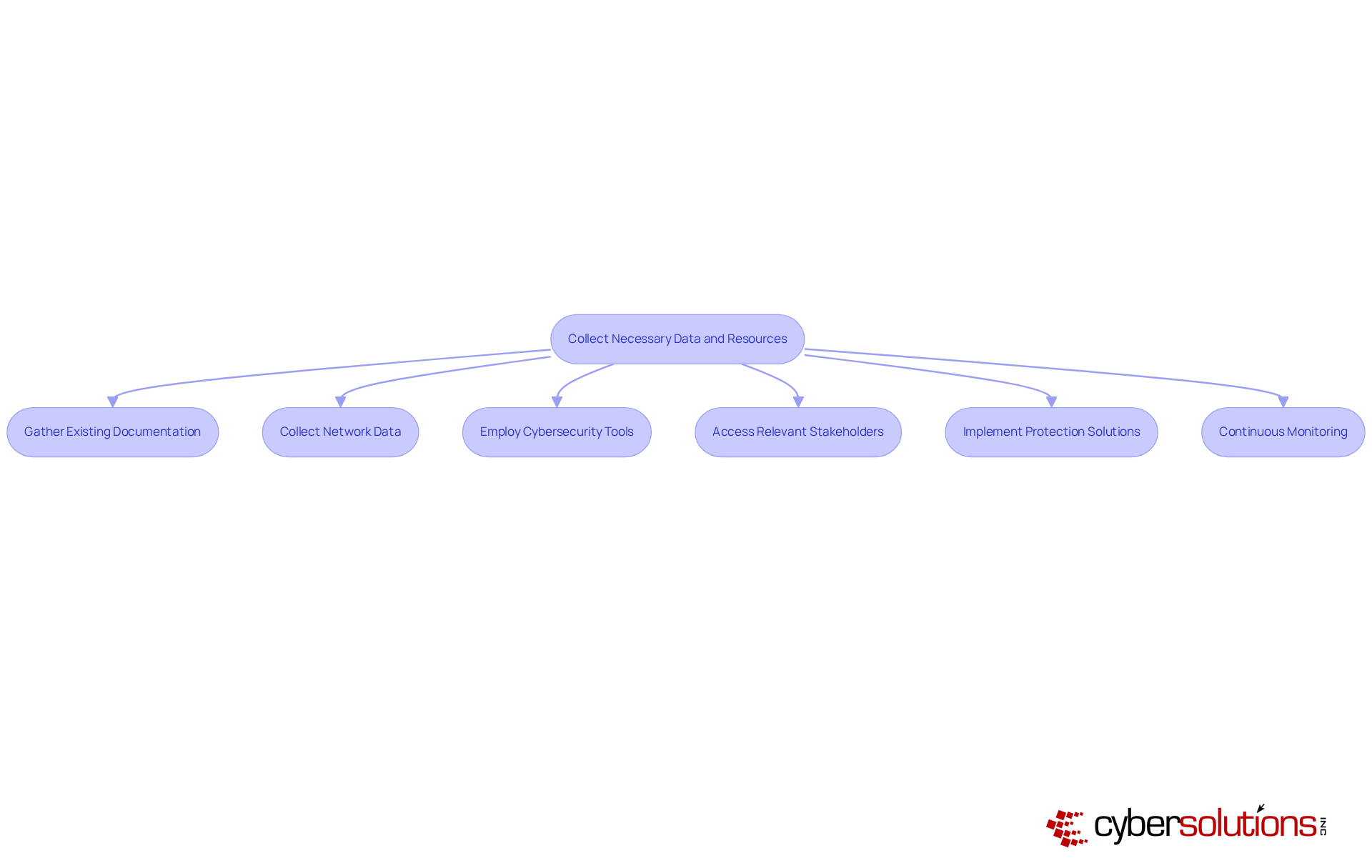
In today's digital landscape, the importance of robust information security cannot be overstated, especially in healthcare. Start by gathering all existing documentation related to your organization's security protection policies, procedures, and prior assessments. Collect comprehensive data on network architecture, system configurations, and user access controls for the assessment. To enhance your understanding of vulnerabilities, employ tools such as vulnerability scanners, security information and event management (SIEM) systems, and threat intelligence to gather real-time data on incidents and threats.
Ensure you have access to relevant stakeholders who can provide valuable insights into operational practices and potential risks. Additionally, consider implementing extensive monitoring solutions, coupled with round-the-clock surveillance. This proactive approach will help identify anomalies and possible vulnerabilities before they escalate into serious threats.
Continuous monitoring is essential; it allows for the early detection of suspicious activities, forming a crucial part of your comprehensive data collection strategy. By incorporating proactive monitoring and threat detection, you can significantly enhance your protective stance, ensuring that your organization is well-equipped to face the evolving landscape of cybersecurity threats.
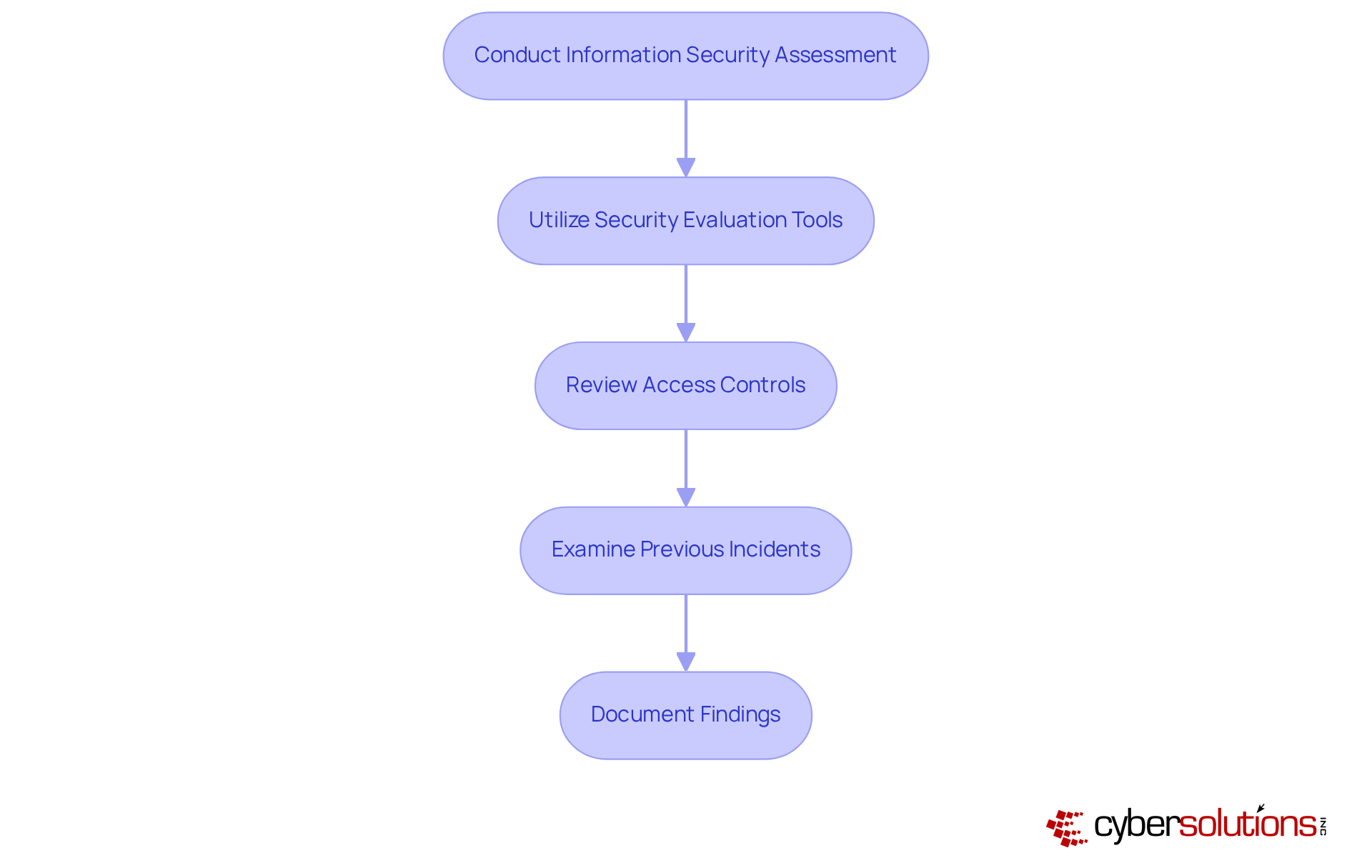
In today's digital landscape, the importance of robust cybersecurity measures cannot be overstated, especially for organizations handling sensitive federal information. Conduct a thorough assessment of your current protective measures—firewalls, intrusion detection systems, and antivirus software—to ensure they meet the stringent standards required for compliance. This is not just a regulatory requirement; it is a critical step in safeguarding against evolving threats.
Utilize vulnerability assessments as part of your strategy to identify flaws in your systems and applications. This proactive approach is crucial for protecting Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). Additionally, review access controls and user permissions meticulously to guarantee that only authorized personnel have access to sensitive data. Are your current protocols sufficient to prevent unauthorized access?
Examine previous incidents to recognize trends and persistent weaknesses. Understanding these patterns can significantly enhance your entity's overall cybersecurity stance. Document all discoveries to create a clear view for your organization and protective environment. This not only guides subsequent actions in the evaluation process but also showcases your commitment to cybersecurity and your capability to secure federal contracts.
By taking these steps, you position your organization to effectively address the unique challenges of cybersecurity, ensuring compliance and fostering trust with stakeholders.
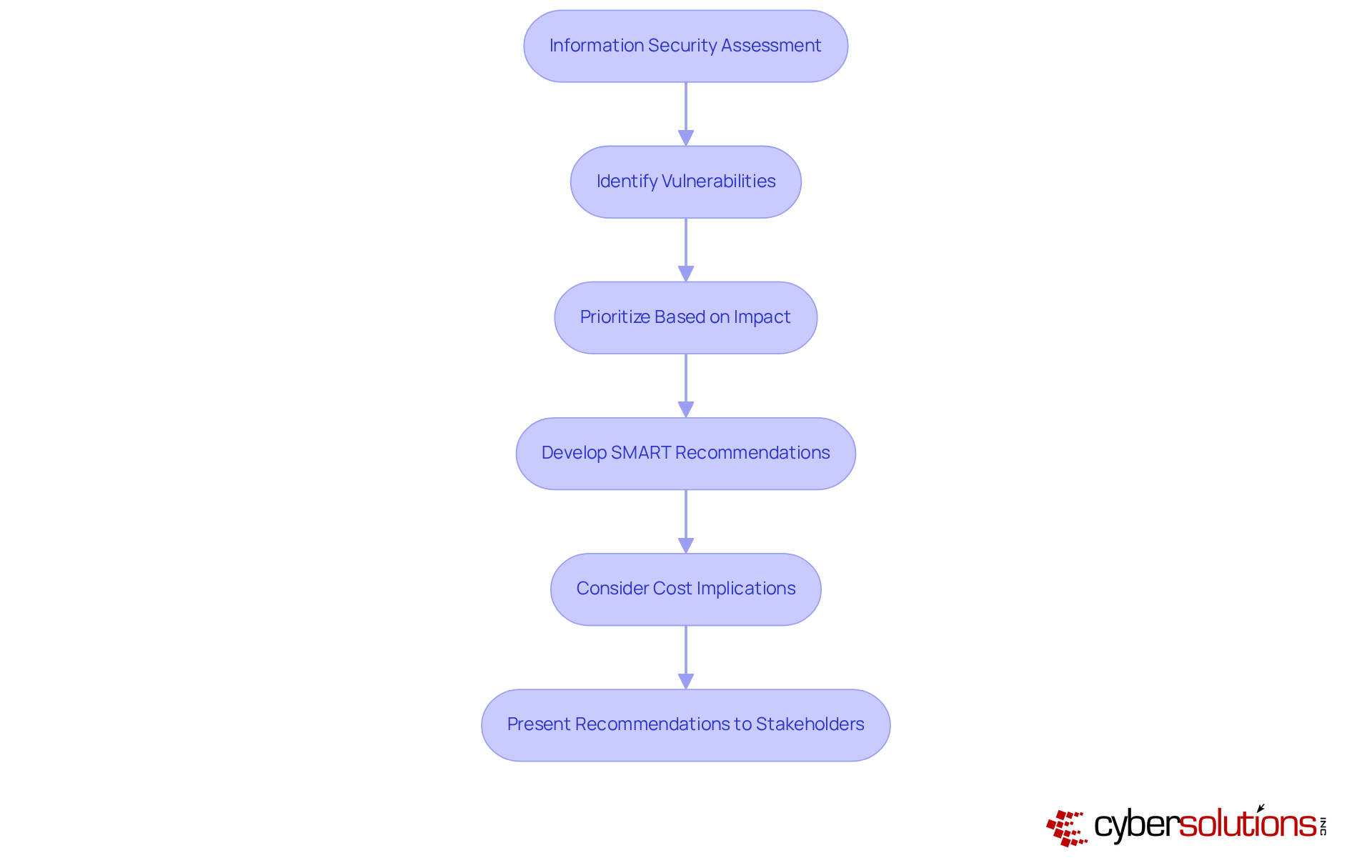
In today's digital landscape, the importance of information security cannot be overstated. An assessment of your existing safety protocols is crucial to identifying patterns and vulnerabilities. By prioritizing these vulnerabilities based on their potential impact, you can effectively guide your remediation efforts.
Develop recommendations that specifically address each identified issue, ensuring they meet the criteria of specific, measurable, achievable, relevant, and time-bound. For instance, organizations that have implemented SMART suggestions have reported a significant improvement, underscoring the effectiveness of this approach.
Consider the cost implications of each recommendation and how they align with your overall strategy, particularly in relation to the organization's goals. Take, for example, a financial institution that prioritized security measures and established a robust framework, resulting in a 30% decrease in breach attempts within the first year. Present these recommendations clearly and concisely to facilitate informed decision-making among stakeholders, ensuring they grasp the rationale behind each suggestion and its anticipated impact on the organization's security posture.
Create a comprehensive report that meticulously documents the entire assessment process. This includes:
Documentation is essential to ensure that the report is accessible to all stakeholders, regardless of their technical expertise.
Visual aids, such as charts and graphs, should be included to effectively illustrate data and trends. A logical structure is crucial, making it easy for readers to follow the progression of the evaluation. This documentation will not only serve as a valuable resource for future evaluations but also for compliance efforts, reinforcing the importance of maintaining standards and accountability.
In today's rapidly evolving digital landscape, the importance of information security, highlighted by an increasing number of cyber threats, cannot be overstated, especially in the healthcare sector. With increasing threats targeting sensitive patient data, organizations require an immediate response and immediate attention. CFOs, in particular, must navigate these complexities to ensure compliance.
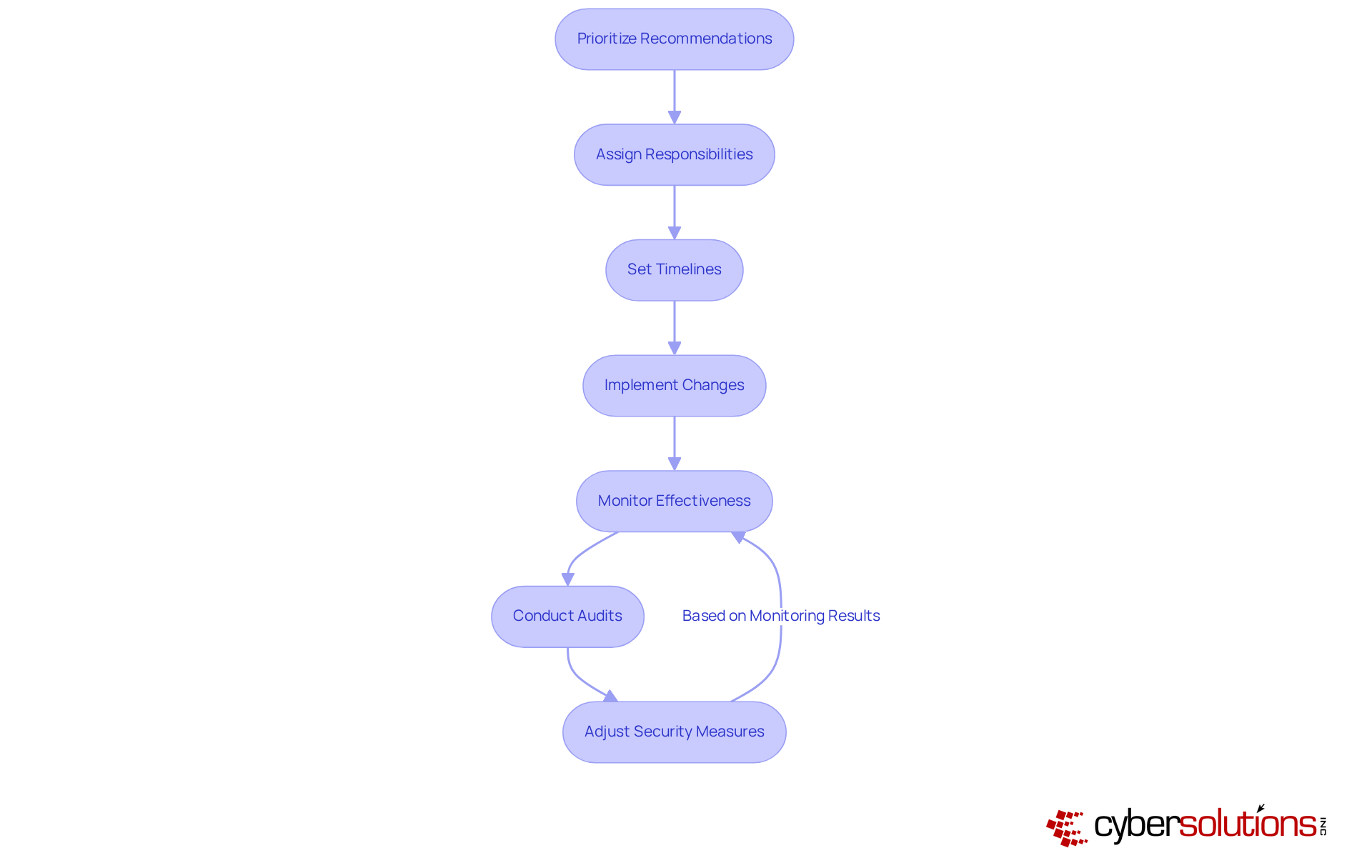
Start by prioritizing the suggestions identified during the analysis phase, focusing first on those that address the most critical vulnerabilities. Assign specific responsibilities to relevant team members and set clear timelines for implementation. Once changes are in place, it’s essential to monitor their effectiveness through regular audits, assessments, and an evaluation process. This proactive approach not only helps in identifying weaknesses but also fosters a culture of continuous improvement.
Adjust security measures as necessary, based on ongoing monitoring and emerging threats. This iterative process ensures that your organization remains resilient against evolving risks. By embracing these strategies, CFOs can lead their organizations toward a more secure future, ultimately protecting both patient data and institutional integrity.
Mastering the complexities of information security assessments is not just essential; it’s a critical investment for organizations determined to protect sensitive data and comply with industry regulations. In today’s landscape, where cyber threats are ever-evolving, these assessments act as a proactive shield, identifying vulnerabilities and assessing risks to bolster overall security posture. By grasping the purpose and scope of these evaluations, organizations can strategically allocate resources and prioritize their cybersecurity initiatives.
This guide outlines key steps that are vital for success:
Each phase is crucial, ensuring that organizations not only meet compliance requirements but also effectively safeguard their assets against emerging cyber threats. The emphasis on continuous monitoring and iterative improvements highlights the necessity of adapting to the dynamic cybersecurity landscape.
Ultimately, conducting a thorough information security assessment transcends mere regulatory obligation; it represents a vital investment in an organization’s future. By prioritizing cybersecurity and adopting a proactive stance, organizations can build trust with clients and stakeholders, mitigate potential risks, and enhance their resilience against cyber threats. Embracing these practices is essential for navigating the complexities of today’s digital environment, ensuring long-term security and compliance.
What is the purpose of an information security assessment?
An information security assessment evaluates a company’s safety stance by identifying weaknesses, assessing risks, and ensuring compliance with relevant regulations. It is essential for safeguarding sensitive data and maintaining trust with clients and stakeholders.
Why are information security assessments important?
Information security assessments are crucial for prioritizing protective measures, allocating resources effectively, enhancing protective frameworks, and navigating compliance and risk management complexities. They help organizations safeguard their assets and uphold their reputation.
What should be included in the scope and objectives of an information security assessment?
The scope and objectives should include compliance with regulations, risk identification, and vulnerability analysis. It is important to clearly document what will and will not be included in the evaluation to maintain focus throughout the process.
How can organizations prepare for an information security assessment?
Organizations can prepare by engaging stakeholders for feedback, documenting policies and procedures, and conducting an information security assessment to evaluate their current cybersecurity posture. This assessment helps identify gaps and informs tailored remediation strategies.
What is the significance of compliance in information security assessments?
Compliance is significant as it ensures that organizations meet regulatory requirements. Preparing comprehensive documentation and conducting simulated audits can help organizations demonstrate compliance during official evaluations, such as CMMC standards.
How can organizations address concerns before an official evaluation?
Organizations can address concerns by conducting a simulated audit to identify and rectify outstanding issues. Seeking professional advice throughout the process can further fortify their cybersecurity framework.