
USB drop attacks represent a significant and growing threat in the cybersecurity landscape, leveraging human curiosity to infiltrate systems and compromise sensitive data. As organizations grapple with an alarming increase in these low-tech yet highly effective tactics, it becomes crucial to understand the mechanics behind USB drop attacks to protect business integrity. How can companies effectively shield themselves from this insidious method that targets unsuspecting employees and risks devastating financial and reputational damage?
The current landscape of cybersecurity threats is evolving, and USB drop attacks are at the forefront of this challenge. These attacks exploit the natural curiosity of individuals, leading them to unwittingly introduce malware into their organizations. The implications for businesses are severe, as a single compromised device can lead to extensive data breaches and significant financial losses.
To combat these threats, organizations must adopt proactive measures. Implementing comprehensive cybersecurity training for employees is essential, ensuring they recognize the risks associated with unknown USB devices. Additionally, investing in advanced security solutions can help detect and neutralize threats before they escalate. By taking these steps, companies can fortify their defenses against USB drop attacks and safeguard their sensitive information.
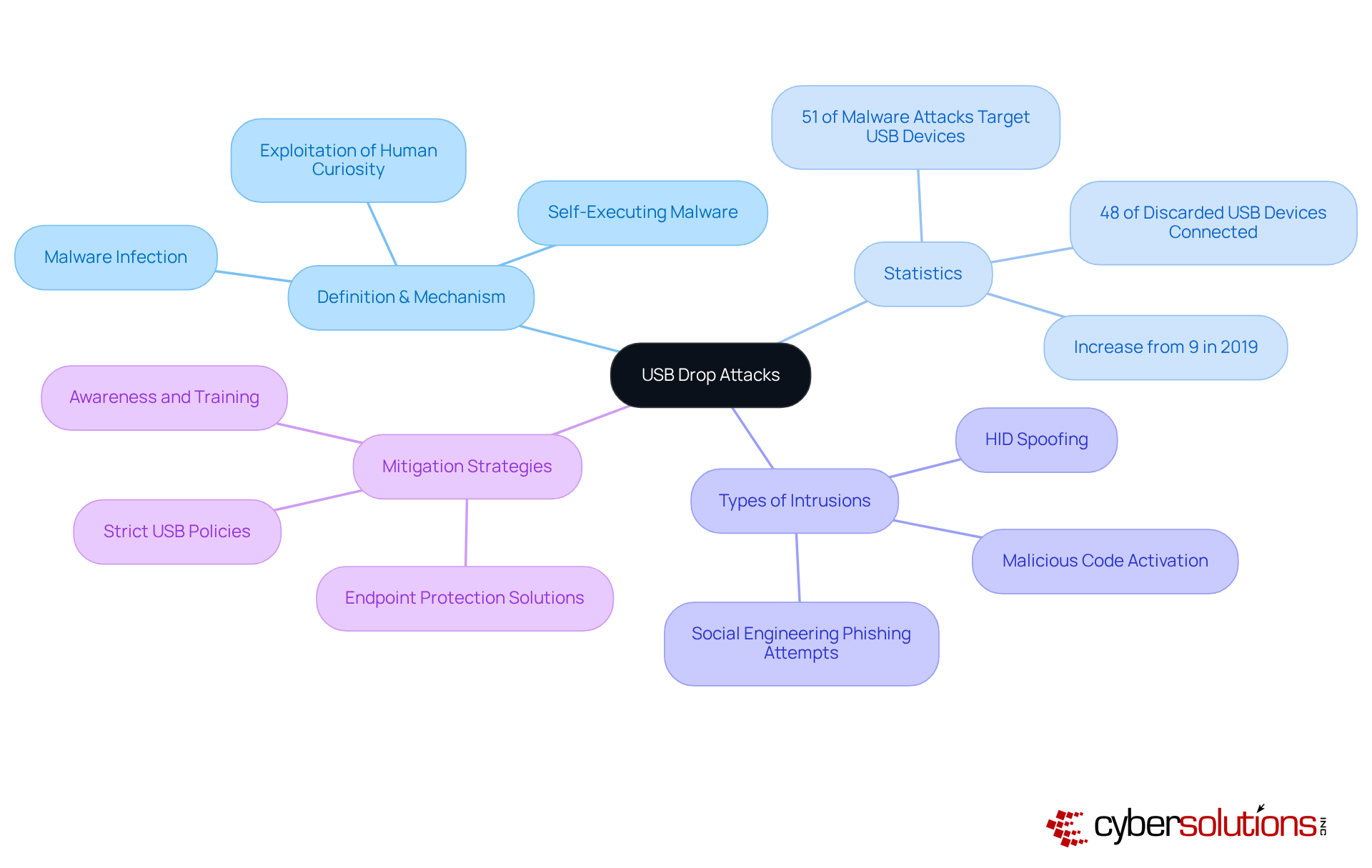
pose a significant threat in the realm of cybersecurity, especially as they take advantage of human curiosity in public spaces. Attackers strategically leave infected USB sticks, and when an unsuspecting individual connects one, harmful software can execute automatically, leading to potential system compromise. This tactic is further enhanced by enticing labels or disguises that make these drives appear legitimate, increasing the likelihood of their use.
Recent statistics reveal a startling trend:
It is clear that awareness and training are crucial in mitigating these risks. Organizations should implement strict policies regarding USB usage, which have been pre-checked for security. The primary goal of USB drop attacks is to achieve unauthorized access, often through self-executing malware or booby-trapped documents. Additionally, other types of USB drop intrusions include:
In conclusion, proactive security is paramount. By safeguarding sensitive information and maintaining operational integrity, organizations can effectively combat the rising threat of USB drop attacks.
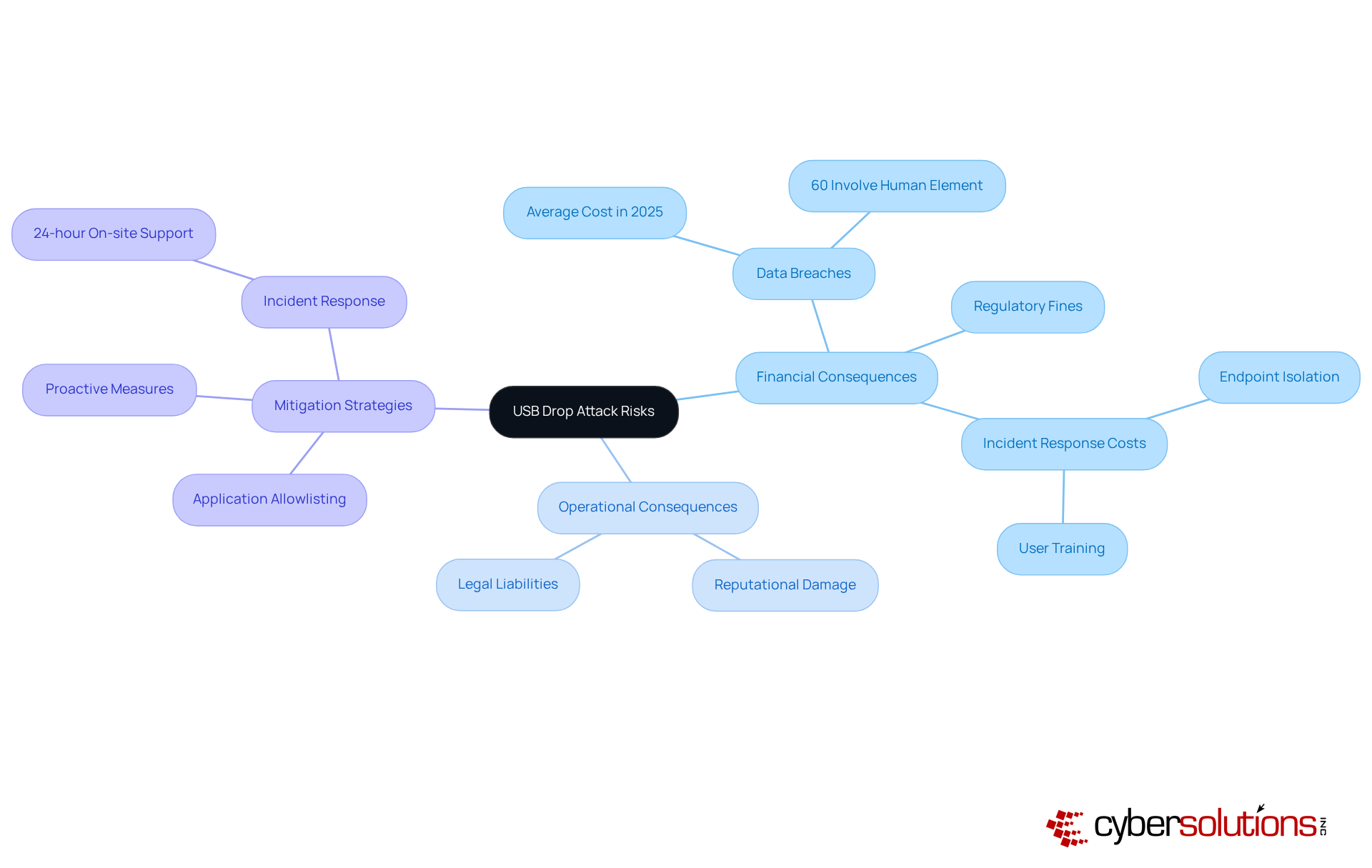
present significant risks to businesses, resulting in severe financial and operational consequences. The immediate threat includes data breaches, where sensitive information can be stolen or compromised. In 2025, the average cost is projected to reach approximately $4.9 million globally, reflecting a 10% increase from the previous year. This financial burden encompasses theft, regulatory fines, and the extensive costs associated with incident response and recovery efforts, including endpoint isolation and user training, which are critical components of a comprehensive security strategy.
Moreover, the reputational damage stemming from a data breach can erode customer trust, resulting in long-term financial impacts. Organizations may also face legal liabilities if they fail to adequately protect sensitive data, further compounding their financial woes. For instance, in 2025, 60% of data breaches are expected to involve a human element, such as malicious insiders or phishing scams, underscoring the critical need for robust security measures.
Cybersecurity analysts emphasize the importance of proactive strategies to mitigate these risks. Philip Törner, a Senior Security Consultant, warns that the simplicity of the attack method makes it particularly effective. He observes that a USB drop attack can occur once a USB device is connected, allowing malware to be installed and granting attackers access to sensitive files and systems. To combat these threats, Cyber Solutions Inc. advocates for a layered approach to cybersecurity, including measures such as employee training, which can help contain threats quickly and effectively. Additionally, implementing application whitelisting can proactively prevent unauthorized software from running, thereby decreasing the vulnerability surface and enhancing overall security.
Alarmingly, 45% of the collected USB devices were connected to computers by inquisitive individuals, emphasizing the need for organizations to prioritize cybersecurity investments and establish strict policies to prevent USB drop attacks and protect against such threats.
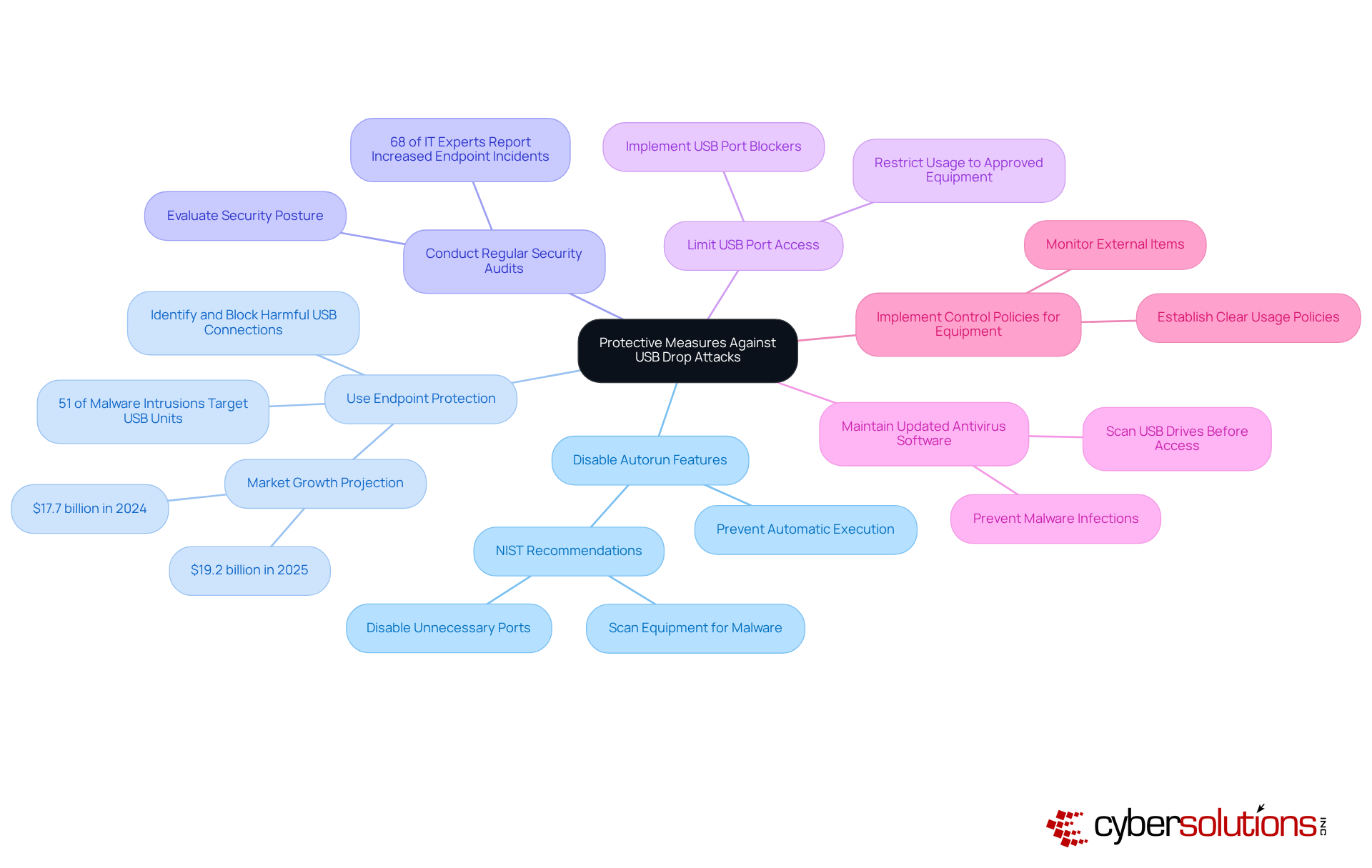
To effectively safeguard against USB drop attacks, organizations must prioritize cybersecurity measures that address this growing threat. USB drop attacks pose significant risks, especially in environments where sensitive data is managed. Implementing a series of best practices can dramatically reduce vulnerabilities and enhance overall security.
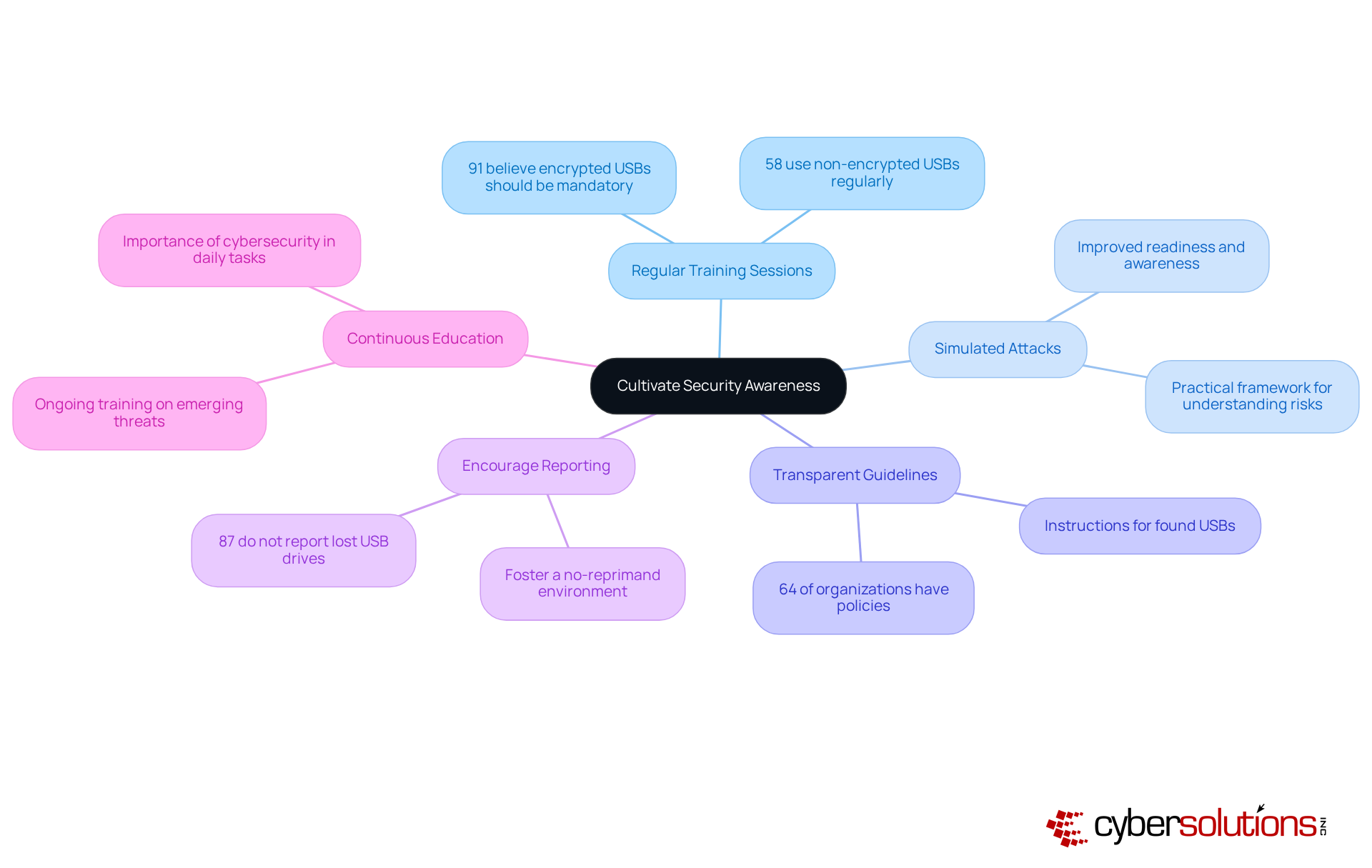
To effectively combat USB drop attacks, organizations must foster a robust culture of security awareness. This is not just a recommendation; it’s a necessity in today’s digital landscape. Here are several key strategies to enhance your organization’s defenses:
By prioritizing these strategies, organizations can significantly enhance their security posture and mitigate the risks associated with a USB drop attack.
Understanding and combating USB drop attacks is not just important; it’s essential for safeguarding business operations and sensitive data. These attacks prey on human curiosity, leading to potentially devastating consequences like data breaches and financial losses. By recognizing the mechanisms behind these threats and implementing effective protective measures, organizations can significantly reduce their vulnerability.
Key strategies include:
Moreover, fostering a culture of security awareness through employee training and transparent policies is crucial. With statistics highlighting the alarming rise in USB-related malware, it’s clear that proactive measures are not merely advisable but necessary for maintaining cybersecurity integrity.
Ultimately, the fight against USB drop attacks demands a comprehensive approach that combines technology, policy, and human vigilance. Organizations must prioritize cybersecurity investments and cultivate an environment where employees are informed and engaged in protecting their digital assets. Embracing these practices will not only fortify defenses against USB drop attacks but also contribute to a more resilient cybersecurity posture overall.
What is a USB drop attack?
A USB drop attack is a cybersecurity threat where attackers leave infected USB sticks in public spaces, exploiting human curiosity. When someone connects the USB to their device, harmful software can execute automatically, potentially compromising the system.
How do attackers make infected USB drives more appealing?
Attackers often use enticing labels or disguises to make infected USB drives appear legitimate, increasing the likelihood that unsuspecting individuals will connect them to their devices.
What are the recent statistics regarding USB attacks?
Recent statistics show that 51% of malware attacks now target USB connections, up from just 9% in 2019, highlighting the growing threat posed by USB drop attacks.
What did the study from the University of Illinois Urbana-Champaign reveal about USB devices?
The study found that nearly 48% of discarded USB devices were connected, demonstrating the effectiveness of the manipulation tactic used in USB drop attacks.
How can organizations mitigate the risks of USB drop attacks?
Organizations can mitigate these risks by raising awareness and providing training, as well as implementing policies that allow only authorized USB drives that have been pre-checked for security.
What is the primary goal of a USB drop attack?
The primary goal of a USB drop attack is to achieve malware infection, often through self-executing malware or booby-trapped documents.
What are some types of USB drop intrusions?
Types of USB drop intrusions include malicious code activation and HID (Human Interface Device) spoofing, which can further compromise systems.
Why is vigilance in cybersecurity practices important?
Vigilance in cybersecurity practices is crucial for safeguarding sensitive information and maintaining operational integrity, which helps organizations effectively combat the rising threat of USB drop attacks.