
In an era where cyber threats are becoming increasingly sophisticated, organizations face the daunting challenge of safeguarding their digital assets. Understanding the nuances between vulnerability scanning and penetration testing is essential for developing a robust cybersecurity strategy. This article explores ten key insights that reveal how these two critical components work in tandem to not only identify potential weaknesses but also simulate real-world attacks. By providing organizations with a comprehensive approach to risk management, we pose a crucial question:
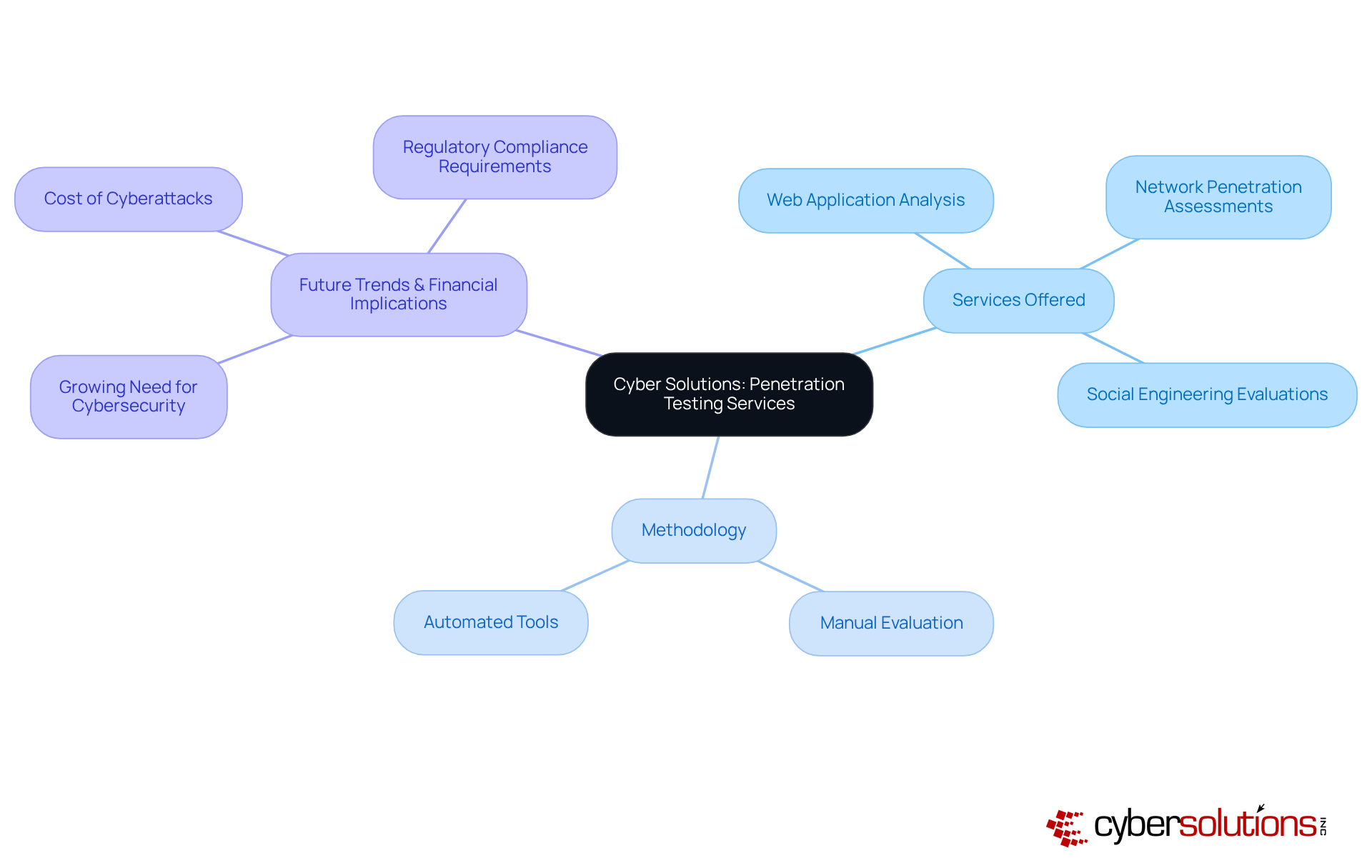
In today's digital landscape, the importance of robust cybersecurity cannot be overstated. Cyber Solutions Inc. offers an extensive range of services designed to reveal and exploit weaknesses within a company's IT framework. Their methodology combines both manual evaluation and automated tools, ensuring comprehensive coverage across various areas, including:
This customized approach meets the specific requirements of various sectors, enabling entities to not only identify weaknesses but also evaluate the potential impact of vulnerabilities.
As we look ahead to 2025, the average expense of cybersecurity breaches is anticipated to mirror the growing need for strong cybersecurity strategies. Numerous entities are acknowledging that safeguarding their networks and protecting sensitive information is essential. The evolving nature of cyber threats highlights the necessity for regular vulnerability assessments, as both serve as critical components of a comprehensive security strategy, enabling businesses to fortify their defenses and protect customer trust.
By investing in these services, entities position themselves to effectively reduce risks and improve their overall protection stance. Proactive measures today can safeguard against potential threats tomorrow, ensuring that organizations remain resilient in the face of increasing cyber challenges.
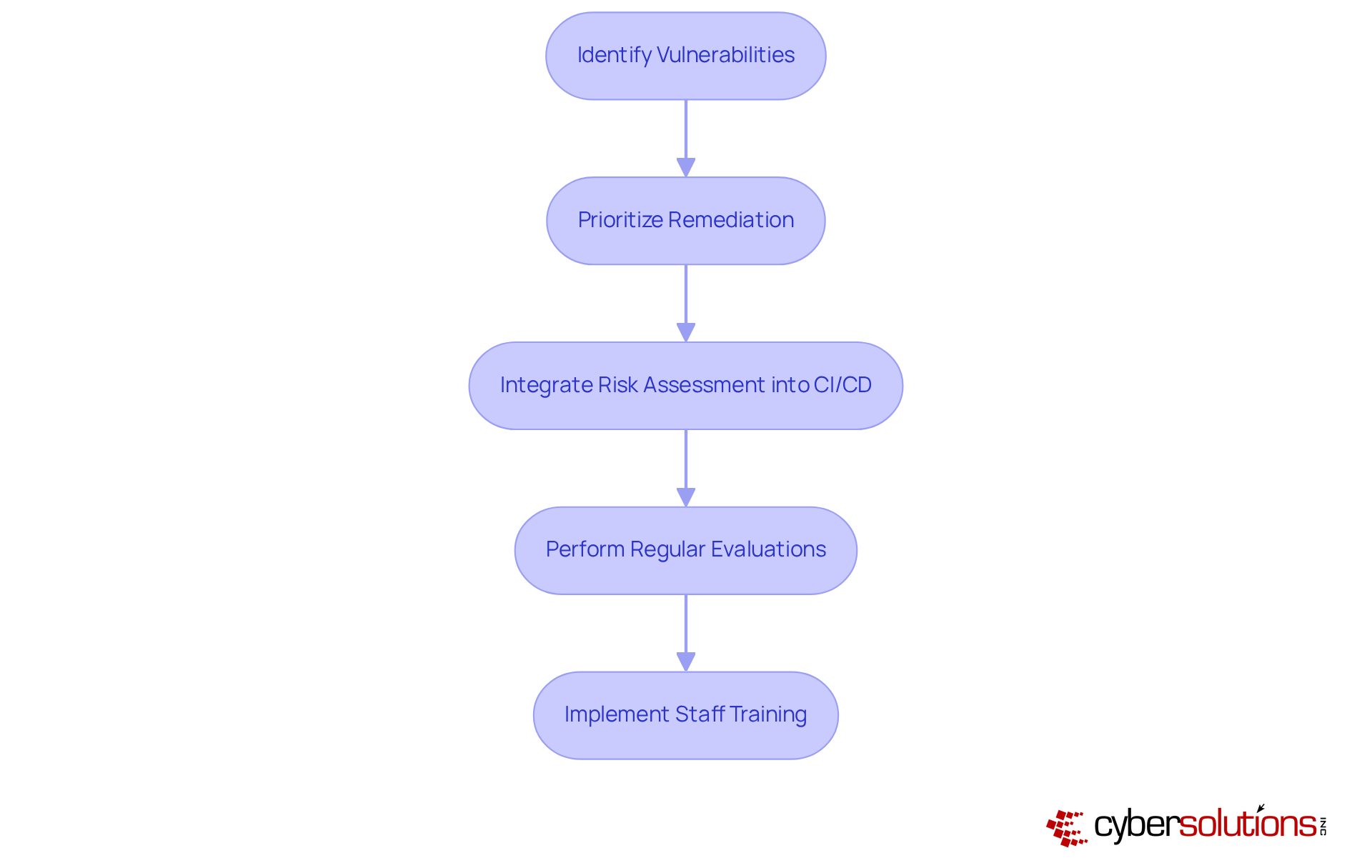
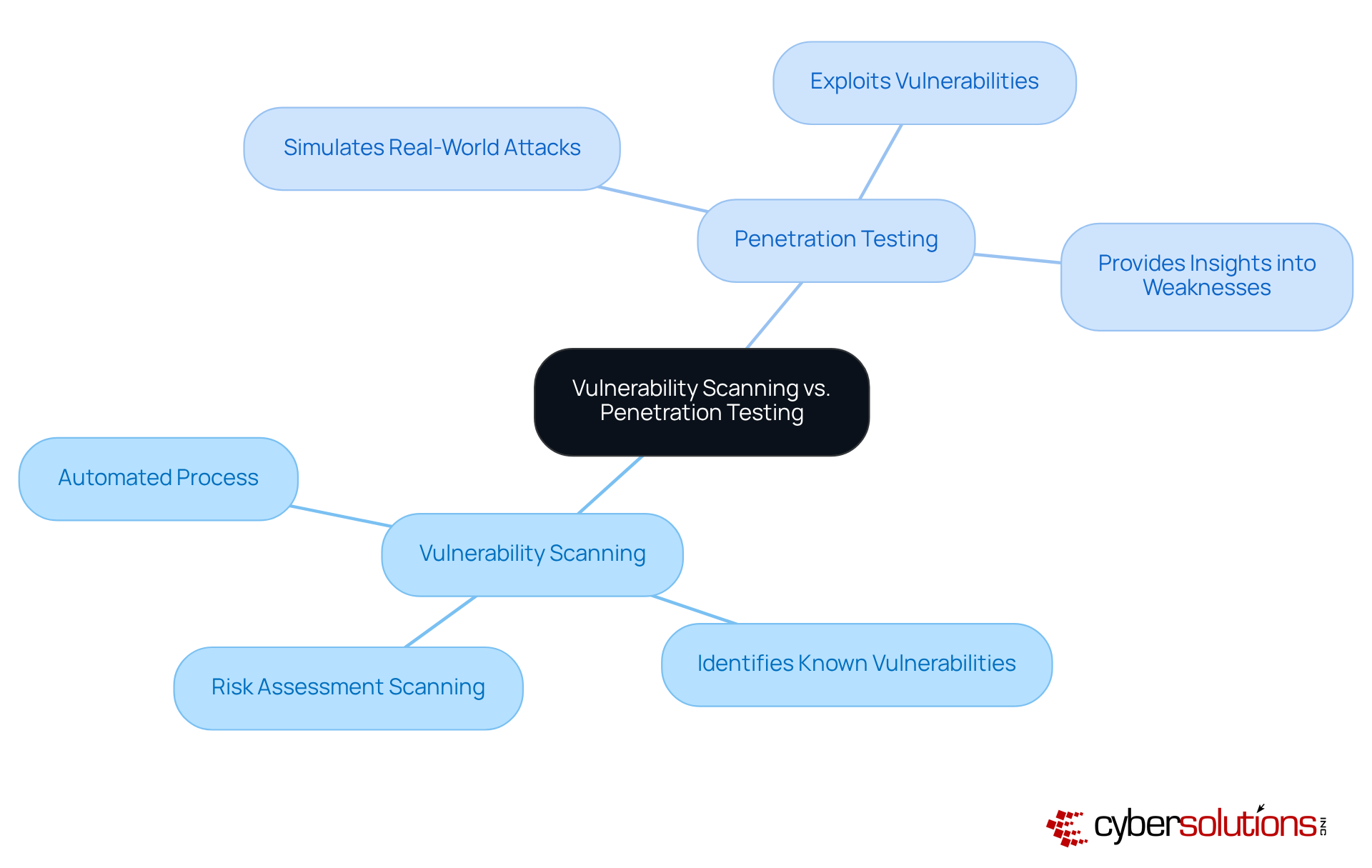
Vulnerability scanning highlights the automated process crucial for detecting known weaknesses within a company's systems, networks, and applications. In the current landscape of cybersecurity, understanding vulnerability scanning vs penetration testing is essential for establishing a security strategy, enabling organizations to prioritize their remediation efforts efficiently. Regular evaluations are essential to maintain a robust protective stance against increasingly sophisticated cyberattacks.
By consistently performing vulnerability scans as part of their security assessments, companies can adopt a proactive approach, addressing weaknesses before they can be exploited by attackers. Current best practices emphasize the integration of security measures into the continuous deployment (CI/CD) pipeline, ensuring that security is a fundamental aspect of the development process. This integration not only streamlines the identification of weaknesses but also facilitates quicker remediation, significantly reducing the window of exposure.
Organizations across various sectors, including healthcare and finance, have reported significant enhancements in their protection frameworks through regular risk assessments. This proactive approach is vital in today's threat landscape, where cyberattacks are both frequent and sophisticated. Cyber Solutions Inc. exemplifies this methodology by implementing network hardening strategies that effectively close potential attack vectors and enhance protective configurations. Moreover, staff training focused on recognizing suspicious emails and maintaining proper cybersecurity hygiene further fortifies defenses against emerging threats.
While both aim to enhance security, they serve distinct purposes that are critical to understand.
Understanding the difference in methodologies is essential for organizations as they formulate their security strategies.
When considering vulnerability scanning vs penetration testing, it is essential for organizations aiming to enhance their security posture. It offers numerous benefits, including:
In today’s rapidly evolving threat landscape, understanding the difference between vulnerability scanning vs penetration testing is crucial, as it is not merely an option; it is a necessity for maintaining robust cybersecurity.

Penetration testing is an essential component of a robust cybersecurity strategy, providing several key advantages that organizations cannot afford to overlook:
Statistics show that a significant proportion of enterprises perform penetration assessments each year, highlighting its significance in proactive cybersecurity strategies. Practical instances demonstrate how companies have effectively employed penetration testing to strengthen their incident response strategies, ultimately resulting in better outcomes and decreased risk exposure.

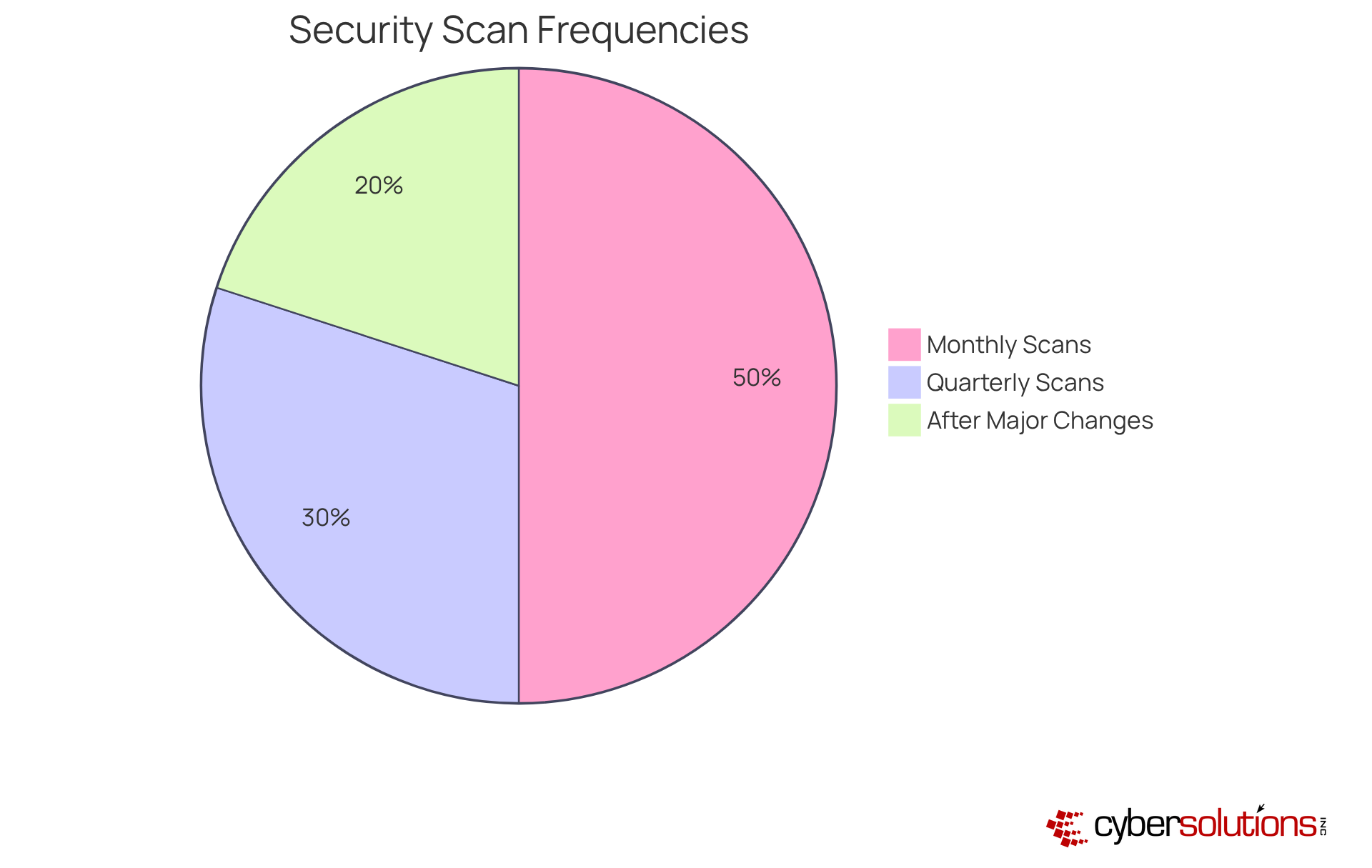
The frequency of vulnerability scans is critical, influenced by factors such as the entity's size, sector, and risk appetite. Best practices in cybersecurity underscore the necessity of regular assessments to safeguard organizational assets.
When considering penetration testing vs vulnerability scanning, it's clear that it is essential to fortify cybersecurity defenses, especially in the face of evolving threats. To ensure maximum effectiveness, organizations should perform penetration testing at the following times:
By adhering to these guidelines, organizations can enhance their defensive posture and better protect themselves against the increasing frequency of cyberattacks.

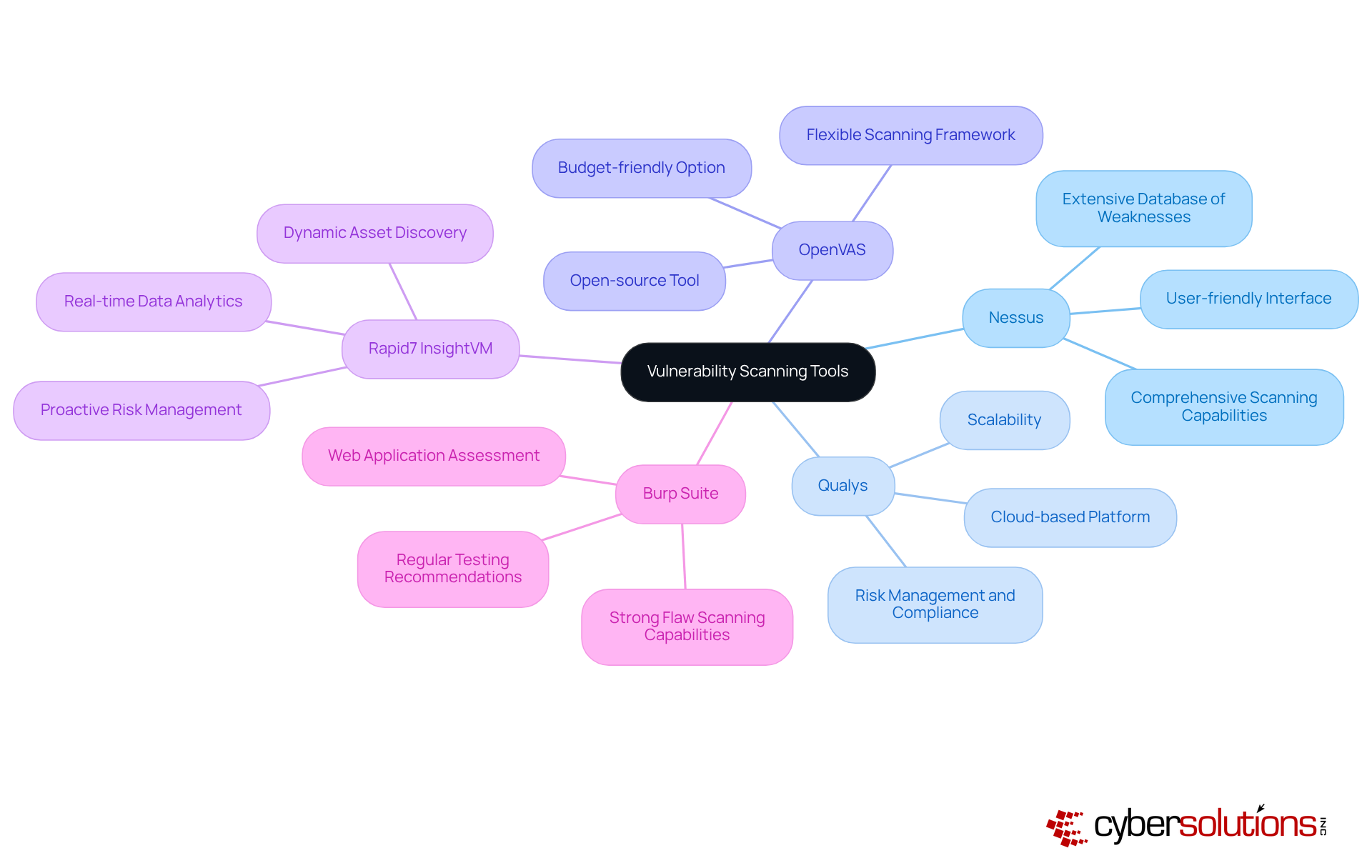
In today's digital landscape, understanding the importance of vulnerability scanning cannot be overstated. Several tools stand out for their ability to address diverse organizational needs:
Nessus: Renowned for its effectiveness, Nessus provides a user-friendly interface that simplifies the vulnerability management process. Organizations employing Nessus report high satisfaction levels, particularly due to its extensive database of weaknesses and ease of integration into existing protective frameworks. With nearly 30,000 weaknesses discovered each year, tools like Nessus are essential for timely detection and resolution.
Qualys: This cloud-based platform excels in vulnerability assessment, enabling entities to continuously monitor their security stance. Qualys is preferred for its scalability and strong reporting capabilities, which assist companies in maintaining compliance with regulatory standards. Cybersecurity specialists assert that regular use of Qualys can greatly enhance a company's ability to manage vulnerabilities efficiently.
OpenVAS: As an open-source tool, OpenVAS offers a flexible and powerful scanning framework. It is especially attractive to businesses seeking budget-friendly options without sacrificing functionality, making it a favored choice among SMEs. Regular utilization of OpenVAS can help organizations stay ahead of potential threats.
Rapid7 InsightVM: This tool combines vulnerability management with real-time data analytics, enabling proactive risk management. Organizations utilizing InsightVM benefit from its dynamic asset discovery and prioritization features, which enhance their overall protection strategy. The proactive approach facilitated by InsightVM is crucial, particularly given that data breaches can cost an average of $200,000 per incident.
Burp Suite: Focused on web application assessment, Burp Suite offers strong flaw scanning capabilities. Its ability to identify vulnerabilities in web applications makes it an essential tool for organizations prioritizing application security. Experts recommend regular testing with Burp Suite to ensure web applications remain secure against evolving threats.
Recent advancements in security scanning tools emphasize the significance of understanding vulnerabilities for effectively mitigating risks. Entities that integrate these tools into a comprehensive cybersecurity plan are better positioned to identify weaknesses and react proactively, ultimately minimizing their exposure to cyber threats. Incorporating security scanning into a broader cybersecurity framework enhances asset management, patch management, and security capabilities.
In today’s cybersecurity landscape, understanding vs is crucial, as effective requires the right tools to simulate attacks and identify vulnerabilities. Here are some essential tools:
Utilizing these tools effectively can significantly against evolving threats.
In today's digital age, the importance of cybersecurity in healthcare cannot be overstated. Combining vulnerability scanning and penetration evaluations establishes a thorough protective approach that tackles both recognized and unrecognized weaknesses. Regular vulnerability scanning helps entities identify and address known weaknesses, while penetration testing uncovers how these vulnerabilities might be exploited in real-world situations. This combined approach strengthens overall security and aligns with compliance requirements, such as HIPAA and other regulations.
Moreover, by leveraging Cyber Solutions' expertise and incident response capabilities, organizations can streamline their compliance efforts and enhance threat detection. This ensures they are well-prepared to effectively respond to incidents. In an environment where the stakes are high, the integration of these services not only fortifies defenses but also instills confidence in stakeholders regarding the organization's commitment to safeguarding sensitive information.

In today's digital landscape, the significance of cybersecurity cannot be overstated, particularly for organizations dedicated to protecting their assets. Understanding the distinction between vulnerability scanning and penetration testing is essential for establishing robust defenses against cyber threats. Vulnerability scanning identifies known weaknesses, while penetration testing simulates real-world attacks to exploit these vulnerabilities. This dual approach empowers organizations to discover potential risks and comprehend their implications in a practical context.
Key insights throughout this discussion highlight the necessity of regular assessments and the integration of both methodologies into an organization's cybersecurity strategy. From proactive risk management and compliance assurance to enhanced incident response, each method offers unique benefits that collectively contribute to a stronger security posture. Tools such as Nessus, Qualys, and Metasploit are crucial for effectively implementing these strategies, ensuring organizations remain vigilant in the face of evolving threats.
Ultimately, integrating vulnerability scanning and penetration testing transcends best practice; it is a necessity for organizations committed to safeguarding sensitive information and maintaining customer trust. As cyber threats grow in sophistication and frequency, embracing a comprehensive cybersecurity strategy that includes both methodologies empowers organizations to proactively address vulnerabilities, enhance defenses, and cultivate a culture of security awareness. Taking decisive action now can significantly mitigate risks and prepare businesses for the challenges of tomorrow.
What services does Cyber Solutions Inc. offer for penetration testing?
Cyber Solutions Inc. offers a range of penetration evaluation services, including web application analysis, network penetration assessments, and social engineering evaluations.
How does Cyber Solutions Inc. approach penetration testing?
Their methodology combines both manual evaluation and automated tools to ensure comprehensive coverage across various areas of a company's IT framework.
Why is penetration testing important for organizations?
Penetration testing helps organizations identify weaknesses in their IT systems and evaluate the potential financial consequences of these vulnerabilities, which is crucial for maintaining compliance and protecting sensitive information.
What is the difference between vulnerability scanning and penetration testing?
Vulnerability scanning is an automated process that identifies known vulnerabilities without exploiting them, while penetration testing simulates real-world attacks to exploit these vulnerabilities and provide insights into how they could be leveraged by malicious actors.
Why should organizations perform regular vulnerability scans and penetration tests?
Regular evaluations are essential for maintaining a robust protective stance against sophisticated cyberattacks, allowing organizations to address weaknesses before they can be exploited.
How can integrating risk assessment into the CI/CD pipeline benefit organizations?
Integrating risk assessment into the CI/CD pipeline ensures that security is a fundamental aspect of the development process, streamlining the identification of weaknesses and facilitating quicker remediation, thus reducing exposure time.
What sectors benefit from regular risk assessments?
Organizations in various sectors, including healthcare and finance, have reported significant enhancements in their protection frameworks through regular risk assessments.
What additional measures can organizations take to strengthen their cybersecurity defenses?
Organizations can implement network hardening strategies, conduct staff training to recognize suspicious emails, and maintain proper cybersecurity hygiene to fortify their defenses against emerging threats.