Introduction
In an era where data is increasingly regarded as the lifeblood of organizations, the stakes for C-suite leaders responsible for safeguarding sensitive information are at an all-time high. Alarming statistics reveal that two-thirds of entities experienced significant data loss in the past year, underscoring the urgent need for robust data backup strategies.
This article explores essential practices for ensuring safe data backup, examining various methods, the critical 3-2-1 strategy, and the importance of regular testing alongside suitable storage solutions.
As cyber threats continue to evolve, how can executives effectively navigate the complexities of data protection to shield their organizations from potential disaster?
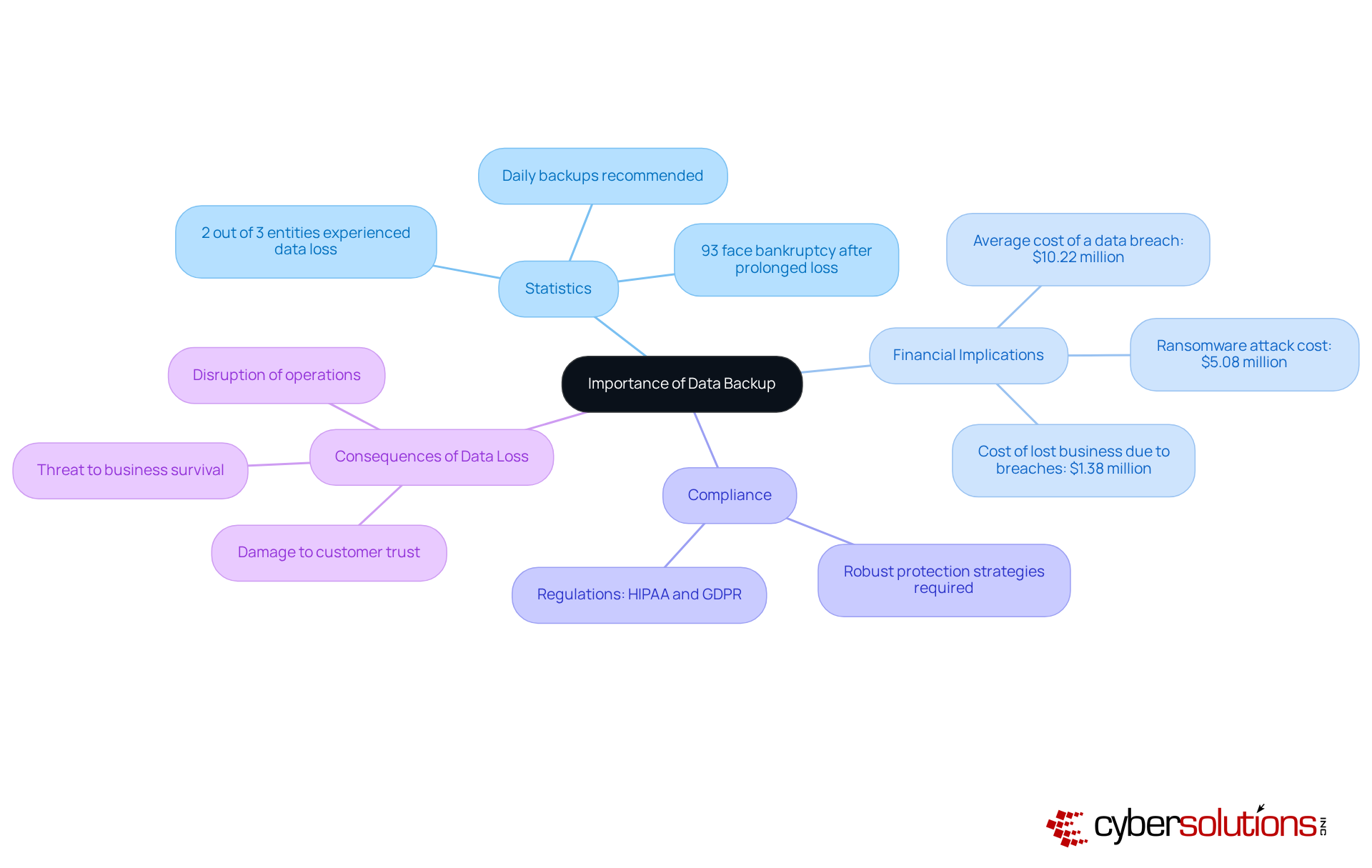
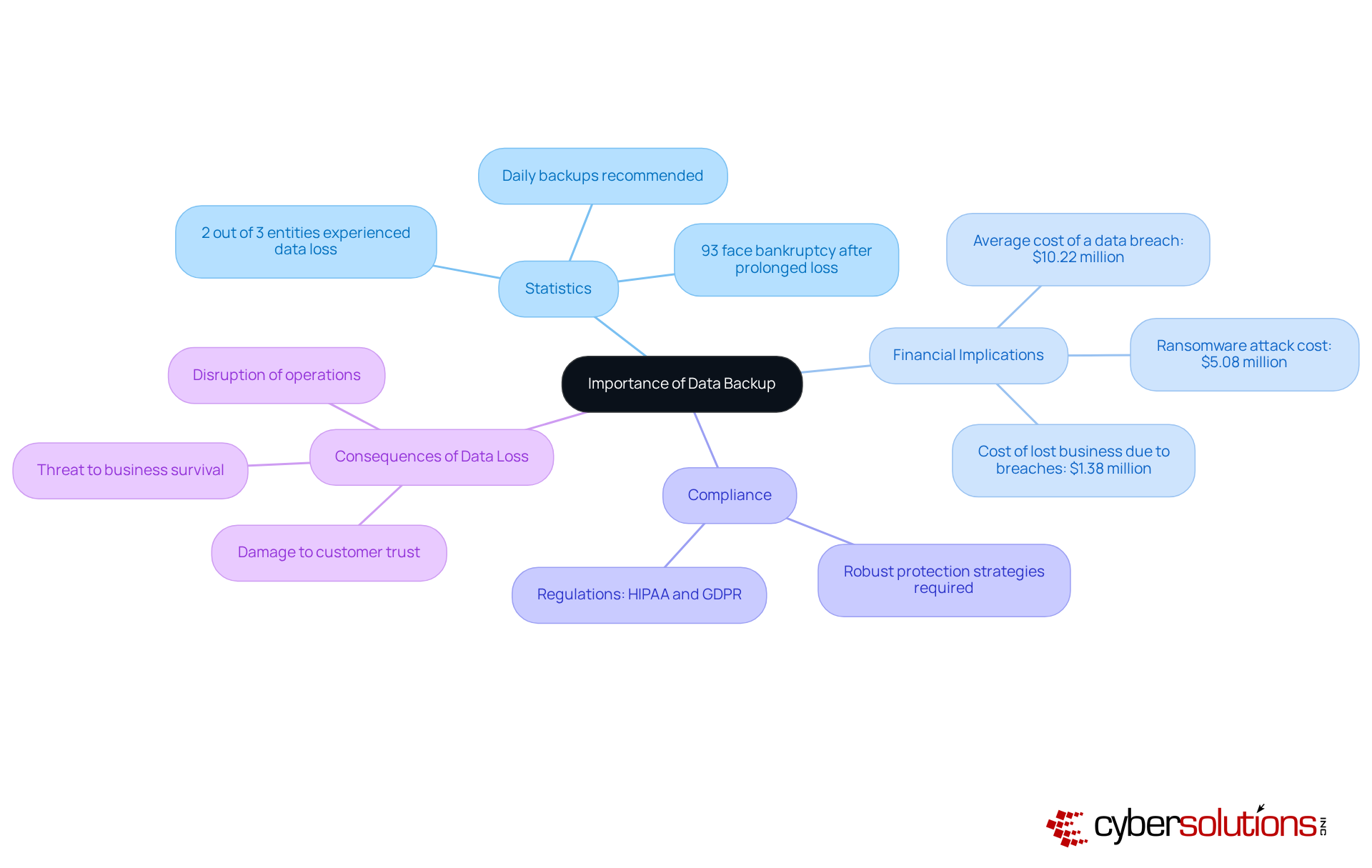
Understand the Importance of Data Backup
Safeguarding sensitive information against various threats, including cyberattacks, hardware failures, and human errors, requires a proactive approach. A recent study reveals that:
- 2 out of 3 entities experienced data breaches in the past year, underscoring the urgent need for effective backup solutions.
- For C-suite executives, the cost of data breaches; the average cost in 2025 escalated to approximately $10.22 million, demonstrating that investing in recovery solutions transcends mere technical necessity—it's a strategic financial imperative.
- Compliance with regulations such as GDPR mandates that organizations implement robust protection strategies, including regular data backups.
Cyber Solutions offers comprehensive cybersecurity services, featuring data encryption and email security, to fortify your systems and sensitive data. Notably:
- 93% of organizations that endure prolonged information loss—lasting 10 days or more—face bankruptcy within the following year, accentuating the critical importance of timely data recovery.
- By prioritizing disaster recovery plans, alongside leveraging Cyber Solutions' expertise for audit support and regulatory adherence, leaders can bolster operational resilience, protect their organization's reputation, and shield their bottom line from the costly repercussions of data loss.
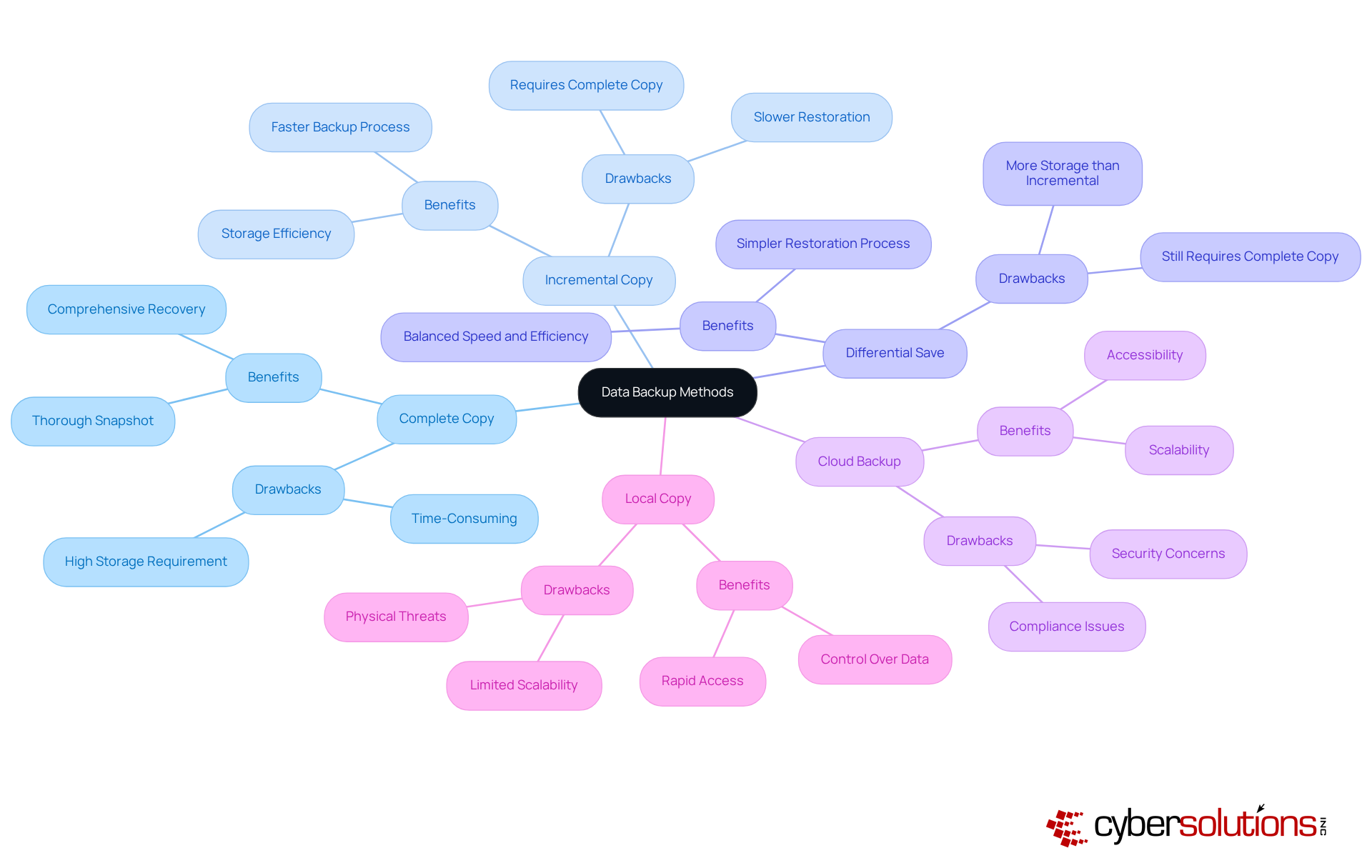
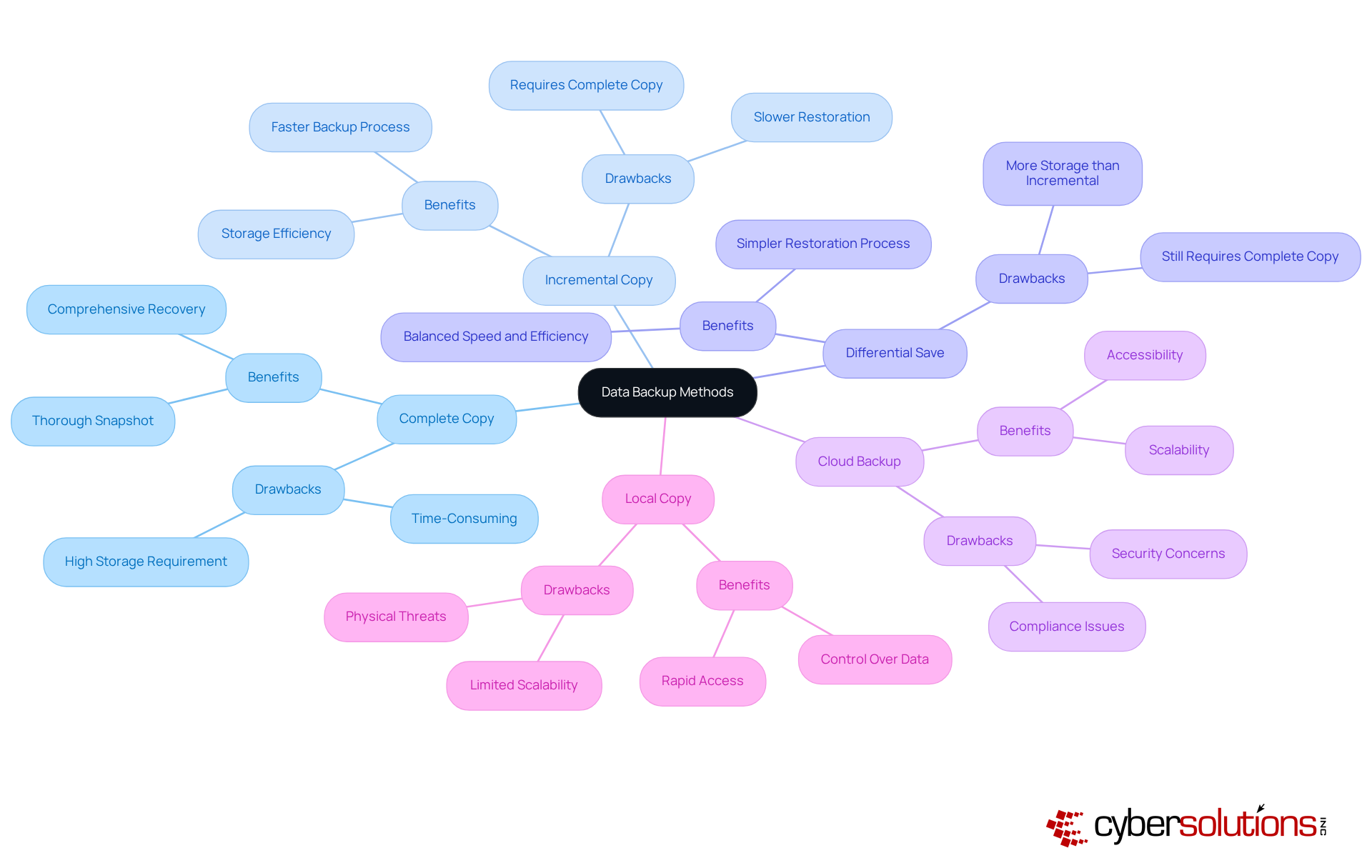
Explore Different Types of Data Backup Methods
In today's digital landscape, organizations must prioritize techniques for safe data backup to effectively safeguard their data. Various methods exist, each offering distinct benefits and drawbacks that can significantly impact data security. The primary types include:
- Complete Copy: This method involves duplicating all information to a storage site, providing a thorough snapshot of the system. While it guarantees data integrity, it can be time-consuming and requires significant storage capacity.
- Incremental Copy: This method saves only the information that has altered since the previous copy, resulting in increased speed and better storage efficiency. However, restoring data can be slower, as it requires the last complete copy along with all subsequent incremental copies.
- Differential Save: Comparable to incremental saves, differential saves record modifications made since the last complete save. This approach strikes a balance between speed and storage efficiency, needing only the last complete save and the latest differential save for restoration.
- Cloud Backup: Storing information offsite in the cloud offers scalability and accessibility, making it a preferred option among companies. However, security and compliance considerations are paramount when selecting a cloud provider, especially given that a company falls victim to a ransomware attack every 14 seconds.
- Local Copy: Keeping copies on physical devices within the entity allows for rapid access and control. However, this method may expose information to physical threats such as theft or natural disasters.
By thoroughly grasping these techniques, leaders can effectively customize their recovery plans to match their organization's particular requirements and risk appetite, ensuring robust data protection, compliance, and a secure environment.
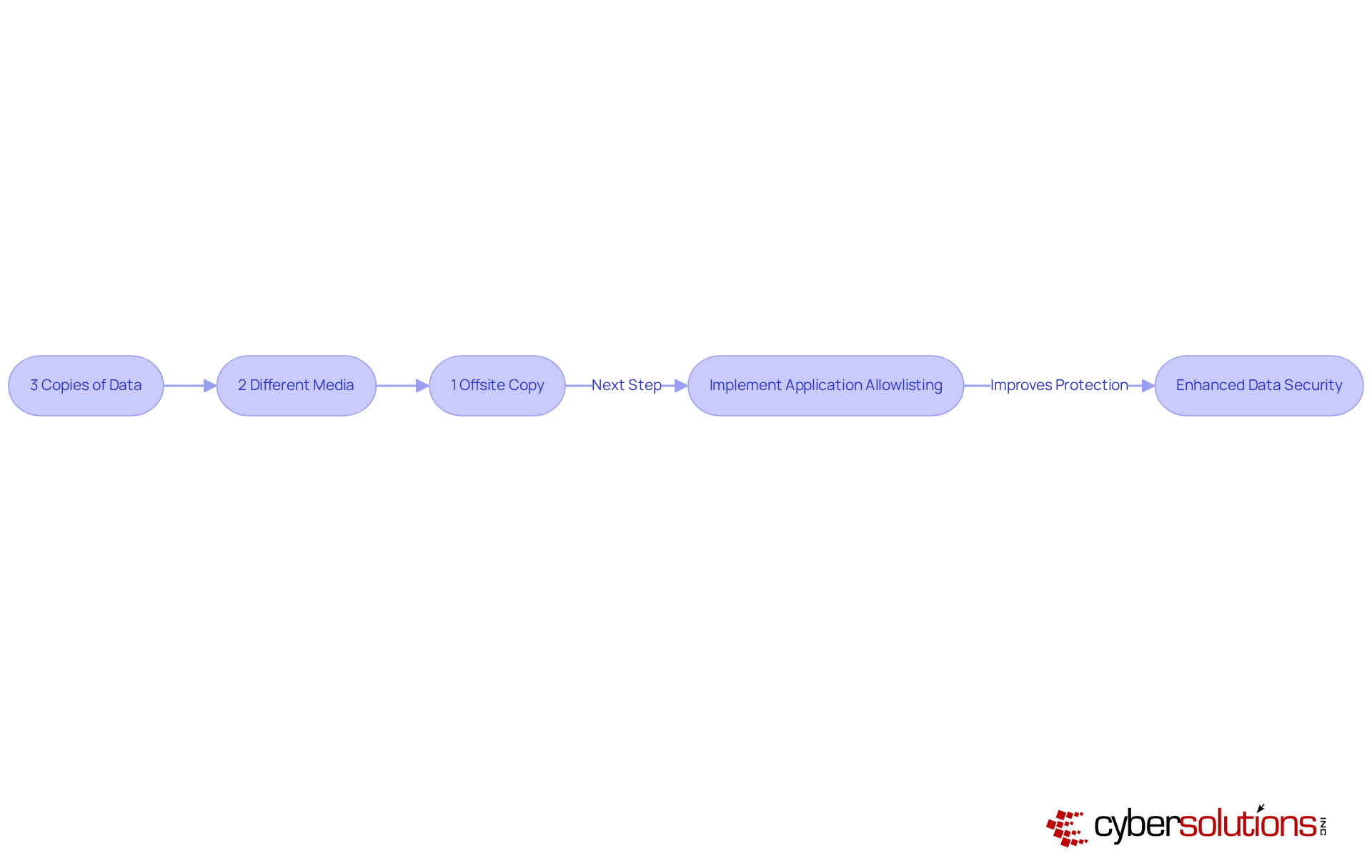
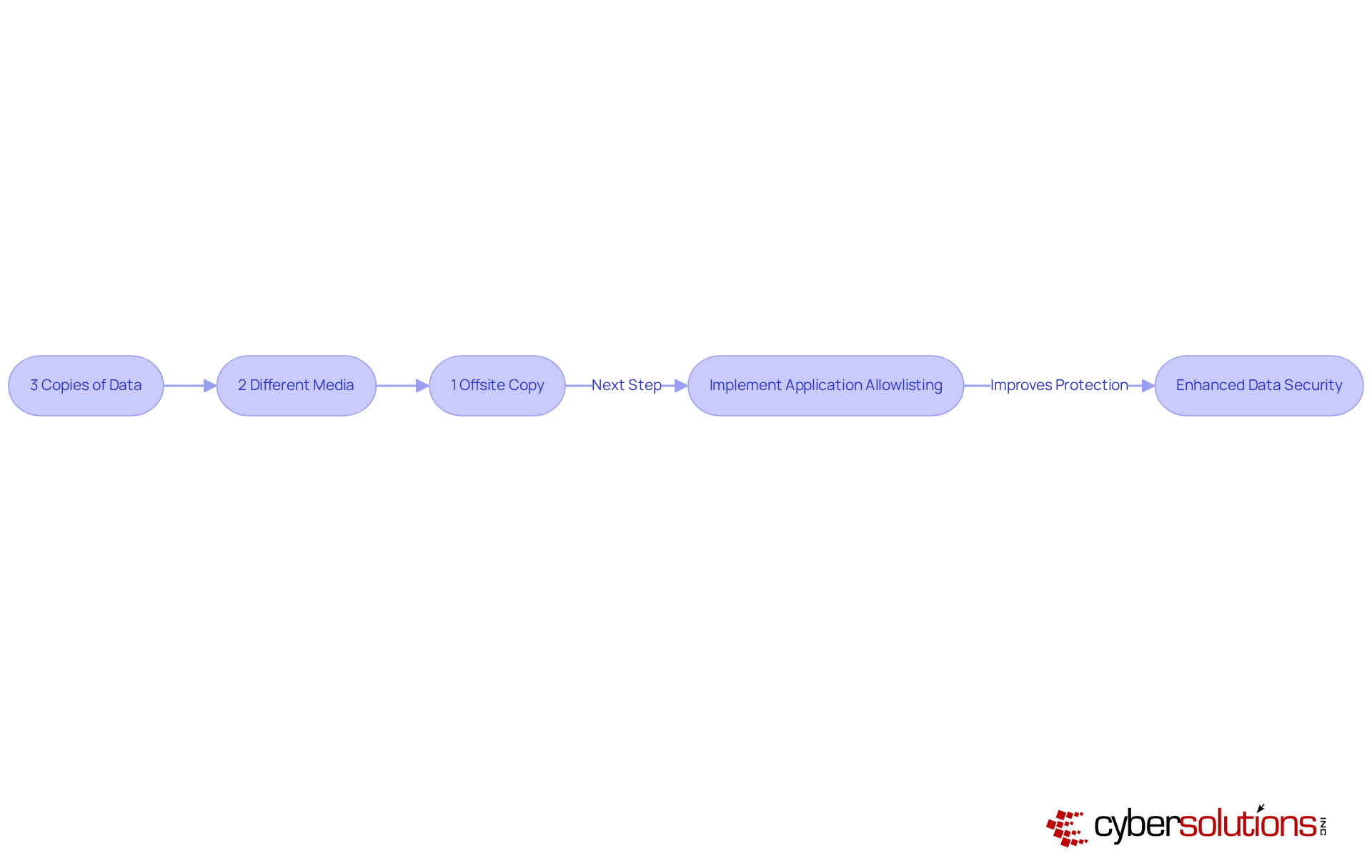
Implement the 3-2-1 Backup Strategy
The 3-2-1 Backup Strategy is a straightforward yet powerful approach to safeguarding data:
- 3 Copies of Data: Ensure you have three copies of your data: the original and two backups.
- 2 Different Media: Store these copies on at least two distinct types of media, such as external hard drives and cloud storage solutions.
- 1 Offsite Copy: Maintain one copy offsite to protect against local disasters like fires or floods.
Executing this plan greatly reduces the chance of information loss. For instance, in the case of a ransomware incident that jeopardizes local data, having an offsite copy enables recovery without major disruption. Furthermore, incorporating security measures into your backup strategy enhances this approach by proactively blocking unauthorized software from running, thus protecting your backups from malware and ransomware risks.
This strategy features continuous monitoring of application activity and centralized management of allowlists, ensuring that only approved applications can run. This not only safeguards your information but also assists organizations in meeting compliance requirements such as HIPAA, PCI-DSS, and GDPR. Organizations that embrace the 3-2-1 strategy alongside security measures can demonstrate to stakeholders their unwavering commitment to data protection and risk management.
The significance of data backup cannot be overstated, particularly as companies encounter rising dangers from cyberattacks. Expert insights highlight that without external data storage, organizations are especially susceptible to data loss, which can result in severe operational and financial repercussions. By implementing the 3-2-1 storage strategy, companies can effectively ensure a safe recovery of their essential information and respond strongly to possible threats.
Establish Regular Backup Schedules and Testing Protocols
Creating a regular recovery timetable is crucial for ensuring consistent information security. Organizations must adopt best practices:
- Frequency: The frequency of backups must be tailored to data volatility. For essential business information, daily or even hourly copies are recommended to mitigate potential losses, while less critical data may be saved weekly or monthly. This approach aligns with the 3-2-1 strategy, promoting the retention of three copies of information across two distinct media types, which ensures that one copy is stored off-site.
- Testing: Regular examination of recovery systems is essential to guarantee effective information restoration. Organizations should conduct simulated recovery scenarios to identify and address potential issues before a real disaster occurs. Statistics indicate that organizations implementing rigorous testing experience significantly higher success rates in data restoration, thereby enhancing overall resilience against data loss incidents.
- Documentation: Clear documentation of procedures and testing results is vital. This transparency not only fosters accountability but also aids communication, ensuring that all stakeholders are aware of the recovery plan's effectiveness. Furthermore, documenting the relationship between complete and differential data sets within the plan provides clarity during recovery scenarios.
- Security: Incorporating security measures into recovery plans is essential to protect information integrity and security against evolving cyber threats. Continuous monitoring ensures that suspicious activities are detected and halted before escalating into significant threats, thereby safeguarding your business from ransomware, phishing, and other malware attacks.
- Objectives: Organizations should define clear Recovery Point Objectives (RPO) and Recovery Time Objectives (RTO) for various types of information, allowing for tailored backup strategies that meet specific business needs.
By integrating these practices, organizations can significantly enhance their data resilience, ensuring readiness and preparedness for any potential data loss events. Regular testing and documentation not only improve operational efficiency but also instill confidence in the organization's ability to recover swiftly from disruptions. Moreover, having a rapid incident response plan in place, as demonstrated in recent case studies, can minimize the impact of ransomware attacks and reinforce overall cybersecurity measures.

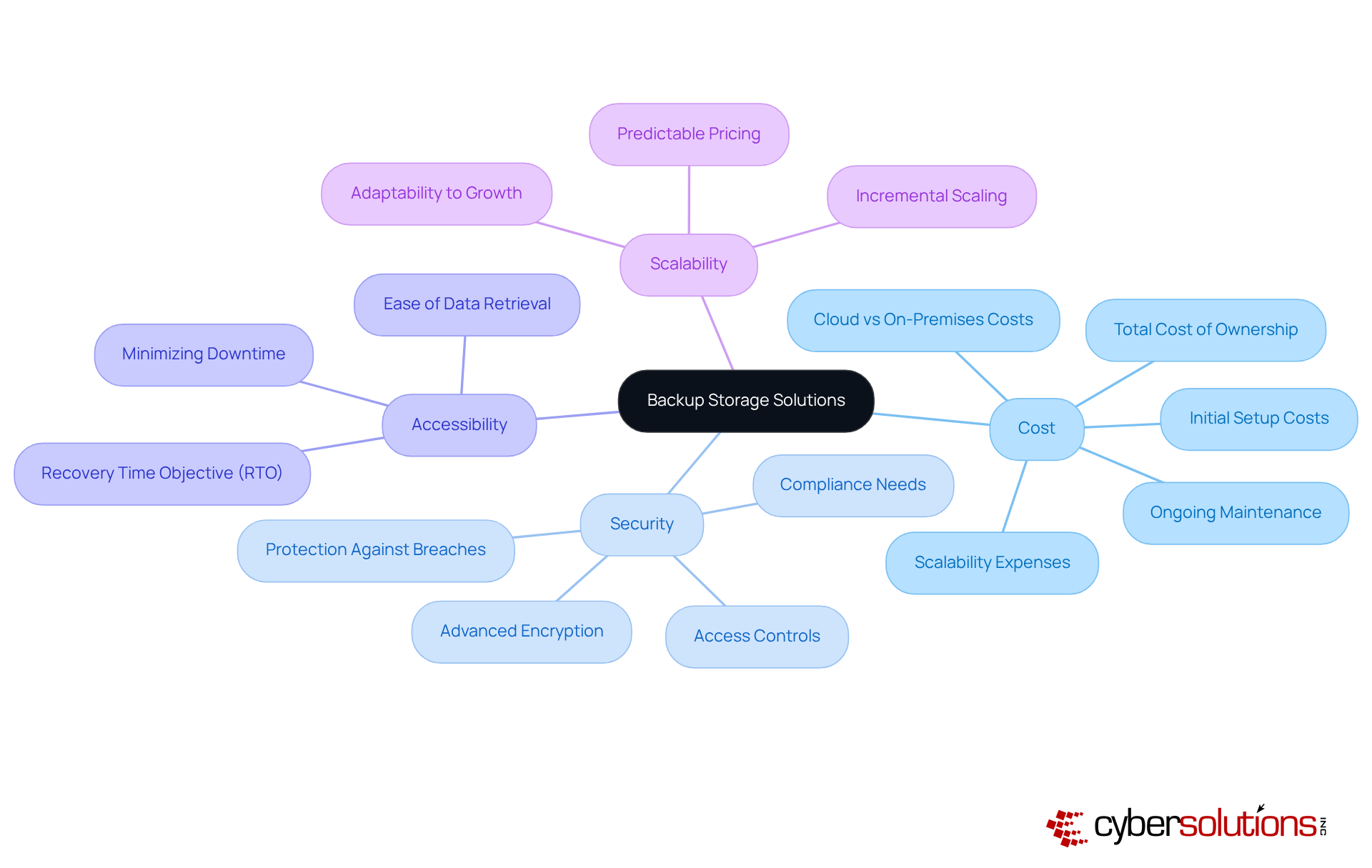
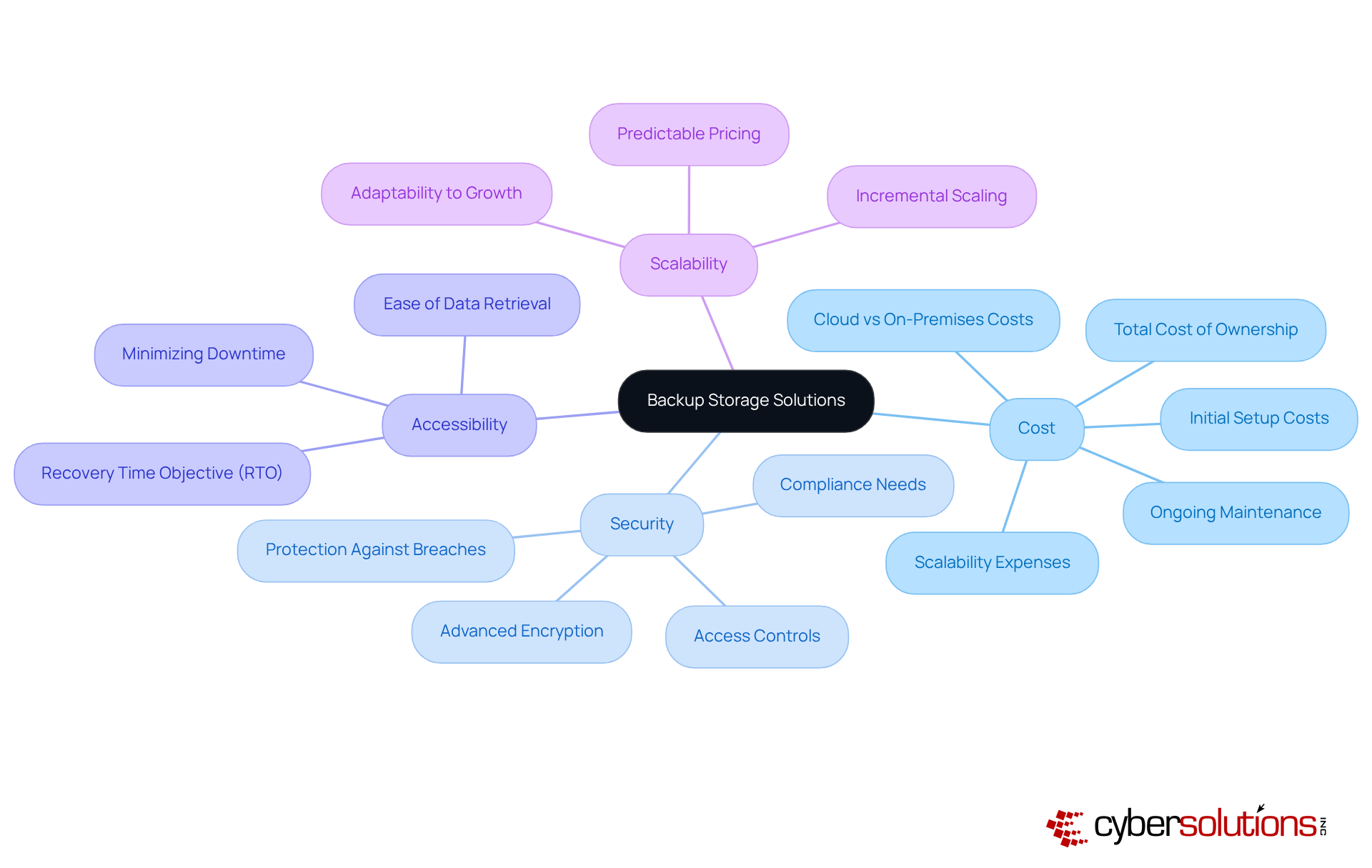
Select Appropriate Backup Storage Solutions
Selecting the right backup storage solution is imperative for organizations aiming to achieve a secure data backup strategy effectively. A thorough evaluation of several key factors is essential to ensure optimal decision-making.
- Cost: Assessing the total cost for each storage option is crucial. This includes initial setup, maintenance, and scalability expenses. For instance, while cloud backup solutions can significantly reduce annual operating costs by up to 80%, on-premises systems may incur higher cumulative costs over time due to substantial upfront investments and ongoing maintenance requirements.
- Security: In an era where cyber threats are ever-evolving, it is essential to choose storage solutions that provide robust security features. Advanced encryption and strict access controls are non-negotiable. Ensuring protection against unauthorized access and breaches is paramount.
- Accessibility: The ability to retrieve information promptly during recovery cannot be overstated. Solutions that facilitate quick access to data are vital for minimizing downtime and maintaining business continuity. For example, GitProtect.io offers a 10-minute Recovery Time Objective (RTO) for S3 storages, underscoring the significance of speed in recovery.
- Scalability: Organizations must select solutions that can adapt to their expanding information requirements. Cloud solutions, in particular, enable gradual scaling with predictable pricing, making them suitable for businesses anticipating varying information volumes.
By meticulously analyzing these factors, C-suite leaders can make strategic decisions that not only enhance their organization's data management practices but also ensure a reliable backup system while optimizing costs effectively.
Conclusion
Ensuring a secure and effective data backup strategy transcends operational necessity; it stands as a vital strategic imperative for C-suite leaders. The potential financial repercussions of data loss illuminate the critical need to prioritize robust backup solutions and recovery methods. By adopting a comprehensive approach to data protection, organizations can effectively safeguard their sensitive information from a myriad of threats, enhancing resilience and preserving their competitive edge.
The article outlines several key strategies for achieving safe data backup, such as:
- Understanding the various backup methods available
- Implementing the 3-2-1 backup strategy
- Establishing regular backup schedules
- Selecting appropriate storage solutions
Each of these elements plays a pivotal role in mitigating risks associated with data loss, underscoring the necessity for C-suite leaders to proactively engage in their data protection efforts. Moreover, the importance of testing recovery protocols and ensuring compliance with industry regulations cannot be overstated, as these practices equip organizations to adeptly respond to potential data breaches.
In a landscape rife with increasingly sophisticated cyber threats, the imperative for executives is unmistakable: prioritize data backup as an essential component of organizational strategy. By investing in effective backup solutions and cultivating a culture of data resilience, leaders can shield their organizations from the devastating impacts of data loss, ensuring not only compliance but also the long-term sustainability of their business operations. Embracing these best practices will not only fortify data security but also bolster stakeholder confidence in an organization's unwavering commitment to safeguarding its most critical assets.
Frequently Asked Questions
Why is data backup important for organizations?
Data backup is crucial for safeguarding sensitive information against threats like cyberattacks, hardware failures, and human errors. A study showed that 2 out of 3 entities experienced significant information loss in the past year, highlighting the need for effective recovery methods.
What are the financial implications of data loss for C-suite executives?
The average cost of a security breach in 2025 is projected to be around $10.22 million. This underscores that investing in recovery solutions is a strategic financial imperative, not just a technical necessity.
What regulations mandate data backup strategies?
Regulations such as HIPAA and GDPR require organizations to implement robust protection strategies, including safe data backup.
What are the consequences of prolonged information loss?
Organizations that experience information loss lasting 10 days or more face a 93% risk of bankruptcy within the following year, emphasizing the importance of effective recovery strategies.
What types of data backup methods are available?
The primary types of data backup methods include: Complete Copy: Duplicates all information, ensuring comprehensive recovery but requiring significant storage and time. Incremental Copy: Saves only changed information since the last copy, offering speed and storage efficiency, but slower restoration. Differential Save: Records changes since the last complete save, balancing speed and storage efficiency for restoration. Cloud Backup: Stores information offsite in the cloud, providing scalability and accessibility, with security considerations being crucial. Local Copy: Keeps copies on physical devices for rapid access, but may expose data to physical threats.
How can organizations enhance their data backup strategies?
Organizations can enhance their data backup strategies by prioritizing data preservation, routinely testing disaster recovery plans, and leveraging services like Compliance as a Service (CaaS) for audit support and regulatory adherence. This helps bolster operational resilience and protect against the costly repercussions of data loss.
List of Sources
- Understand the Importance of Data Backup
- Why Businesses Needsa Backup and Disaster Recovery Strategy| Northern Technologies Group (https://ntgit.com/why-every-business-needs-a-smart-backup-and-disaster-recovery-strategy-in-2025)
- secureframe.com (https://secureframe.com/blog/data-breach-statistics)
- invenioit.com (https://invenioit.com/continuity/data-loss-statistics?srsltid=AfmBOoqTTunrh0Y5JIPH2fTeQOg_ar9DHPVKLYxMagzyIGTeqYhCjrC9)
- invenioit.com (https://invenioit.com/continuity/data-loss-statistics?srsltid=AfmBOoqz-irW_7i5oKXyShDAu6xaYKWpSz4dz6luzYVkl9v0V6L68ITu)
- Explore Different Types of Data Backup Methods
- solutionsreview.com (https://solutionsreview.com/backup-disaster-recovery/world-backup-day-quotes-from-experts-for-2025)
- Implement the 3-2-1 Backup Strategy
- solutionsreview.com (https://solutionsreview.com/backup-disaster-recovery/world-backup-day-quotes-from-experts-for-2025)
- starwindsoftware.com (https://starwindsoftware.com/blog/3-2-1-backup-rule-implementation)
- Establish Regular Backup Schedules and Testing Protocols
- nova-communications.com (https://nova-communications.com/blog?p=the-critical-importance-of-data-backup-251002)
- Data Backup: Best Practices for 2025 (https://ais-now.com/blog/data-backup-best-practices-2024)
- cloudvara.com (https://cloudvara.com/database-backup-strategies)
- Data Backup Best Practices & Backup Strategy | ConnectWise (https://connectwise.com/blog/backup-strategy-best-practices)
- blog.thriveon.net (https://blog.thriveon.net/the-importance-of-regular-data-backups-cybersecurity)
- Select Appropriate Backup Storage Solutions
- 5 Enterprise Backup Solutions to Consider in 2025 | Storware (https://storware.eu/blog/5-enterprise-backup-solutions-to-consider-in-2025)
- gitprotect.io (https://gitprotect.io/blog/data-protection-and-backup-predictions-for-2025-and-beyond)
- techtarget.com (https://techtarget.com/searchdatabackup/feature/9-backup-as-a-service-BaaS-providers-in-2025)
- essentialdesigns.net (https://essentialdesigns.net/news/on-premises-vs-cloud-backup-cost-comparison)
- solutionsreview.com (https://solutionsreview.com/backup-disaster-recovery/storage-and-data-protection-news-for-the-week-of-september-5-updates-from-druva-varonis-zoom-backup-more)