Introduction
In today's world, where cyber threats are more prevalent than ever, the importance of Security Information and Event Management (SIEM) systems cannot be overstated, especially for organizations in the healthcare sector. These robust tools not only enable real-time monitoring and threat detection but also help ensure compliance with stringent regulations, acting as a vital line of defense against ever-evolving cyber risks.
However, a pressing question arises: how can organizations truly maximize the effectiveness of their SIEM deployments to enhance their cybersecurity posture? This article explores best practices for leveraging SIEM events, providing insights that can transform security strategies and strengthen defenses against increasingly sophisticated threats. By understanding the unique challenges faced by healthcare organizations, we can better appreciate the critical role that SIEM systems play in safeguarding sensitive information and maintaining trust in healthcare services.
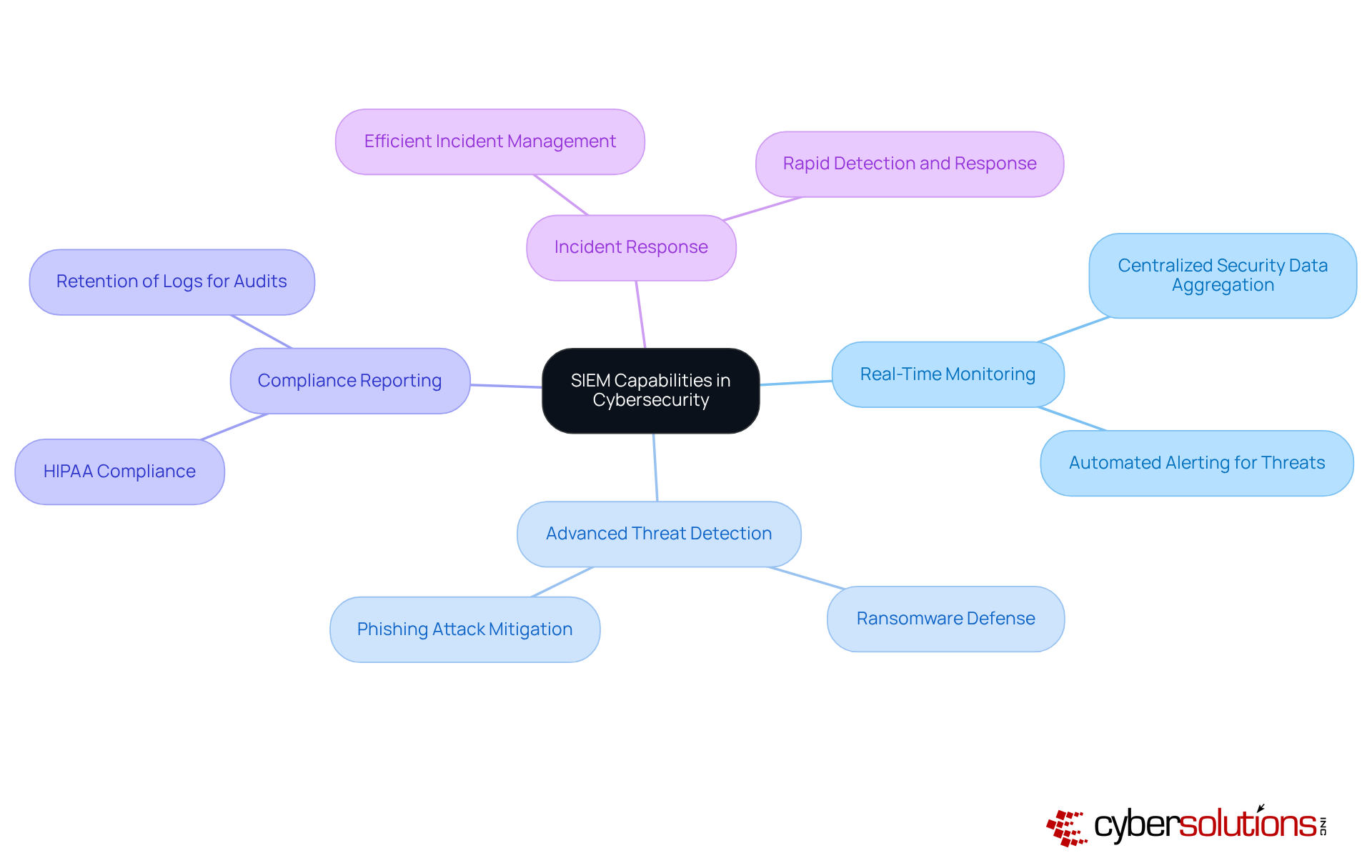
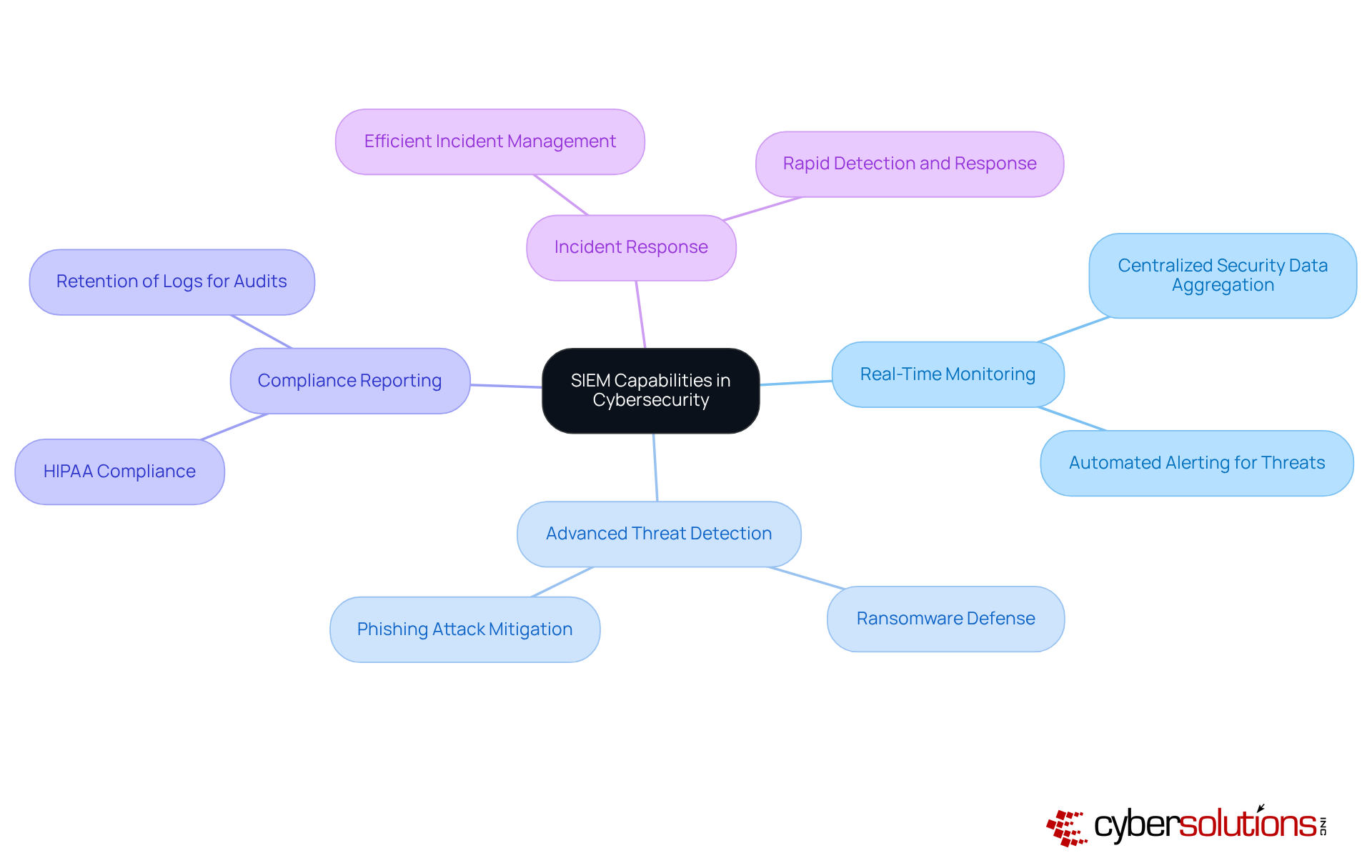
Understand SIEM Capabilities and Their Role in Cybersecurity
In today's digital age, cybersecurity is not just an option; it's a necessity, especially in healthcare. SIEM events play a crucial role in this landscape, acting as a centralized hub for aggregating and analyzing security data from various sources. These systems empower organizations with capabilities like threat detection, incident response, compliance reporting, and efficient data management.
Consider the implications for healthcare CFOs: with Cyber Solutions' monitoring and alerts, organizations can swiftly identify anomalies and potential vulnerabilities. This proactive approach is vital in defending against threats such as data breaches. By leveraging these features, healthcare institutions can significantly bolster their security posture while ensuring they meet operational objectives. For instance, they can streamline incident management, all while enhancing their overall security framework.
Moreover, continuous monitoring is essential for safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). This is not just about regulatory adherence; it’s about maintaining eligibility for lucrative government contracts. As cyber risks evolve, the integration of SIEM events becomes increasingly critical for risk management. Ultimately, this enhances security measures in a complex digital environment, allowing healthcare entities to focus on what they do best - providing quality care.
Leverage the Benefits of SIEM Solutions for Enhanced Security
Deploying security information and event management solutions is not just beneficial; it’s essential for enhancing a company’s security posture. In an era where cyber threats are increasingly sophisticated, organizations must prioritize their defenses. Here’s how these solutions can transform your cybersecurity posture:
- SIEM solutions allow Security Information and Event Management systems to continuously monitor network activity, enabling rapid identification of potential threats before they escalate into serious incidents. This proactive approach is crucial; organizations that invest in early detection mechanisms can safeguard their revenue and uphold trust.
- SIEM solutions By consolidating information from multiple sources, solutions simplify adherence to regulations like GDPR and HIPAA, alleviating the workload on compliance teams. With only 34.4% of entities fully compliant with PCI DSS, effective deployment of these solutions is vital for meeting regulatory obligations.
- SIEM solutions enable faster responses to incidents by supplying security teams with actionable insights and automated notifications, allowing for prompt threat mitigation. For instance, organizations that have embraced comprehensive strategies report significantly improved recovery times, with some achieving a 30% reduction in time after implementing these solutions.
- SIEM solutions By preventing breaches and minimizing downtime, SIEM solutions can result in substantial cost savings, making them a wise investment for organizations of all sizes. The average cost of a data breach in 2024 is projected to reach $4.35 million, highlighting the financial necessity for robust cybersecurity measures.
In summary, utilizing SIEM solutions not only enhances your security stance but also promotes operational efficiency, making them indispensable in today’s threat landscape.

Implement Best Practices for Effective SIEM Deployment
To ensure a successful deployment, organizations must prioritize best practices that enhance their security posture:
- Define Clear Use Cases: Identifying specific use cases that align with security objectives is crucial. This approach customizes the setup to meet distinct requirements, ensuring that the deployment is both relevant and effective.
- Prioritize Log Sources: Start by collecting logs from critical systems and applications. This prioritization guarantees that the most vital data is monitored and analyzed, allowing organizations to focus their resources where they matter most.
- Tune Alerts to Reduce False Positives: Regularly adjusting alert thresholds and parameters is essential to minimize false positives. Overwhelming teams with unnecessary alerts can lead to alert fatigue, undermining the effectiveness of the SIEM system.
- Consistently Assess and Revise SIEM Settings: The risk environment is ever-changing, and so should be the SIEM settings. Regular reviews ensure that the system remains effective against emerging threats, adapting to new challenges as they arise.
- Provide Comprehensive Training: A well-trained staff is vital. Ensuring that personnel understand the capabilities of the SIEM system and can respond to alerts appropriately enhances the overall security framework.
By adhering to these best practices, organizations can significantly improve the efficiency of their management solutions for SIEM events, fortifying their defenses against evolving threats.

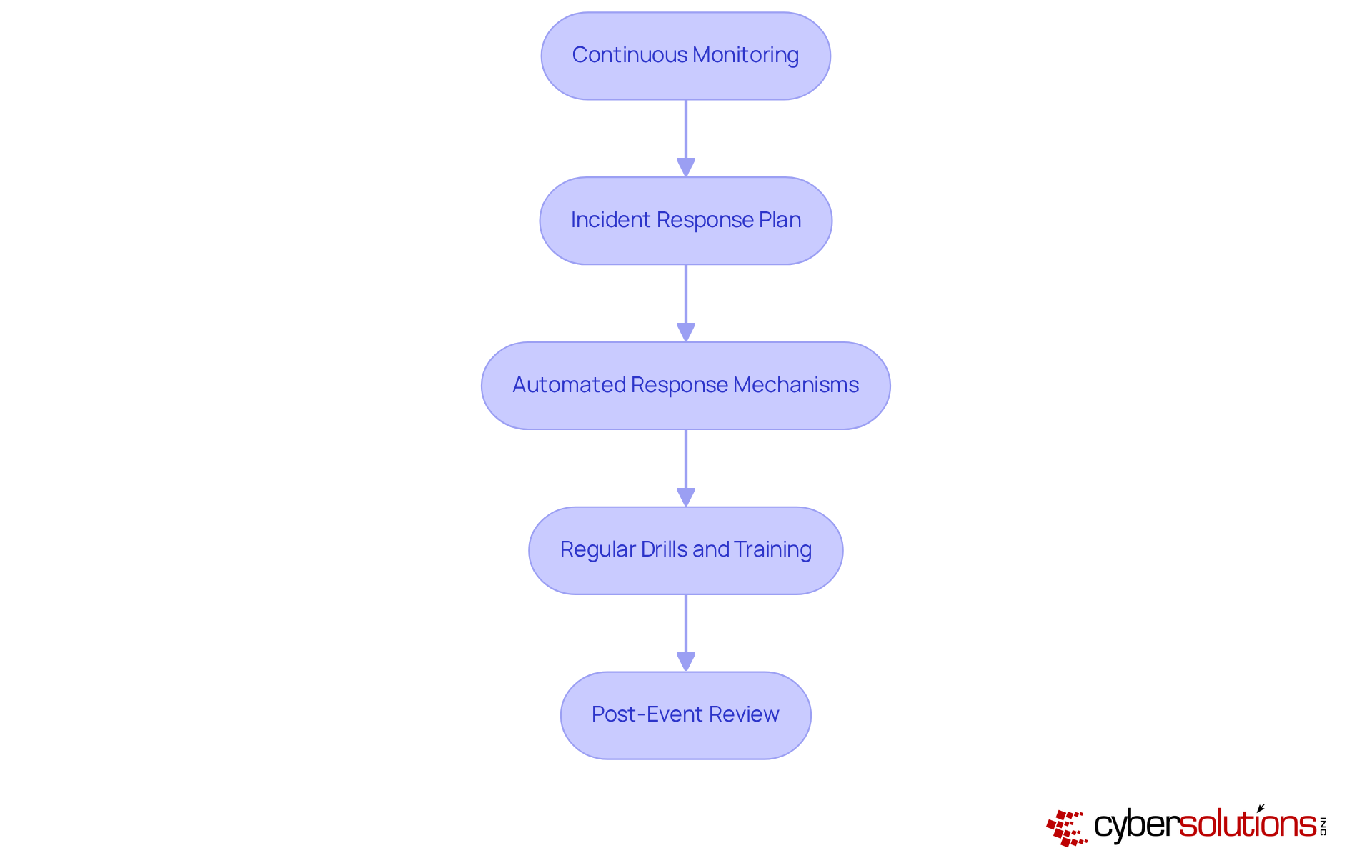
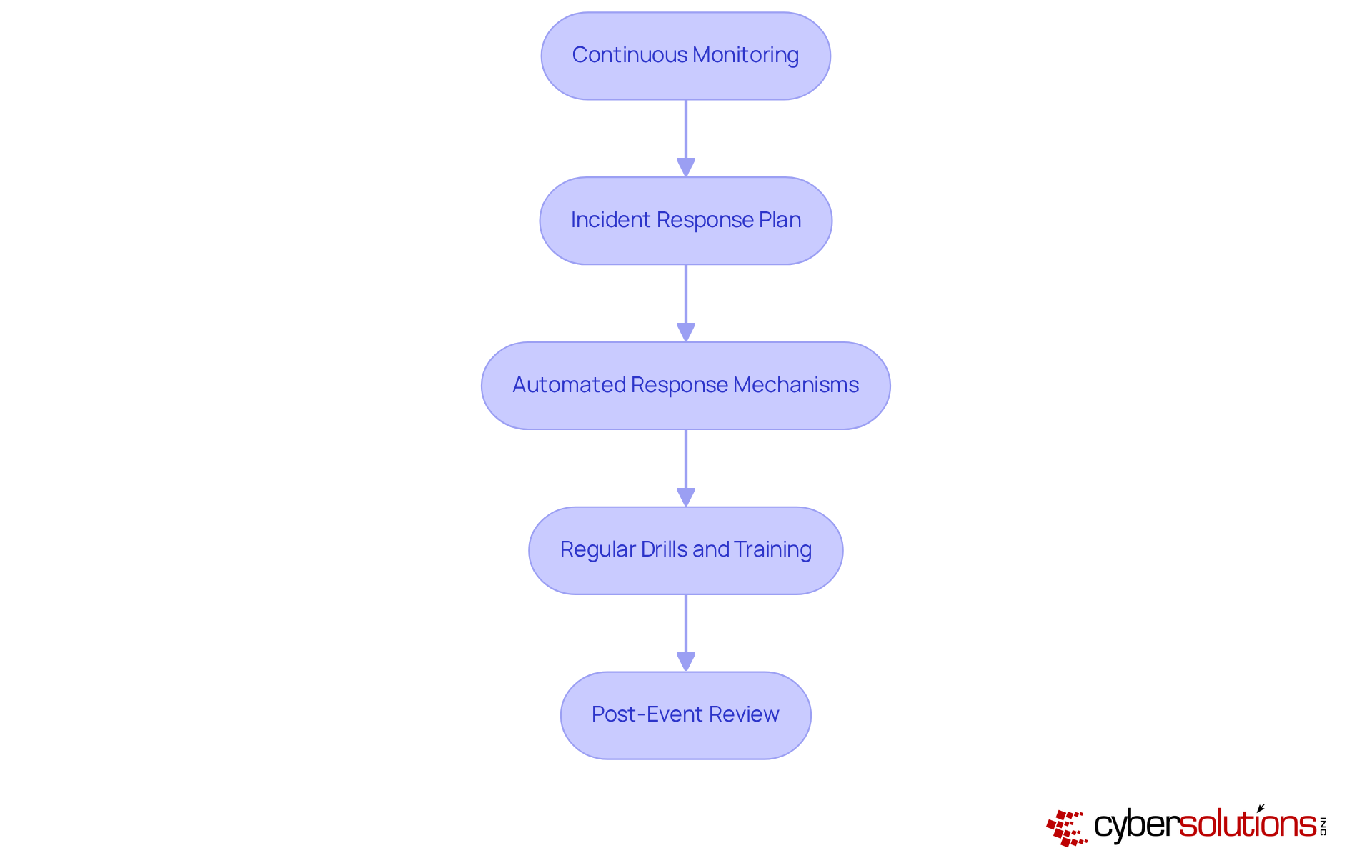
Establish Continuous Monitoring and Incident Response Protocols
In today's digital landscape, monitoring and effective incident response are not just important; they are essential for a robust cybersecurity strategy. Organizations must adopt the following protocols to safeguard their operations:
- Utilize SIEM solutions to continuously analyze network traffic and system logs for suspicious activities. Cyber Solutions provides round-the-clock monitoring, identifying anomalies and potential vulnerabilities. This proactive approach enables early risk identification and prompt measures to prevent downtime or breaches. Tailored access controls ensure that only authorized users can access sensitive information.
- Develop a response plan that clearly defines roles, responsibilities, and procedures for addressing incidents. Regular testing and revisions of this plan are crucial to ensure its effectiveness and alignment with evolving risks. Insights from case studies can enhance the plan's relevance and applicability.
- Integrate automated response capabilities that can act immediately upon detecting threats, such as isolating affected systems or blocking malicious IP addresses. This is vital for minimizing damage from attacks like ransomware and phishing, supported by advanced threat intelligence.
- Conduct frequent emergency response exercises to ensure all team members are well-prepared for their roles during real incidents. Organizations that engage in regular training can improve response times by up to 35%, significantly boosting overall cybersecurity confidence.
- After any incident, perform a thorough examination to assess the events, evaluate response effectiveness, and identify areas for improvement in the response plan. This reflective practice is essential for the continuous enhancement of security protocols and can be informed by previous case studies to refine strategies.
By implementing these protocols, organizations can strengthen their resilience against threats and ensure a swift, effective response to incidents, ultimately protecting their operations and reputation.
Conclusion
Maximizing the effectiveness of Security Information and Event Management (SIEM) systems is not just important; it’s essential for organizations striving to bolster their cybersecurity frameworks. In a world where cyber threats are increasingly sophisticated, understanding and leveraging SIEM capabilities allows organizations to proactively defend against emerging threats while ensuring compliance with regulatory standards. This proactive approach not only secures sensitive data but also fortifies the overall resilience of the organization.
To effectively deploy SIEM systems, organizations should focus on several key strategies:
- Defining clear use cases is crucial.
- Prioritizing log sources and continuously assessing system settings can streamline operations, reduce false positives, and enhance incident response capabilities.
- Continuous monitoring and automated response mechanisms play a vital role in swiftly addressing potential security incidents, ensuring that organizations remain one step ahead of cyber adversaries.
The time to act is now. By adopting these strategies, organizations can significantly improve their cybersecurity posture and foster operational efficiency. Investing in robust SIEM solutions is a strategic move that not only safeguards valuable assets but also maintains trust in an ever-evolving digital environment. The question is: can your organization afford to wait?
Frequently Asked Questions
What is the role of SIEM in cybersecurity?
SIEM acts as a centralized hub for aggregating and analyzing security data from various sources, enabling organizations to monitor security events in real-time, detect advanced threats, report on compliance, and respond efficiently to incidents.
Why is cybersecurity particularly important in healthcare?
Cybersecurity is crucial in healthcare to protect sensitive data, ensure compliance with regulations like HIPAA, and defend against threats such as ransomware and phishing attacks, which can compromise patient information and organizational integrity.
How can SIEM systems benefit healthcare organizations?
SIEM systems help healthcare organizations by providing 24/7 network monitoring and alerts, allowing for the swift identification of anomalies and vulnerabilities, thus enhancing their overall security posture and operational efficiency.
What compliance requirements do SIEM systems help healthcare organizations meet?
SIEM systems assist healthcare organizations in efficiently satisfying HIPAA compliance requirements and safeguarding Controlled Unclassified Information (CUI) and Federal Contract Information (FCI), which are essential for maintaining eligibility for government contracts.
How do SIEM capabilities enhance organizational resilience?
By integrating SIEM events, healthcare entities can better protect sensitive data, ensure regulatory compliance, and respond effectively to evolving cyber risks, allowing them to focus on providing quality care.
List of Sources
- Understand SIEM Capabilities and Their Role in Cybersecurity
- 20 Quotes Proving The Need for Security Integrations (https://synqly.com/moving-from-ok-to-best-in-class-20-quotes-from-experts-proving-the-need-for-security-integrations)
- expertinsights.com (https://expertinsights.com/security-operations/siem-market-overview-key-stats-and-insights)
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Security Information and Event Management (SIEM) (https://infosecurity-magazine.com/security-information-and-event-management-(siem))
- choicesolutions.com (https://choicesolutions.com/news/how-siem-strengthens-security-compliance-in-it-environments)
- Leverage the Benefits of SIEM Solutions for Enhanced Security
- connectwise.com (https://connectwise.com/blog/best-siem-software-solutions)
- 110 Top Cybersecurity Statistics, Facts, and Trends for 2026 (https://acecloudhosting.com/blog/top-cybersecurity-stats-and-facts)
- secureframe.com (https://secureframe.com/blog/data-breach-statistics)
- SIEM — Latest News, Reports & Analysis | The Hacker News (https://thehackernews.com/search/label/SIEM)
- Establish Continuous Monitoring and Incident Response Protocols
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- NIST Releases Updated Incident Response Guidance Under Its Cybersecurity Framework (https://morganlewis.com/blogs/sourcingatmorganlewis/2025/06/nist-releases-updated-incident-response-guidance-under-its-cybersecurity-framework)
- Cybersecurity’s First Responders: Managing Incident Response | Harvard Extension School (https://extension.harvard.edu/blog/cybersecuritys-first-responders-managing-incident-response)
- CISA Shares Lessons Learned from an Incident Response Engagement | CISA (https://cisa.gov/news-events/cybersecurity-advisories/aa25-266a)
- How to Create a Cybersecurity Incident Response Plan That Works (https://hyperproof.io/resource/cybersecurity-incident-response-plan)