
In today’s digital landscape, where cyber threats are evolving at an alarming rate, the importance of managed security companies cannot be overstated. These specialized firms provide tailored cybersecurity solutions that not only safeguard sensitive information but also allow organizations to concentrate on their core operations, free from the complexities of managing intricate security systems. As cybercrime continues to grow, businesses face a pressing question: how can they ensure robust protection against an ever-expanding array of threats?
Understanding the significance and key features of managed security services is crucial for organizations looking to strengthen their defenses and maintain compliance in this challenging environment. By leveraging expert cybersecurity solutions, businesses can effectively navigate the complexities of today’s threats, ensuring they remain resilient and secure.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for businesses that handle sensitive information. A managed security company specializes in the outsourced monitoring and management of security systems, providing a comprehensive suite of cybersecurity solutions tailored to meet the unique challenges organizations face. These services include:
All critical in safeguarding digital assets against evolving threats.
One of the most vital components of these services is threat detection. This proactive measure prevents malware and unauthorized software from executing, effectively reducing the attack surface and minimizing vulnerabilities. By leveraging advanced technologies such as firewalls, intrusion detection systems, and secure access controls - along with skilled personnel, firms like Cyber Solutions empower organizations to protect their digital assets while ensuring compliance with industry regulations like HIPAA, PCI-DSS, and GDPR.
Outsourcing cybersecurity allows companies to concentrate on their core operations without the burden of managing complex protective systems in-house. Managed security providers play a crucial role in this model, providing ongoing monitoring, proactive risk management, and customized compliance strategies. These elements are essential for maintaining a robust security posture in an ever-changing digital environment.
As cyber threats continue to evolve, the need for expert guidance and support becomes increasingly clear. Are you prepared to face these challenges head-on? With the right MSSP by your side, you can mitigate risks and focus on what truly matters - your business.
In the current landscape, where cyber threats are increasingly sophisticated and pervasive, the significance of a managed security company cannot be overstated. Organizations face a myriad of challenges, from data breaches to navigating the complexities of compliance with stringent regulations like GDPR and HIPAA. Managed security companies provide crucial support through continuous 24/7 monitoring, rapid incident response, and expert guidance on best practices. A well-structured response plan and security protocols are essential for organizational resilience.
For instance, Cyber Solutions demonstrated the power of managed security by restoring 4,500 endpoints after a ransomware attack, ensuring healthcare continuity and enhancing protective measures to safeguard patient data. This not only mitigates risks but also fortifies an organization's overall defensive posture, making it a vital component of modern business strategy. As reliance on digital operations grows, the demand for managed security solutions from a trusted provider is surging, positioning these providers as indispensable allies in the ongoing battle against cybercrime.
In 2023, the average cost of a data breach reached a staggering $9.36 million, underscoring the financial impact of cyber threats. Moreover, nearly 50% of all cyberattacks target small-to-medium enterprises (SMEs), highlighting the critical need for a managed security provider that offers tailored protection solutions for these organizations. Companies that leverage resources from a managed security provider, including Cyber Solutions' robust firewall and network defenses, report increased operational efficiency, allowing them to focus on core operations while ensuring compliance and safety.
Additionally, managed security services provide SMBs with access to enterprise-level compliance expertise, streamlining the process and safeguarding against potential penalties. Are you ready to fortify your organization against the evolving cyber threat landscape?

Cybersecurity is no longer just an IT concern; it’s a fundamental business necessity that demands immediate attention. The development of managed protection offerings (MSS) began in the early 2000s, as companies recognized the need to delegate IT functions to focus on their core business activities. Initially, these offerings provided basic IT support. However, as the industry evolved, the demand for specialized protective services surged. High-profile incidents, such as the 2007 data breach at TJX Companies and the 2013 Target breach, underscored vulnerabilities and highlighted the urgent need for enhanced security measures, prompting organizations to seek more comprehensive solutions.
The rise of cloud computing and the rapid spread of mobile devices have only intensified this trend. As businesses transitioned to cloud environments, they faced new security challenges that necessitated the enhancement of security protocols. Today, MSS encompasses a wide range of solutions, including:
These reflect the industry's ongoing adaptation to an ever-changing threat landscape.
A cornerstone of these services is threat intelligence, which enables real-time detection of anomalies and potential vulnerabilities. With immediate alerts and insights, organizations can act swiftly to prevent downtime or breaches, effectively shielding themselves from ransomware, phishing, and other malware attacks. Moreover, implementing tailored access controls ensures that only authorized personnel can access sensitive information, further fortifying security.
The MSS market is poised for significant growth, with projections indicating an increase from USD 39.47 billion in 2025 to USD 66.83 billion by 2030, at a compound annual growth rate (CAGR) of 11.1%. This expansion is driven by the escalating complexity of cyber threats and the critical need for continuous monitoring and rapid incident response. As organizations increasingly recognize the importance of cybersecurity in their operational strategy, the demand for services provided by a managed security company continues to rise. This positions MSS providers as essential partners in safeguarding sensitive information and ensuring compliance.

In today's digital landscape, the importance of cybersecurity cannot be overstated, especially in healthcare. Managed security companies distinguish themselves from traditional IT service providers by offering several essential features that address the unique challenges faced by organizations in this sector.
These traits empower a managed security company to deliver solutions tailored to the unique needs of their clients, ultimately enhancing their resilience against cyber threats.

In today's digital landscape, cybersecurity is not just an option; it's a necessity, especially in healthcare and finance. Consider this: a healthcare organization recently faced a ransomware attack that threatened sensitive patient data. By collaborating with a managed security company, they developed a robust plan that included real-time monitoring and threat detection. This proactive approach allowed them to quickly contain the attack, minimizing data loss and ensuring patient safety.
Similarly, in the financial sector, a leading institution leveraged a managed security provider to enhance its compliance framework. The provider performed regular assessments and audits, effectively pinpointing and addressing potential weaknesses before they could be exploited. This strategy not only protected sensitive financial information but also bolstered the institution's overall security posture.
The urgency of these measures is underscored by alarming statistics:
These examples highlight the critical role of a managed security service in defending organizations against cyber threats and ensuring compliance with regulatory standards.
As we navigate this complex landscape, it's clear that investing in managed protection services is not just a smart move - it's essential for safeguarding your organization’s future.

In today's digital landscape, cybersecurity isn't just an IT concern; it's a fundamental business necessity, especially in healthcare. As organizations face increasingly sophisticated cyber threats, the role of managed security companies has become pivotal. These partners provide essential services like:
This allows businesses to concentrate on their core operations while effectively navigating the complexities of a constantly evolving threat environment.
The importance of 24/7 monitoring and the integration of advanced technologies cannot be overstated. With the financial and reputational risks associated with cyberattacks on the rise, healthcare organizations must recognize that investing in managed security services is not merely a choice; it's a critical step toward resilience. The evolution of these services reflects a growing acknowledgment of cybersecurity as a vital component of business strategy, adapting to meet the unique challenges faced by various sectors, particularly healthcare and finance.
Consider this: how prepared is your organization to handle a cyber incident? Embracing a proactive cybersecurity strategy through a trusted managed security provider not only fortifies defenses against today's sophisticated threats but also ensures compliance with stringent regulations. The time to act is now-safeguarding the future of your organization depends on it.
What is a managed security company?
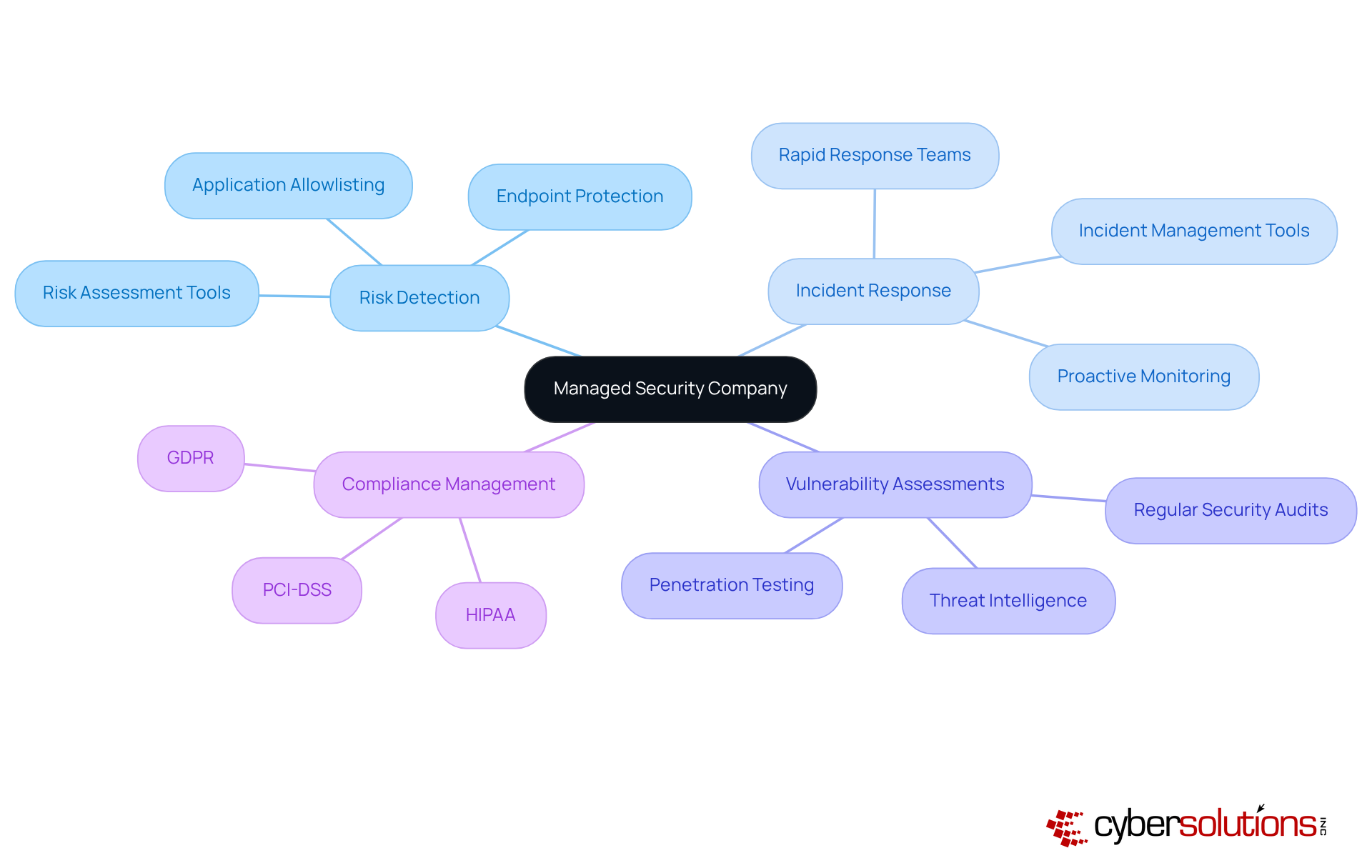
A managed security company specializes in the outsourced monitoring and management of security systems, offering a comprehensive suite of cybersecurity solutions, including risk detection, incident response, vulnerability assessments, and compliance management.
What services do managed security companies provide?
They provide services such as risk detection, incident response, vulnerability assessments, compliance management, and application allowlisting to prevent unauthorized software from executing.
Why is application allowlisting important?
Application allowlisting is a proactive measure that prevents malware and unauthorized software from executing, effectively reducing the attack surface and minimizing vulnerabilities.
How do managed security companies help businesses focus on their core operations?
By outsourcing cybersecurity, companies can concentrate on their core operations without the burden of managing complex protective systems in-house, while receiving ongoing monitoring and proactive risk management.
What is the significance of 24/7 monitoring in managed security?
Continuous 24/7 monitoring is crucial for rapid incident response and expert guidance on best practices, helping organizations manage incidents effectively and maintain a strong cybersecurity posture.
What impact do cyber threats have on businesses?
Cyber threats, including data breaches and ransomware attacks, can lead to significant financial repercussions, with the average cost of a data breach reaching $9.36 million in 2023, highlighting the importance of robust cybersecurity measures.
How do managed security companies support compliance with regulations?
Managed security companies provide tailored protection solutions and Compliance as a Service (CaaS), offering access to enterprise-level compliance expertise to help organizations navigate regulations like GDPR and HIPAA.
Why are small-to-medium enterprises (SMEs) particularly vulnerable to cyberattacks?
Nearly 50% of all cyberattacks target SMEs, making it critical for these organizations to leverage managed security companies for tailored protection solutions to enhance their cybersecurity resilience.
Can you provide an example of effective incident response by a managed security company?
Cyber Solutions effectively restored 4,500 endpoints after a ransomware attack, ensuring healthcare continuity and enhancing protective measures to safeguard patient data.
What should organizations consider when choosing a managed security company?
Organizations should look for a managed security company that offers tailored solutions, 24/7 monitoring, rapid incident response, and compliance management to effectively address their unique cybersecurity challenges.