
In an era where digital threats are more pronounced than ever, C-suite leaders face the formidable task of protecting their organizations from a multitude of cybersecurity risks. A staggering 72.7% of companies identify ransomware as their primary concern, underscoring the urgent need for robust cybersecurity measures. This article explores ten essential practices that not only strengthen defenses but also equip executives to adeptly navigate the complexities of compliance and risk management in a swiftly changing landscape.
How can leaders ensure they are fully prepared to tackle these escalating threats head-on?
C-suite executives must recognize that cybersecurity is not just a technical issue; it’s a business priority. With 72.7% of organizations identifying ransomware as the top threat, the stakes have never been higher. As we look ahead to 2026, an estimated 41% of companies are expected to adopt advanced cybersecurity measures, underscoring the urgent need for robust protection strategies that encompass every facet of their enterprise.
Implementing sophisticated threat detection systems is essential for organizational security. These systems serve as a vital line of defense, significantly reducing incident response times and minimizing breaches. Moreover, employee training is equally crucial, acting as the first barrier against cyber threats. By leveraging best practices, organizations can ensure their cybersecurity framework not only meets but also adapts to the ever-evolving threat landscape.
This proactive approach not only mitigates uncertainties but also enhances operational efficiency, fostering a culture of security awareness among employees. Are your current strategies sufficient to combat the growing tide of cyberattacks? By prioritizing cybersecurity initiatives, organizations can protect their assets and maintain trust with stakeholders.

C-suite executives must prioritize frequent evaluations to identify and reduce weaknesses within their companies. Why? Because the landscape of cybersecurity is evolving, and organizations must stay ahead. These assessments should comprehensively evaluate both internal and external threats, ensuring that all potential risks are identified and addressed. By utilizing tools and methods that align with best practices, entities can effectively prioritize security investments and allocate resources strategically. This proactive approach not only strengthens security but also facilitates adherence to regulatory frameworks.
Current trends suggest that enterprises are progressively acknowledging the importance of risk assessments. In fact, 88% of small businesses conduct these assessments quarterly to tackle vulnerabilities. Moreover, nearly half of financial institutions experienced a third-party cyber event last year, underscoring the critical need for robust security measures.
Expert insights reveal that a systematic assessment of an entity's protective stance is crucial for risk management. Regular assessments ensure that defenses remain effective against evolving cyber threats, which are becoming more frequent and severe. Organizations now face an average of 1,636 cyberattacks per week—a staggering 30% increase from the previous year.
As for defense contractors, understanding and implementing best practices related to risk assessment is essential for maintaining security and operational integrity in 2026 and beyond. Furthermore, risk management frameworks can streamline compliance procedures for SMBs, offering crucial assistance in navigating regulatory requirements while improving their security stance.

C-suite leaders must recognize the critical importance of cybersecurity in today’s digital landscape. With the rise in cyber threats, particularly in healthcare, implementing training programs focused on cybersecurity awareness is not just beneficial - it's essential. These programs should encompass vital topics such as:
training, complemented by simulated phishing attacks, can significantly bolster employees' ability to identify and respond to potential threats. By prioritizing safety, companies can effectively reduce the likelihood of human errors, which often serve as a primary factor in data breaches.
Investing in such training not only protects sensitive information but also builds a resilient workforce capable of navigating the complexities of cybersecurity challenges. Are your employees prepared to face these threats head-on? It's time to take action and prioritize cybersecurity training.

C-suite leaders must recognize that access controls are not just a recommendation but a necessity for protecting sensitive information in today’s digital landscape. With the rise in cyber threats, clearly defining user roles and enforcing the principle of least privilege is crucial. This principle restricts user access to only the information necessary for their job functions, significantly reducing the risk of unauthorized access. Studies show that human error, often stemming from excessive permissions, is a leading cause of data breaches. By adopting this principle, organizations can fortify their defenses against potential threats.
Moreover, implementing multi-factor authentication adds another essential layer of security. MFA requires users to present two or more credentials for identity verification, which greatly enhances security. Research indicates that MFA can reduce the risk of cyberattacks by up to 80-90%. In fact, numerous studies have demonstrated its effectiveness in preventing data breaches.
Creating and regularly assessing permissions not only strengthens security but also aligns with CMMC practices and compliance requirements. Successful case studies of MFA implementation highlight its critical role in protecting sensitive data across various sectors, particularly in healthcare and finance, where the stakes are exceptionally high. Cybersecurity specialists emphasize that embracing the principle of least privilege, alongside strong authentication techniques, is vital for organizations aiming to enhance their security posture and defend against evolving threats.

C-suite leaders must prioritize the creation of a robust incident response plan, a critical component in safeguarding against cyber threats. This plan should encompass:
Regular drills are not just beneficial; they are vital. They ensure that every team member is well-acquainted with their roles and responsibilities, significantly enhancing overall readiness. Did you know that organizations conducting regular incident response exercises can reduce breach costs by an average of $1.49 million?
Moreover, a well-defined incident response plan preserves operational continuity. In today’s rapidly evolving threat landscape, integrating automated tools and frequently updating the incident response plan are not merely suggestions; they are essential practices for effective cybersecurity. By prioritizing these strategies, organizations can effectively navigate the complexities of contemporary digital security challenges.
C-suite leaders must recognize that maintaining comprehensive and current documentation for all cybersecurity policies, procedures, and practices is not just important - it's essential. In today's landscape, where threats are ever-evolving, this documentation should include:
guidelines that are crucial to ensure alignment with changing regulations and organizational practices.
By prioritizing documentation, organizations can significantly enhance their compliance efforts and demonstrate accountability during audits. Consider this: up-to-date documentation not only facilitates smoother audits but also reinforces a company's commitment to cybersecurity and regulatory adherence. As compliance professionals emphasize, the implications of neglecting this aspect can be severe, impacting both reputation and operational integrity.
In conclusion, the proactive management of documentation is a strategic imperative for C-suite leaders. By taking action now, organizations can safeguard their assets and foster a culture of accountability and compliance.

C-suite executives must recognize that continuous monitoring is not just a best practice - it's essential for real-time incident identification and response. In today’s landscape, where cybersecurity threats are prevalent, leveraging monitoring tools is crucial. These tools provide comprehensive visibility into network activity and potential threats, enabling organizations to detect anomalies and vulnerabilities effectively.
Regular log reviews and alert assessments are vital. They help identify unusual patterns that may signal a breach. For instance, organizations that implement continuous monitoring can significantly enhance their incident detection rates. Studies show that timely alerts can reduce the window for threat exploitation to mere minutes. This proactive monitoring strategy not only strengthens a business's protective stance but also ensures rapid response capabilities.
Moreover, access controls and restrictions play a pivotal role in safeguarding sensitive information. By ensuring that only authorized users can access critical data, organizations bolster their defenses. Successful examples of entities employing real-time security incident detection tools illustrate that such measures can lead to a significant reduction in response times and overall exposure. This underscores the crucial importance of continuous monitoring in today’s digital security landscape.

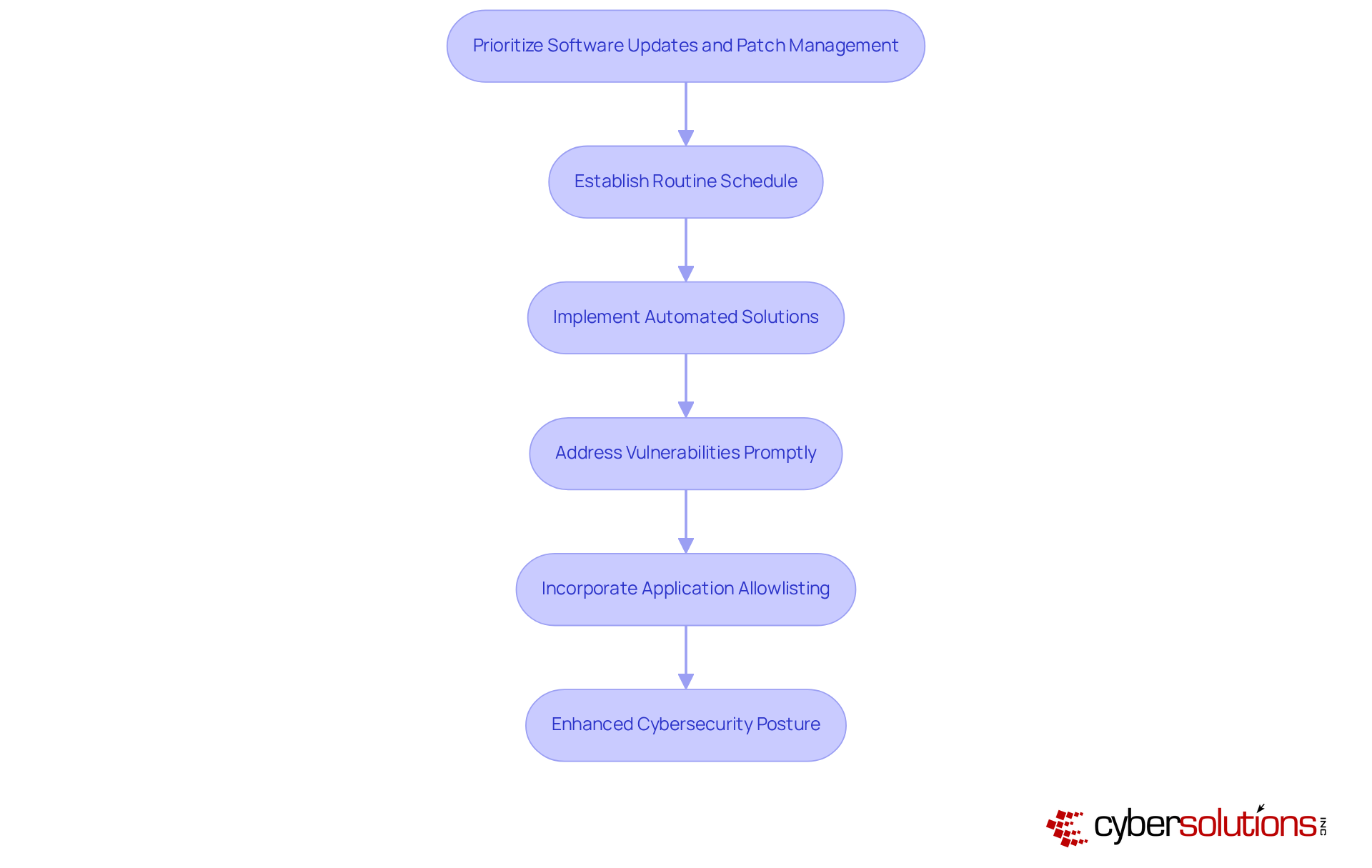
C-suite leaders must recognize that prioritizing regular software updates and patch management is not just a best practice; it’s a fundamental aspect of a robust cybersecurity strategy. In today’s landscape, where cyber threats are increasingly sophisticated, establishing a routine schedule for applying updates and patches across all software and systems is crucial. By promptly addressing vulnerabilities, companies can significantly mitigate the risk of exploitation by cybercriminals.
Automated solutions have proven effective in streamlining this process, ensuring systems remain secure and compliant with industry standards. For instance, organizations that have implemented automated solutions report a decrease in the time dedicated to patching processes, with many experiencing improved efficiency as a result. Industry leaders stress that prompt software updates are essential; in fact, 79% of managers believe that isolating protective patches from functional updates would accelerate the patching process.
Moreover, software updates not only enhance security but also maintain operational integrity, as evidenced by successful implementations across various sectors. Incorporating patch management as part of a layered security strategy can further bolster defenses by proactively preventing unauthorized software from executing. This method supports compliance and assists companies in fulfilling regulatory requirements, ensuring a strong security stance.
By leveraging automation and proactive measures like allowlisting, entities can focus on strategic initiatives while ensuring their cybersecurity defenses are robust and up-to-date. Are you ready to take the necessary steps to fortify your organization’s cybersecurity posture?
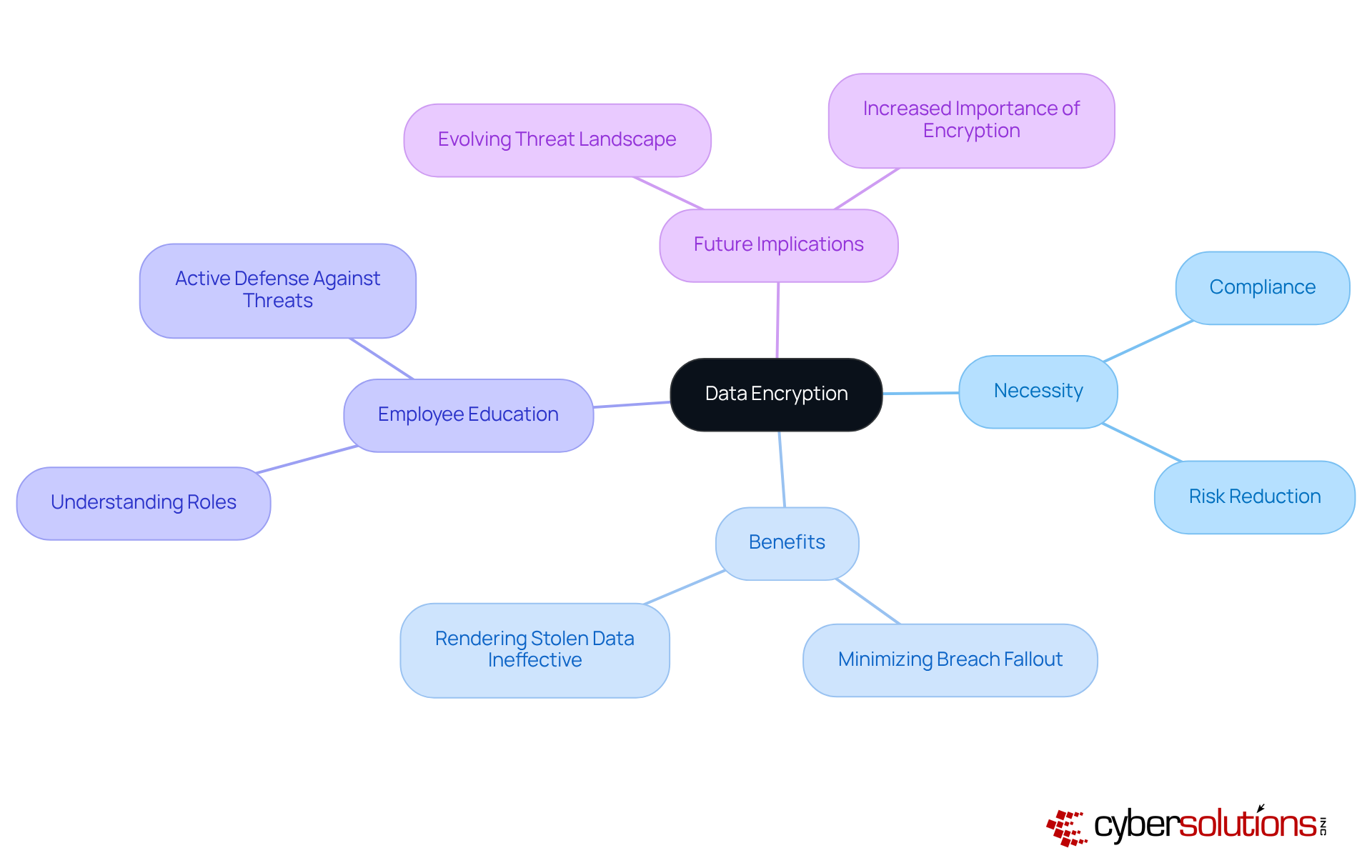
C-suite leaders must recognize that prioritizing data encryption is not just a strategy; it’s a fundamental necessity for safeguarding sensitive information. In today’s landscape, where cyber threats are prevalent, encrypting data both at rest and in transit is essential to prevent unauthorized access. Robust encryption standards not only enhance security but also ensure compliance.
Consider this: organizations that adopt strong encryption practices can significantly reduce the risk of data breaches. Why? Because encryption renders stolen data ineffective for attackers. Statistics reveal that ransomware accounts for approximately 51% of the average cyberattack costs for SMEs, highlighting the financial repercussions of inadequate security measures.
Moreover, educating employees about the importance of encryption further strengthens the organization’s security posture. When employees understand their role, they become proactive defenders. Successful examples abound; companies that have implemented persistent encryption across all environments have effectively minimized the fallout from potential breaches.
As information security experts emphasize, a comprehensive encryption approach is vital for protecting assets and maintaining trust in an increasingly regulated environment. Notably, by 2026, sensitive information will encompass anything that could cause harm if leaked, stolen, or misused, making encryption more critical than ever. Are you prepared to take action and fortify your organization’s defenses?
C-suite leaders must prioritize robust frameworks to effectively assess and mitigate risks associated with external vendors. In today’s landscape, where 70% of companies have faced a data breach, often linked to third-party vulnerabilities, the importance of thorough due diligence before onboarding new partners cannot be overstated. Regular monitoring of vendor performance is vital in averting potential security breaches and ensuring a resilient supply chain.
Implementing a structured third-party risk management framework not only safeguards against these risks but also ensures compliance with evolving regulations, including cybersecurity standards. Successful examples of best practices demonstrate that companies can significantly reduce their exposure to breaches by embedding rigorous assessment processes into their operations. By adopting this proactive approach, leaders can enhance their security posture and maintain a competitive edge.
Furthermore, leveraging Cyber Solutions' expertise in risk management provides organizations with specialized support to recover swiftly from breaches. Their consulting offerings ensure that businesses remain aligned with regulatory requirements, particularly in highly regulated industries. Cyber Solutions simplifies compliance processes for small and medium-sized businesses, allowing them to access enterprise-level expertise without the high costs of in-house staff. Are you ready to fortify your organization against the evolving threats in cybersecurity?

C-suite leaders stand at the forefront of implementing effective cybersecurity strategies, understanding that robust practices are essential not just for compliance but also for safeguarding their organizations against ever-evolving threats. The urgency for comprehensive cybersecurity measures has never been greater, as the landscape of digital threats continues to expand. Executives must prioritize an integrated approach that encompasses:
to build resilient defenses.
Key practices highlighted throughout this article emphasize the necessity of:
Additionally, developing an incident response plan and maintaining up-to-date documentation are crucial for ensuring compliance and operational integrity. These strategies not only mitigate risks but also enhance overall business performance and stakeholder trust.
As organizations navigate the complexities of cybersecurity, the proactive implementation of these practices will be paramount. Leaders must take decisive action to fortify their defenses, ensuring that their organizations are well-equipped to face the challenges ahead. By embracing a comprehensive cybersecurity framework, C-suite executives can protect their assets and drive a culture of security that resonates throughout the entire organization.
The time to act is now-prioritize these essential CMMC practices and secure a safer future for your business.
Why is cybersecurity considered a critical business imperative for organizations?
Cybersecurity is critical because 72.7% of organizations identify ransomware as the largest global digital security threat, making the stakes very high for protecting sensitive data and maintaining trust with stakeholders.
What percentage of companies are expected to adopt advanced threat detection systems by 2026?
An estimated 41% of companies are expected to adopt advanced threat detection systems by 2026.
What are the benefits of implementing sophisticated threat detection systems?
Sophisticated threat detection systems serve as a vital line of defense, significantly reducing incident response times and minimizing breaches, thereby safeguarding sensitive data.
How can managed IT services from Cyber Solutions benefit organizations?
Managed IT services can ensure that an organization's cybersecurity framework meets CMMC practices and adapts to the evolving threat landscape, enhancing operational efficiency and fostering a culture of security awareness.
Why are regular risk assessments important for organizations?
Regular risk assessments are important because they help identify and reduce vulnerabilities, ensuring that organizations stay ahead of rapidly evolving cybersecurity threats.
What percentage of small businesses conduct risk assessments quarterly?
88% of small businesses conduct risk assessments quarterly to address cybersecurity challenges related to suppliers and partners.
What is the average number of cyberattacks organizations face per week?
Organizations now face an average of 1,636 cyberattacks per week, which is a 30% increase from the previous year.
What role does Compliance as a Service (CaaS) play in cybersecurity?
Compliance as a Service (CaaS) can streamline compliance procedures for small and medium-sized businesses (SMBs), helping them navigate regulatory requirements while improving their security stance.
What topics should comprehensive employee training programs for cybersecurity awareness cover?
Employee training programs should cover topics such as phishing detection, safe internet practices, and the significance of data protection.
How can regular training sessions impact employee behavior regarding cybersecurity?
Regular training sessions, complemented by simulated phishing attacks, can significantly enhance employees' ability to identify and respond to potential threats, thereby reducing the likelihood of human errors that lead to data breaches.