
In an age where cyber threats loom larger than ever, healthcare organizations find themselves at a critical juncture regarding data security and operational resilience. The financial ramifications of data loss can be staggering, making it imperative for CFOs to master effective recovery and backup strategies. This article delves into essential practices that not only ensure compliance with regulations like HIPAA but also safeguard sensitive patient information. How can healthcare leaders navigate the complex landscape of backup solutions to protect their institutions from devastating breaches and maintain trust in their services?
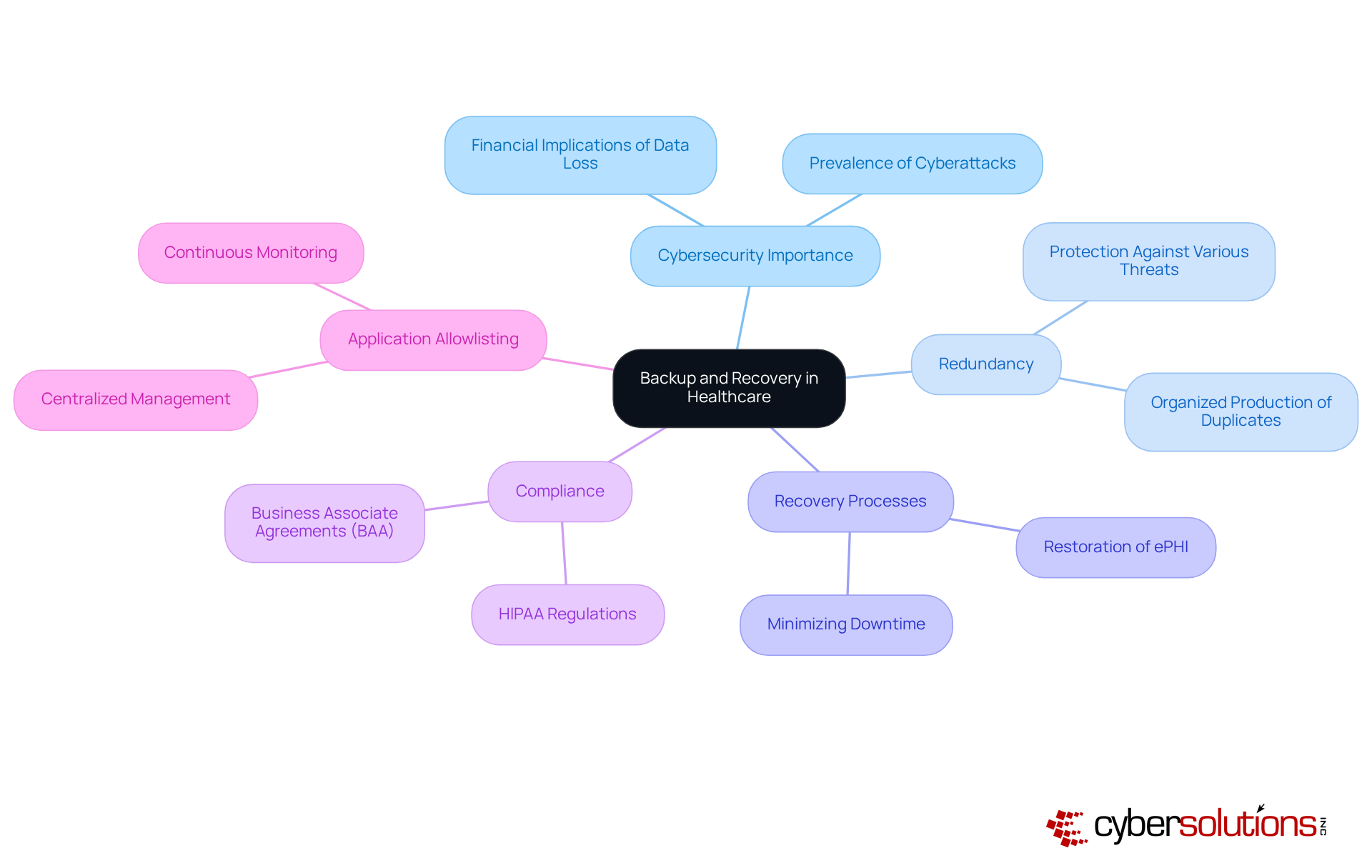
In today's healthcare landscape, the importance of cybersecurity cannot be overstated. With over 90% of healthcare organizations experiencing a data breach, the costs are staggering. Redundancy, defined as the organized production of duplicates of critical data, is crucial for recovery and backup against loss from various threats, including cyberattacks, equipment malfunctions, and natural disasters. Recovery ensures that this information can be reinstated, allowing medical operations to continue smoothly following an incident.
Efficient backup strategies are essential for upholding the integrity of patient records and ensuring compliance. For CFOs, investing in robust backup solutions is not just about compliance; it is a vital component of operational resilience. Organizations that implement comprehensive recovery plans can swiftly restore electronic Protected Health Information (ePHI) after a breach, minimizing downtime and maintaining trust with patients and stakeholders.
By prioritizing these strategies—such as regular validation of information protection protocols and periodic testing of recovery and backup processes—healthcare CFOs can safeguard their organizations from the costly consequences of information loss while ensuring regulatory compliance. Furthermore, incorporating cybersecurity measures into a broader cybersecurity strategy significantly enhances data protection by preventing unauthorized applications from executing, thereby safeguarding sensitive information. Key features of these measures include:
These features assist entities in maintaining strict control over software usage.
Establishing a Business Associate Agreement (BAA) with any third-party service provider managing ePHI storage is crucial for adherence to HIPAA regulations. Cyber Solutions offers customized IT services tailored to meet the specific requirements of healthcare entities, ensuring strong data protection that conform to industry standards. By taking decisive action now, healthcare organizations can mitigate risks effectively.
In the rapidly evolving landscape of healthcare, the importance of robust cybersecurity measures cannot be overstated. Healthcare organizations face unique challenges that demand a comprehensive understanding of recovery and backup strategies to protect sensitive information. Implementing these strategies is not just a technical necessity; it is a critical aspect of maintaining operational integrity and protecting patient data.
In addition to these strategies, having a dedicated recovery team available within 24 hours can significantly enhance recovery efforts. A layered strategy—including endpoint isolation, malware removal, and user training—facilitates a quicker and more thorough recovery, ensuring that healthcare entities can react effectively to potential threats. This combination of swift recovery efforts with strong recovery strategies is essential for reducing harm and maintaining information integrity.
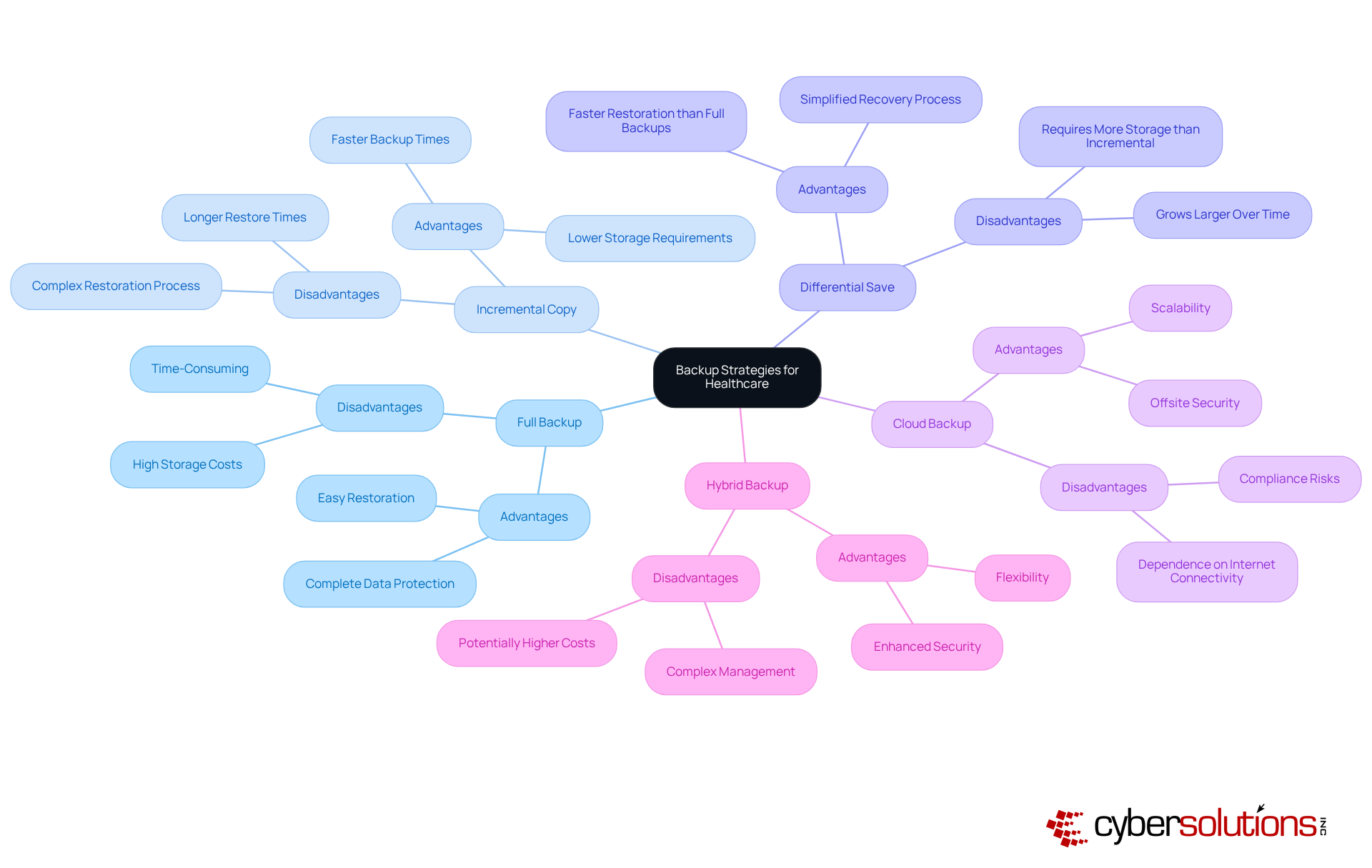
By grasping these strategies, CFOs can make knowledgeable choices regarding which approaches correspond with their financial and operational objectives, ultimately enhancing their institutions' information protection as well as recovery and backup capabilities. Considering that the typical expense of medical information breaches is $9.77 million and that 43% of all security incidents in the medical sector are caused by unintentional human mistakes, it is crucial to establish strong backup practices. As highlighted by HealthITSecurity, establishing a personalized backup strategy designed to meet the particular requirements of healthcare entities is essential for efficient information management.
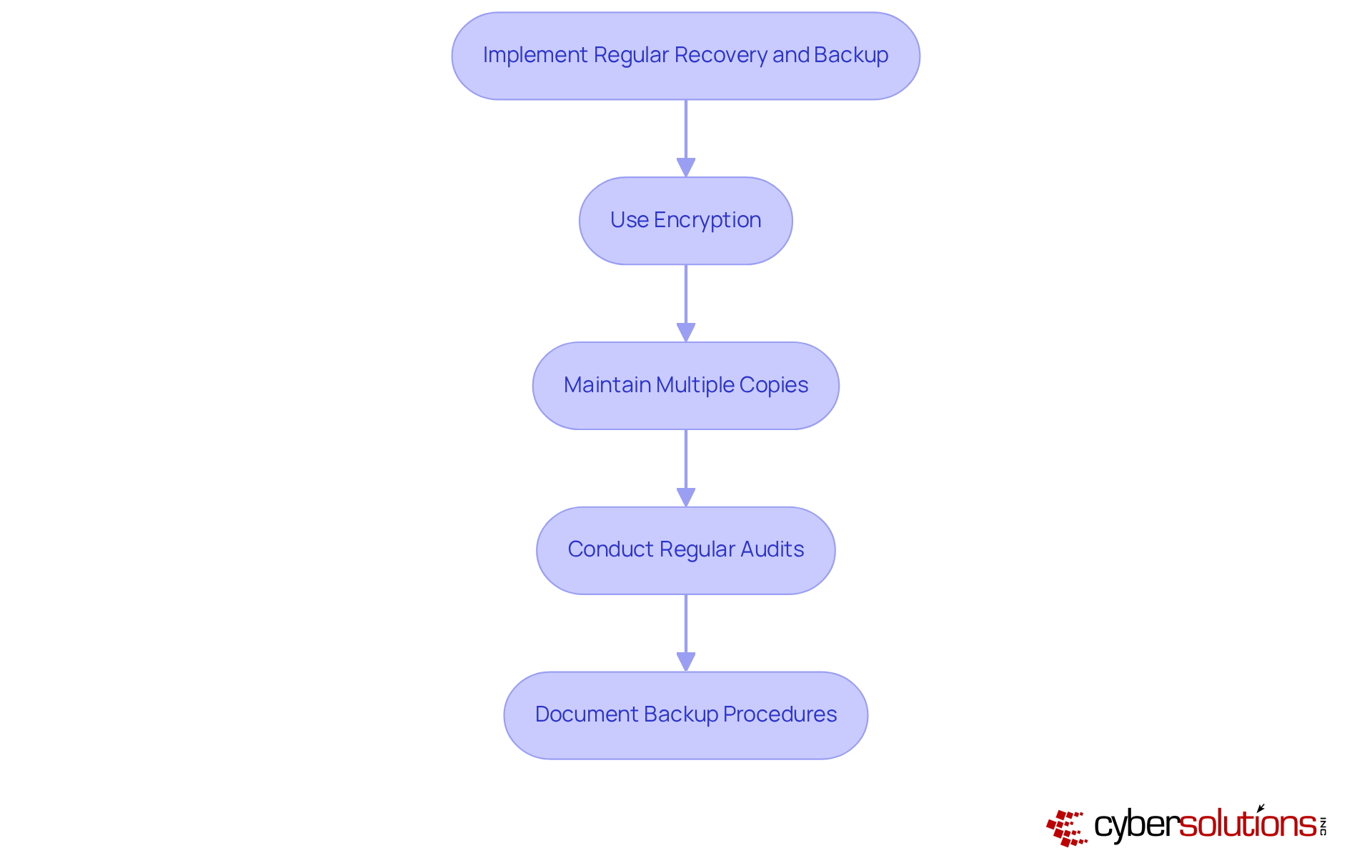
In today's healthcare landscape, the imperative for robust backup and recovery strategies cannot be overstated. With the rise in cyber threats, healthcare entities are mandated to comply with various regulations, notably HIPAA, which requires the protection of patient information. To effectively navigate these challenges and safeguard sensitive data, organizations should adopt the following best practices:
By incorporating these practices, CFOs can effectively reduce risks related to non-compliance and improve their organization's overall security stance, ensuring the safeguarding of sensitive patient information. For further insights on common questions regarding HIPAA compliance and cybersecurity, please refer to our FAQs section, which addresses key concerns and provides additional guidance.
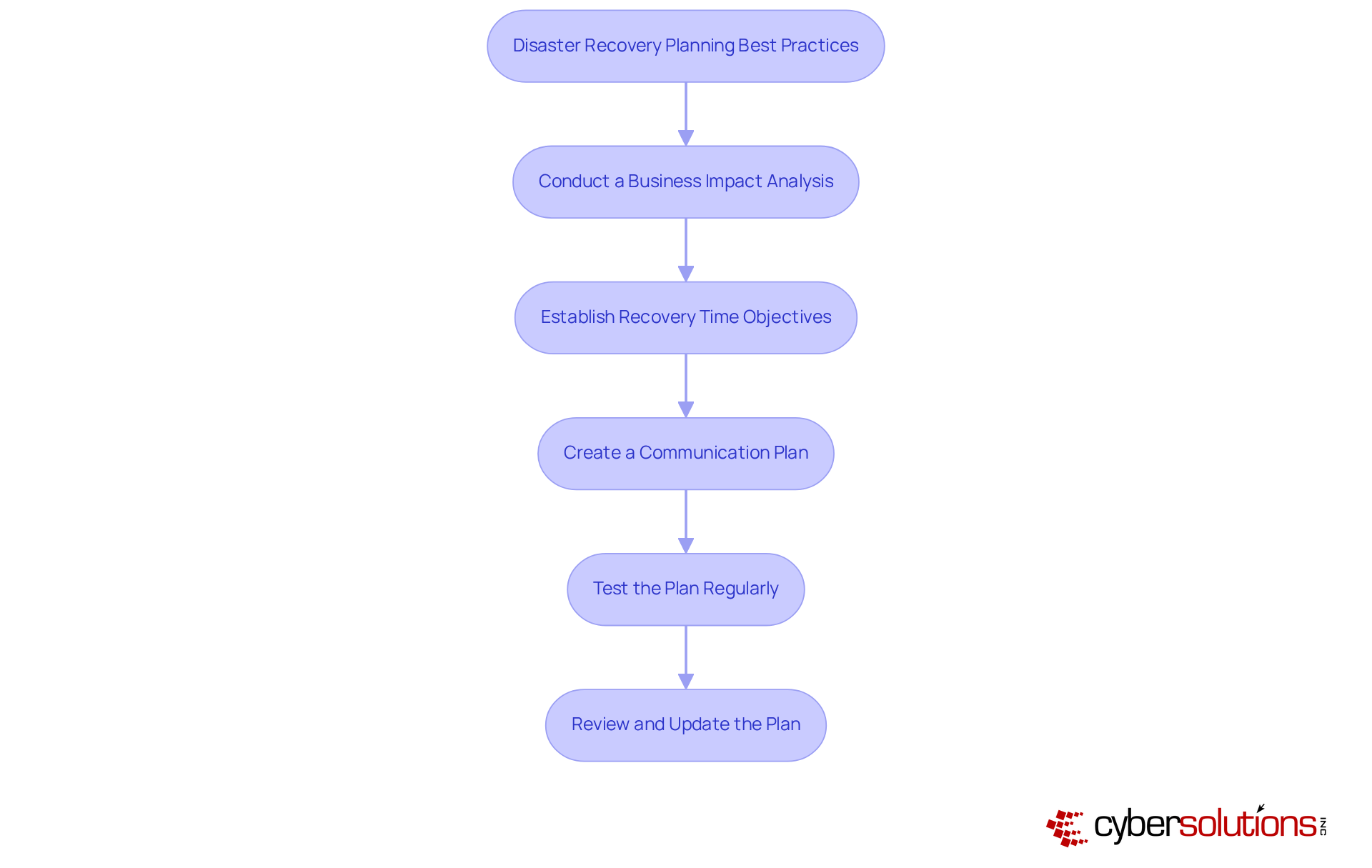
In the face of increasing threats, developing an effective strategy is paramount for healthcare CFOs. To ensure organizational resilience, they should consider the following best practices:
By implementing these best practices, CFOs can significantly enhance their organization’s resilience against disruptions, ensuring that patient safety and operational integrity remain intact.
In the healthcare sector, establishing effective recovery and backup strategies is vital for safeguarding sensitive patient information and ensuring operational resilience. As cyber threats continue to escalate, healthcare CFOs must prioritize robust data protection measures to not only comply with regulations like HIPAA but also to maintain trust with patients and stakeholders. The implementation of comprehensive backup solutions is essential for minimizing downtime and facilitating swift recovery in the event of data loss.
The article highlights various backup strategies, including:
Each with its unique advantages and considerations. It emphasizes the significance of regular testing, encryption, and maintaining multiple copies of data to enhance resilience against potential breaches. Moreover, the necessity of a well-structured disaster recovery plan, supported by a thorough Business Impact Analysis and clear communication strategies, cannot be overstated. These practices collectively contribute to a proactive approach in managing risks associated with data loss and ensuring compliance with regulatory standards.
Ultimately, the implementation of these best practices not only fortifies healthcare organizations against cyber threats but also reinforces the integrity of patient care. By taking decisive action now, healthcare CFOs can create a secure environment that prioritizes data protection, operational continuity, and regulatory compliance. The time to act is now—investing in robust recovery and backup strategies is not just a necessity; it is a critical investment in the future of healthcare operations.
What is the significance of backup and recovery in healthcare?
Backup and recovery are vital in healthcare to protect against data loss from cyberattacks, equipment malfunctions, and natural disasters, ensuring that medical operations can continue smoothly after an incident.
What role does redundancy play in data protection?
Redundancy involves creating organized duplicates of essential information, which is crucial for recovery and backup, helping to mitigate the impact of data loss.
Why is compliance with regulations like HIPAA important for healthcare organizations?
Compliance with regulations such as HIPAA is essential for upholding the integrity of patient records and avoiding potential legal and financial repercussions associated with data breaches.
How can healthcare CFOs benefit from investing in recovery and backup solutions?
Investing in robust recovery and backup solutions helps CFOs ensure operational resilience, allowing organizations to swiftly restore electronic Protected Health Information (ePHI) after a breach, minimizing downtime and maintaining trust with patients and stakeholders.
What strategies can healthcare organizations implement to safeguard against information loss?
Strategies include regular validation of information protection protocols, periodic testing of recovery and backup processes, and incorporating application allowlisting into a broader cybersecurity strategy.
What are the key features of application allowlisting?
Key features of application allowlisting include continuous monitoring of application activity and centralized management of allowlists, which help maintain strict control over software usage.
Why is it important to establish a Business Associate Agreement (BAA) with third-party service providers?
Establishing a BAA with third-party service providers is crucial for adherence to HIPAA regulations, ensuring that ePHI storage is managed in compliance with industry standards.
How can Cyber Solutions assist healthcare organizations?
Cyber Solutions offers customized IT services tailored to the specific requirements of healthcare entities, providing strong recovery and backup solutions that conform to industry standards.