
In today’s digital landscape, where communication is vital, spam bombing has emerged as a significant threat for organizations across all sectors. This sophisticated cyberattack method floods inboxes with an overwhelming number of unwanted messages, severely hindering access to essential communications. As the frequency and complexity of these attacks escalate, it becomes crucial for organizations to grasp the mechanics and implications of spam bombs. How can businesses effectively navigate this evolving threat landscape and safeguard themselves against the chaos that spam bombs can unleash?
Understanding the current cybersecurity threats is imperative. Spam bombing not only disrupts daily operations but also poses risks to sensitive information and overall organizational integrity. The implications for businesses are profound, as they must contend with the potential for lost productivity and compromised communications.
To combat these challenges, organizations must adopt proactive strategies. Cyber Solutions can provide the necessary tools and expertise to fortify defenses against spam attacks. By implementing robust cybersecurity measures, businesses can protect themselves from the disruptive effects of spam bombing and ensure that critical communications remain intact.
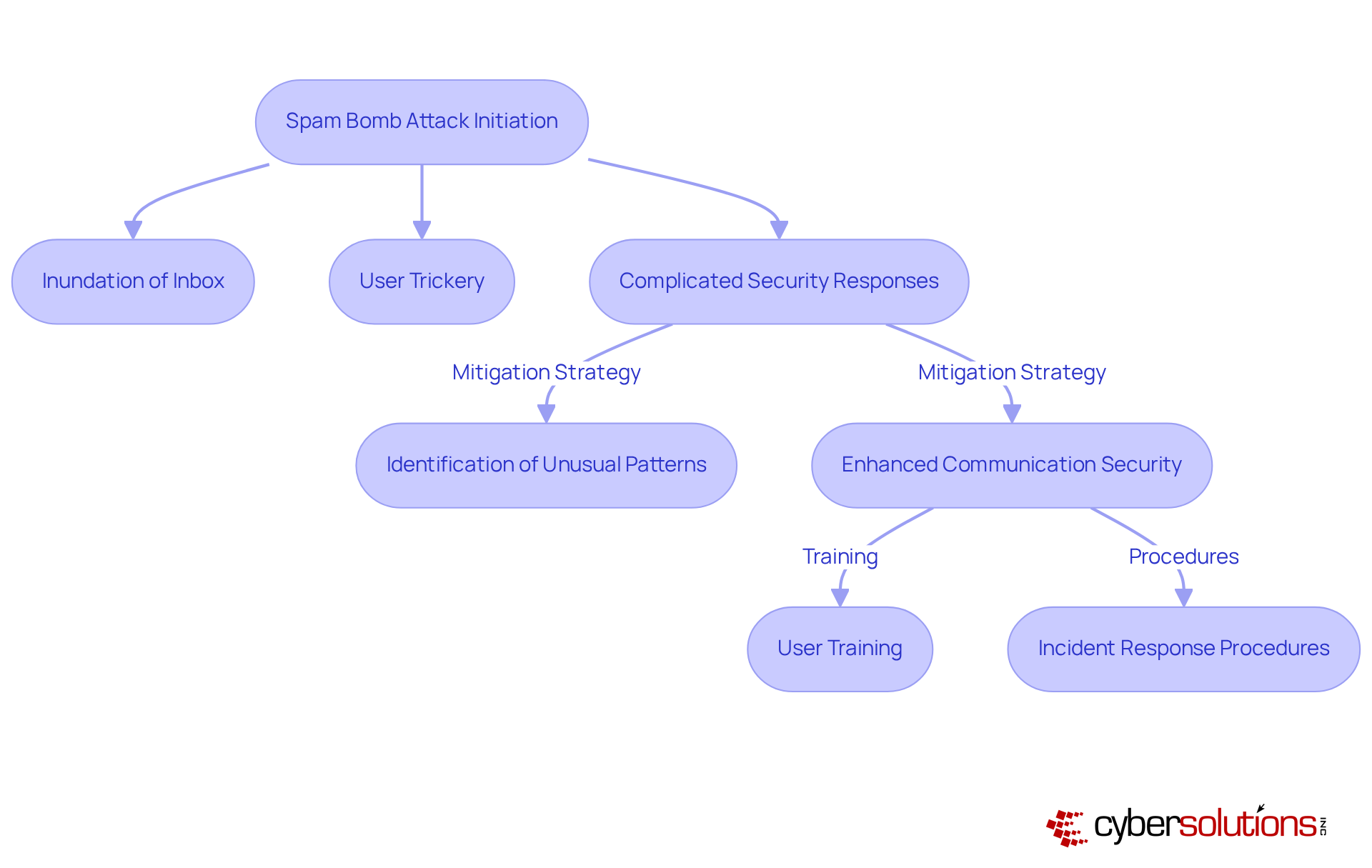
Spam flooding is a sophisticated attack that utilizes a spam bomb to inundate a target's inbox with a staggering volume of unwanted messages in a short timeframe. This tactic is specifically engineered to disrupt the recipient's email system, complicating access to legitimate communications. Unlike typical unsolicited messages that often contain promotional content, these large-scale emails, referred to as spam bombs, serve a more malicious purpose, acting as a diversion for further incidents such as data breaches or phishing attempts. In 2025, the rise of such strategies has been linked to organizations like BlackBasta, which employ disruptive tactics as part of broader attack sequences, frequently leveraging social engineering techniques to exploit vulnerabilities.
The impact of unsolicited messages on organizations can be profound. A recent study revealed that 86.5% of individuals believe the spam they receive has increased over the past year, highlighting a growing concern regarding online security. Furthermore, traditional email security measures are becoming increasingly inadequate, as they often focus on individual messages rather than identifying trends indicative of unwanted mass emails. This oversight can lead to operational disruptions and heightened vulnerability to more severe threats.
To effectively combat these threats, organizations must adopt prevention strategies, including comprehensive training, alongside advanced technologies. Cyber Solutions provides continuous monitoring to detect suspicious activities and thwart them before they escalate into serious threats. This approach safeguards companies from ransomware, phishing, and other malware incursions through advanced threat intelligence. Instant notifications and insights empower organizations to take swift action, preventing downtime or breaches and ensuring they can respond effectively to flooding incidents.
Real-world incidents underscore the seriousness of this threat. Darktrace reported a series of attacks that exploited the MailChimp Mandrill extension, where attackers not only flooded inboxes but also conducted reconnaissance on target devices post-assault. Such occurrences highlight the urgent need for organizations to evolve their security measures, integrating dynamic solutions with human oversight to effectively counter these layered threats. As the landscape of cyber dangers continues to shift, understanding spam bombing is crucial for establishing robust protections and response strategies. With 160 billion unsolicited messages sent daily, of which 46% are deemed unwanted, the situation is alarming. As PJ Bradley notes, "The recent increase in spam bomb incidents should emphasize the necessity for businesses to develop their defenses beyond relying on fixed filters."

In today's digital landscape, the threat of a spam bomb flooding email initiatives poses a significant risk. These attacks inundate a target's inbox with a barrage of messages, often without the victim's awareness. Imagine receiving over 150 messages in less than five minutes from 107 unique domains, all while security email gateways fail to filter them out. This overwhelming influx complicates the ability to identify critical communications amidst the chaos.
Attackers often employ deceptive tactics to exacerbate the situation, tricking users into subscribing to various mailing lists. This not only increases the volume of unwanted messages but also conceals harmful content within seemingly legitimate notifications. The messages can range from genuine-looking alerts to blatant junk, making it increasingly difficult for victims to discern important communications.
Cybersecurity experts stress the urgent need for organizations to move beyond static filters. Conventional techniques frequently struggle to address the complex characteristics of unwanted messages, which can include behavioral irregularities and rapid registration spikes. How can organizations stay ahead of these evolving tactics? By focusing on identifying unusual patterns in email activity, they can better protect themselves.
Understanding the mechanics of spam bombing is crucial. Organizations can develop more effective strategies, significantly reducing the risks associated with these assaults. In a world where every message counts, vigilance is essential.
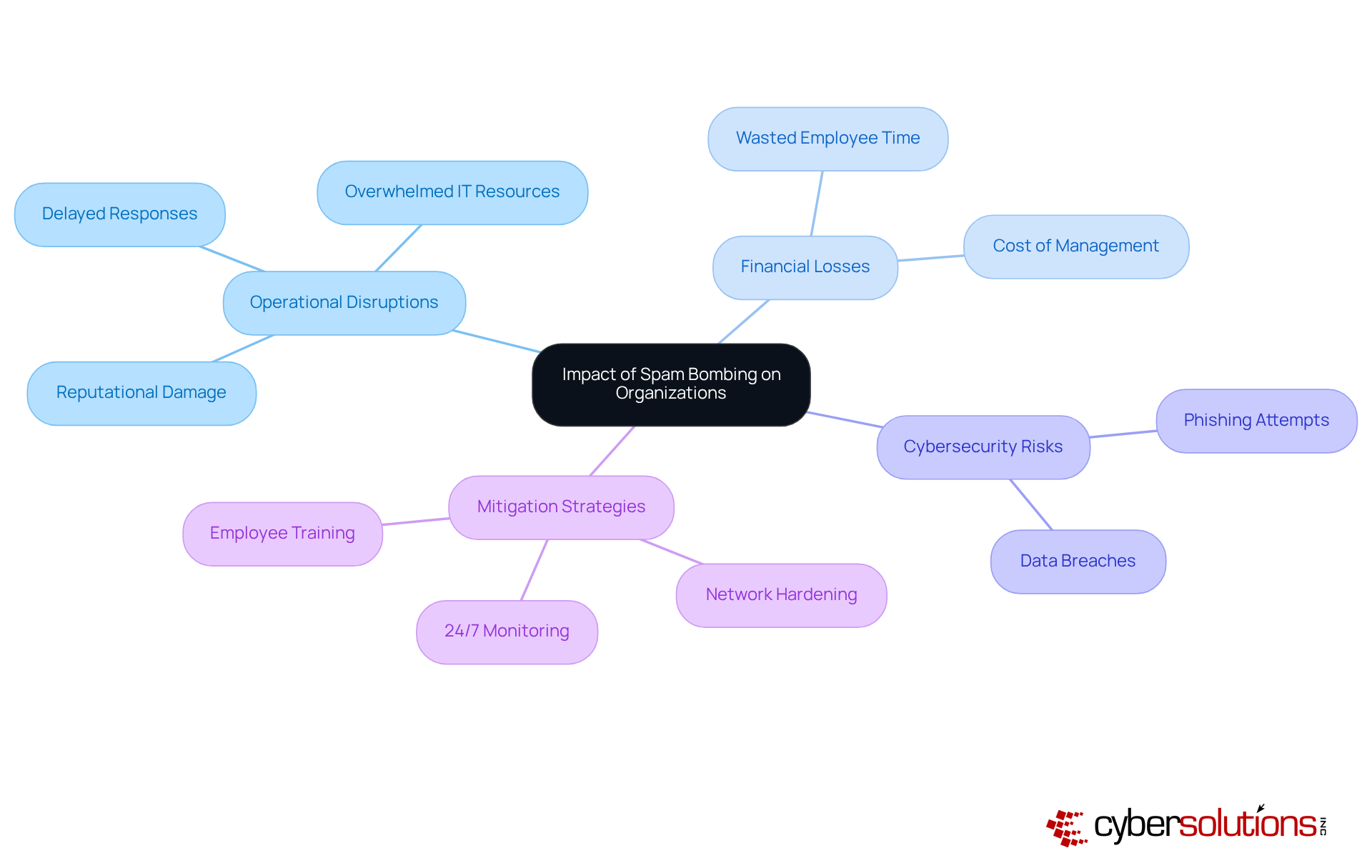
poses a serious threat to organizations, leading to significant disruptions. When employees are inundated with a flood of emails, important messages can easily slip through the cracks, leading to delayed responses to clients and partners. This not only jeopardizes reputational integrity but also undermines trust—something that can be challenging to restore. The sheer volume of emails can overwhelm IT resources, driving up costs associated with email management and potentially causing downtime. For instance, if each employee spends just five minutes daily managing unwanted emails, a medium-sized firm could waste thousands of hours annually, leading to considerable financial losses.
Moreover, unsolicited messages, often referred to as spam, can mask even greater threats, such as phishing attempts or malware, complicating detection efforts. Darktrace's analysis indicates that during a spam campaign, the devices of affected users often engage in reconnaissance activities. This suggests that attackers frequently blend benign and malicious elements to evade detection. To mitigate these risks, Cyber Solutions Inc. underscores the necessity of implementing effective security measures. These strategies include:
Additionally, training staff to recognize and uphold proper cybersecurity hygiene is vital in reducing vulnerabilities.
The consequences of such incidents can be dire, especially if they lead to a data breach or operational failure. Therefore, implementing robust security protocols is crucial for detecting and halting suspicious activities before they escalate into significant threats. By leveraging advanced threat intelligence, organizations can protect themselves from ransomware, phishing, and other malware attacks, ensuring a comprehensive cybersecurity strategy that defends against the myriad dangers posed by unsolicited messages.
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations in the healthcare sector. With the rise of sophisticated cyber threats, it’s crucial to adopt a strategy to combat unwanted messages effectively. Here are several key components to consider:
By implementing these strategies, alongside comprehensive measures like firewalls, encryption, and advanced phishing protection from Cyber Solutions, organizations can significantly bolster their defenses against spam bomb attacks. This proactive approach not only enhances their overall cybersecurity posture but also safeguards sensitive information, ensuring a secure environment for both staff and patients.

The threat of spam bombing poses a serious challenge for organizations today, especially as cyberattack strategies continue to evolve. This malicious tactic not only floods inboxes with unwanted messages but also acts as a smokescreen for more severe security breaches. Understanding the nature of spam bombs and their potential impact is crucial for organizations aiming to safeguard their vital communications against these disruptive attacks.
Key insights throughout this discussion reveal the mechanics of spam bombing and the significant operational disruptions it can cause. The rise in unsolicited messages, combined with social engineering tactics, demands a shift from traditional email security approaches to more dynamic and proactive strategies. Implementing strong message filtering, user education, and continuous monitoring are essential steps in defending against these threats.
The urgency to address spam bombing cannot be overstated. Organizations must act decisively to bolster their defenses, ensuring they are not merely reacting to threats but actively preventing them. By adopting a comprehensive cybersecurity strategy that includes advanced filtering solutions and employee training, businesses can significantly mitigate the risks posed by spam bombs, thereby protecting both their operations and their reputations in an increasingly hostile digital landscape.
What is spam bombing?
Spam bombing is a cyberattack method that floods a target's inbox with a large volume of unwanted messages in a short timeframe, disrupting access to legitimate communications.
How does spam bombing differ from typical spam messages?
Unlike typical unsolicited messages that often contain promotional content, spam bombs serve a malicious purpose, acting as a diversion for further incidents such as data breaches or phishing attempts.
What organizations are linked to the rise of spam bombing strategies?
In 2025, the rise of spam bombing strategies has been linked to organizations like BlackBasta, which employ disruptive tactics as part of broader attack sequences.
What impact do unsolicited messages have on organizations?
Unsolicited messages can lead to operational disruptions and heightened vulnerability to severe threats, with a study showing that 86.5% of individuals believe the volume of scam messages has increased over the past year.
Why are traditional email security measures becoming inadequate?
Traditional email security measures often focus on individual messages rather than identifying trends indicative of unwanted mass emails, which can lead to operational disruptions.
What proactive cybersecurity solutions should organizations adopt to combat spam bombing?
Organizations should adopt comprehensive firewall and network security services, alongside 24/7 threat monitoring, to effectively combat spam bombing threats.
How does Cyber Solutions help organizations with spam bombing threats?
Cyber Solutions provides continuous monitoring to detect suspicious activities and thwart them before they escalate, safeguarding companies from ransomware, phishing, and malware incursions.
What real-world incidents highlight the seriousness of spam bombing?
Darktrace reported spam bomb attacks that exploited the MailChimp Mandrill extension, where attackers flooded inboxes and conducted reconnaissance on target devices post-assault.
What is the scale of unsolicited messages sent daily?
Approximately 160 billion unsolicited messages are sent daily, with 46% of them deemed unwanted, indicating a significant issue.
What should businesses do in response to the increase in spam bomb incidents?
Businesses should develop their communication security strategies beyond relying on fixed filters to effectively counter spam bombing threats.