
In today’s world, where cyber threats are escalating not just in frequency but also in sophistication, the urgency for effective cybersecurity measures is paramount. Managed cybersecurity solutions present organizations with a strategic avenue to enhance their defenses against a wide array of potential attacks. These solutions grant access to specialized expertise and advanced technologies that many businesses find challenging to cultivate internally.
As companies navigate this intricate landscape, a pressing question arises: how can they ensure they are selecting the right managed services to effectively protect their digital assets and uphold compliance in an ever-changing regulatory environment? This is where understanding the unique challenges faced by organizations becomes crucial.
Cybersecurity is not merely a technical issue; it’s a fundamental aspect of organizational resilience. By leveraging managed services, organizations can not only safeguard their assets but also position themselves to thrive amidst evolving threats. The right partner can make all the difference in navigating this complex terrain.
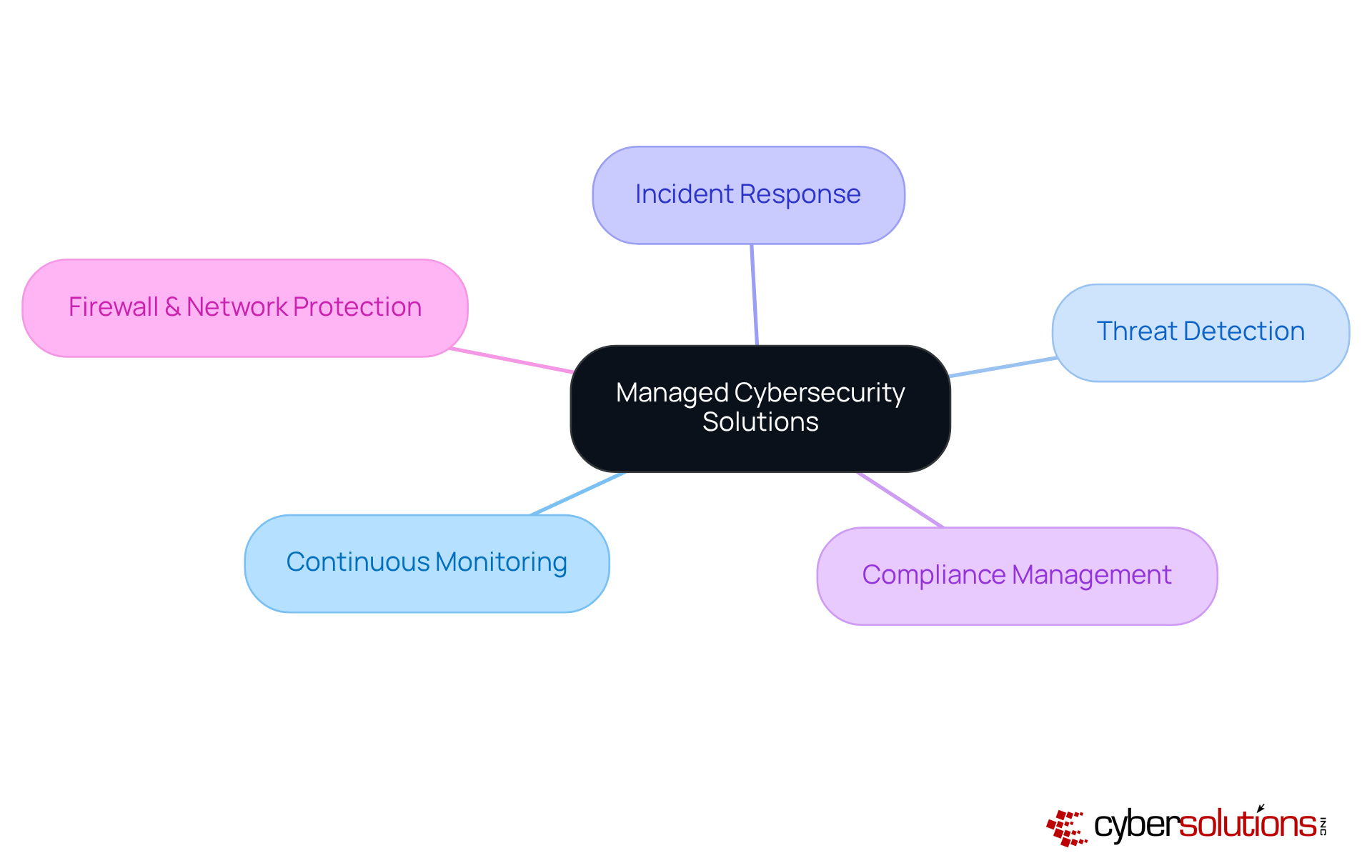
In today's digital landscape, the importance of robust cybersecurity cannot be overstated. Organizations face an ever-evolving array of cyber threats, making managed cyber security solutions essential for safeguarding their assets. These offerings, provided by third-party vendors like Cyber Solutions, encompass:
By outsourcing these critical functions, businesses gain access to specialized expertise and advanced technologies, alleviating the burden of maintaining an internal protection team.
As we look toward 2025, a significant number of organizations are adopting managed cyber security solutions, reflecting a growing recognition of their vital role in protecting digital assets. Companies utilizing managed protection providers (MSSPs) have reported enhanced incident response times and improved compliance with regulatory frameworks. This trend underscores the necessity of outsourcing security functions, allowing organizations to remain agile and resilient against increasing cyber threats.
This shift towards managed services is not merely a trend; it represents a fundamental transformation in how businesses approach digital security. By integrating these solutions into their operational strategies, organizations can strengthen their protective posture while focusing on core operations. The expertise offered by managed cybersecurity providers is invaluable, ensuring compliance with industry regulations and enhancing overall security measures.
In conclusion, as cyber threats continue to escalate, organizations find that the adoption of managed cyber security solutions is becoming a strategic imperative. Embracing this approach not only fortifies defenses but also positions businesses for success in an increasingly complex digital environment.
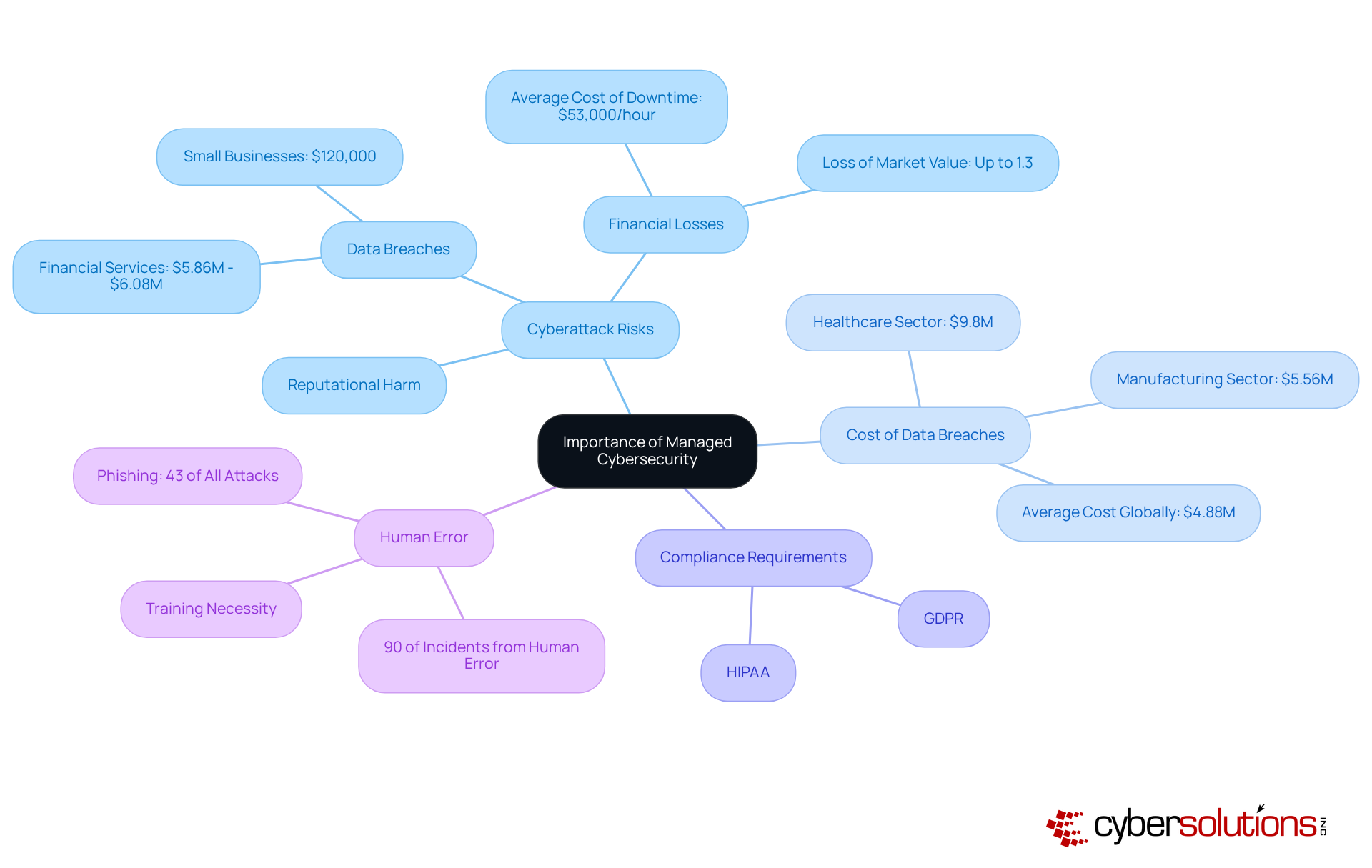
In the current digital landscape, the significance of managed cyber security solutions is paramount. As cyberattacks grow more sophisticated and frequent, organizations face significant risks that can result in data breaches, financial losses, and reputational harm. Projections suggest that cybercrime costs could escalate to a staggering $10.5 trillion annually by 2025, highlighting the urgent need for businesses to strengthen their defenses.
For example, the average cost of a data breach in the financial services sector ranges from $5.86 million to $6.08 million, while small businesses may incur around $120,000 to recover from a cyberattack. Furthermore, regulatory frameworks such as GDPR and HIPAA impose strict compliance requirements, compelling organizations to adopt robust security measures. Managed cyber security solutions equip companies with the essential knowledge and tools to effectively tackle these challenges, ensuring they remain safe and compliant in an increasingly complex environment.
With 90% of cyber incidents originating from human error, the necessity for comprehensive training and proactive security measures is more critical than ever. By investing in managed digital security, organizations can mitigate risks and protect their assets against the ever-evolving threat landscape. Are you prepared to safeguard your organization against these looming threats?
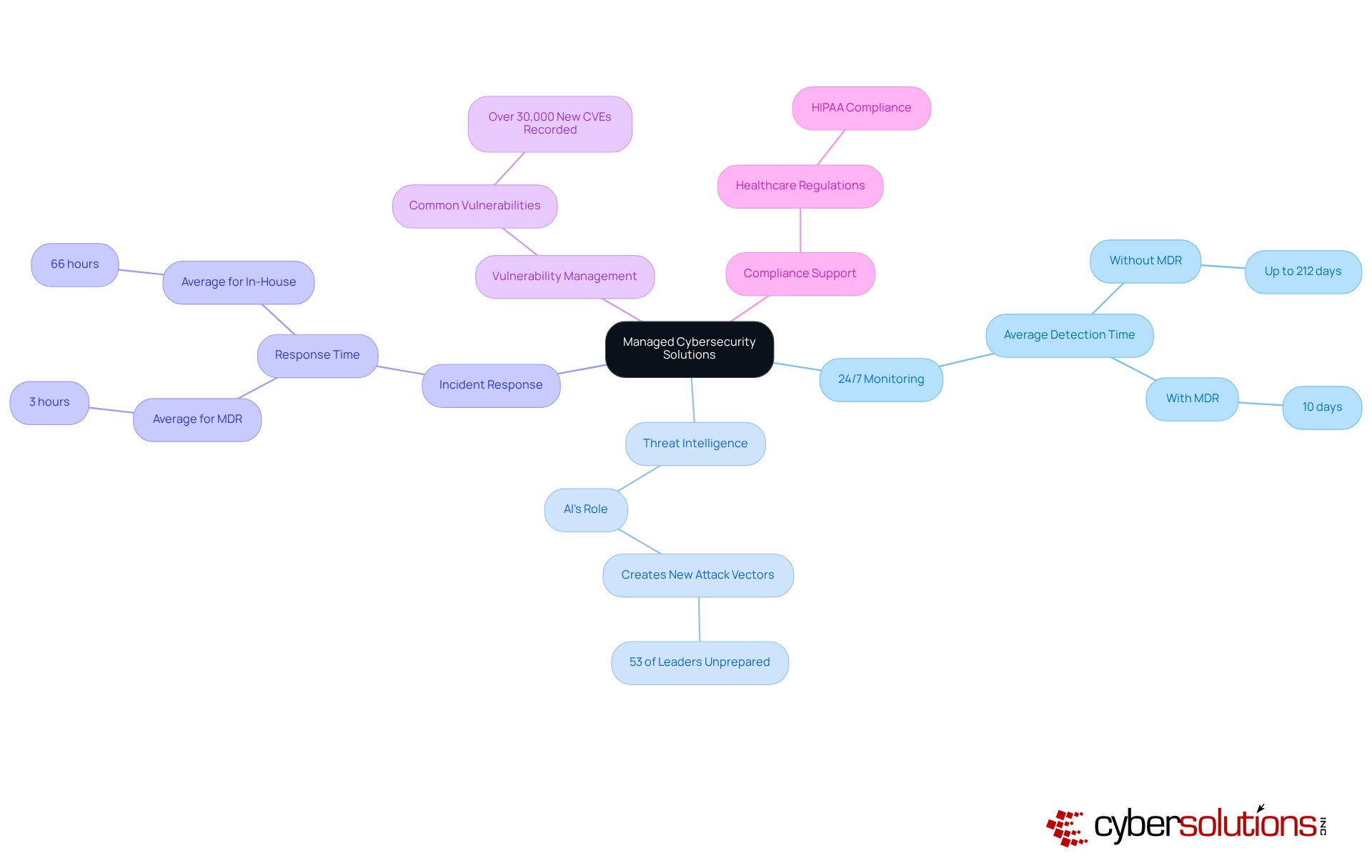
Cybersecurity is not just a necessity; it’s a critical component of operational integrity, especially in healthcare. With the rise of sophisticated cyber threats, organizations must adopt managed cyber security solutions that include:
These solutions take a proactive stance, leveraging advanced technologies like artificial intelligence and machine learning to detect and respond to threats in real-time. For instance, organizations utilizing Managed Detection and Response (MDR) services have seen a remarkable 62% reduction in security incidents annually, underscoring the effectiveness of these strategies in fortifying security frameworks.
Current trends reveal that AI is becoming increasingly vital in digital security. A staggering 53% of leaders acknowledge that AI creates new attack vectors for which they are unprepared. This duality highlights AI's role in both strengthening defenses and introducing new challenges. Furthermore, the importance of 24/7 monitoring cannot be overstated; entities without this capability can take up to 212 days to identify a security incident, while those employing MDR can do so in just 10 days.
Managed cyber security solutions provided by tailored cybersecurity providers address the unique needs of various industries. For example, healthcare organizations often require specialized compliance assistance for regulations like HIPAA, while financial institutions focus on protecting sensitive customer information. This level of customization ensures that organizations receive the most relevant and effective defenses against evolving cyber threats.
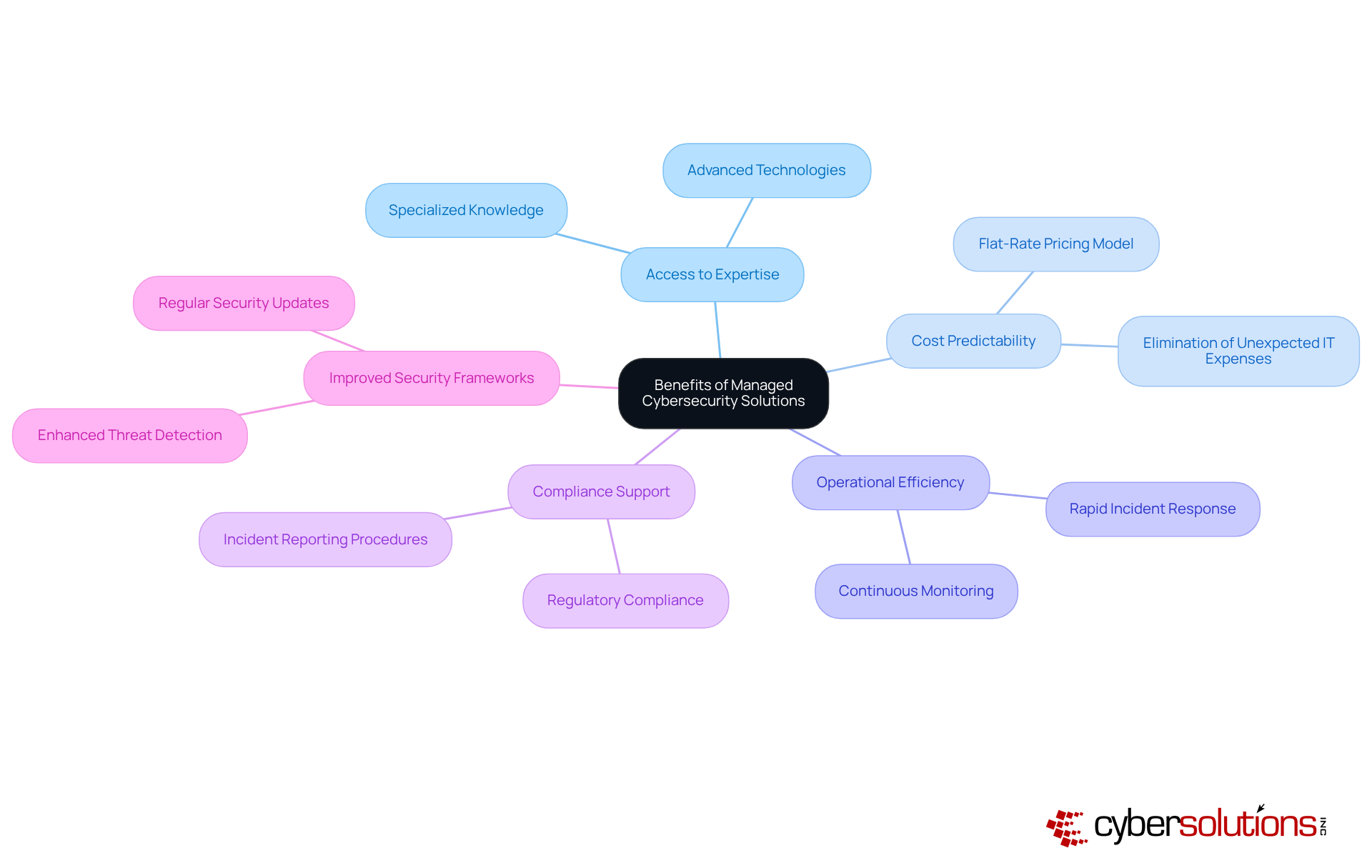
In today's digital landscape, the importance of robust cybersecurity cannot be overstated. Organizations face an ever-evolving array of cyber threats that can jeopardize their operations and reputation. Implementing managed cyber security solutions provides a strategic advantage by granting access to specialized expertise and advanced technologies that could be too expensive for businesses to develop internally.
With Cyber Solutions' flat-rate pricing model, companies can simplify their budgeting process. This ensures predictable monthly costs, eliminating unexpected IT expenses that can disrupt financial planning. Such an approach not only enhances operational efficiency but also facilitates continuous monitoring and rapid incident response, significantly mitigating the potential impact of cyber threats.
Moreover, managed cyber security solutions play a crucial role in helping organizations uphold compliance with regulatory requirements. This reduces the risk of expensive fines and reputational harm. For instance, companies that have adopted managed cyber security solutions report improved operational efficiency, reduced downtime, and enhanced overall security frameworks. These improvements ultimately lead to a stronger return on investment.
Additionally, our Compliance as a Service (CaaS) offerings provide essential support for businesses in highly regulated industries. They ensure that organizations meet stringent standards while preparing for audits and maintaining ongoing compliance. Are you ready to fortify your cybersecurity posture and safeguard your organization against potential threats?
In today’s digital landscape, the importance of managed cybersecurity solutions is paramount. Organizations are grappling with increasingly sophisticated cyber threats, making robust protection not just a necessity but a strategic imperative. By outsourcing cybersecurity functions to specialized providers, businesses can bolster their defenses and concentrate on their core operations, ensuring a proactive stance in safeguarding their digital assets.
The advantages of adopting managed cybersecurity solutions are significant. Continuous monitoring, threat detection, and compliance management are just a few of the key benefits. These services not only mitigate the risk of data breaches and financial losses but also enhance operational efficiency and improve incident response times. Moreover, the integration of advanced technologies, such as artificial intelligence, fortifies security measures, rendering organizations more resilient against emerging threats.
Ultimately, embracing managed cybersecurity solutions is essential for organizations striving to thrive in an increasingly complex and perilous digital environment. As the costs associated with cybercrime continue to escalate, investing in these services transcends mere protection; it is a strategic move that positions businesses for long-term success. Organizations must act decisively now, strengthening their cybersecurity posture to ensure they are well-equipped to navigate future challenges.
What are managed cybersecurity solutions?
Managed cybersecurity solutions are services provided by third-party vendors that include continuous monitoring, threat detection, incident response, compliance management, and comprehensive firewall and network protection to safeguard organizations' digital assets.
Why are managed cybersecurity solutions important for organizations?
These solutions are essential because they help organizations protect against an ever-evolving array of cyber threats, ensuring the security of their assets and allowing them to focus on their core operations.
What benefits do organizations gain from outsourcing cybersecurity functions?
By outsourcing cybersecurity functions, organizations gain access to specialized expertise and advanced technologies, which alleviates the burden of maintaining an internal protection team and improves incident response times and regulatory compliance.
What trends are emerging regarding the adoption of managed cybersecurity solutions?
A significant number of organizations are adopting managed cybersecurity solutions, reflecting a growing recognition of their importance in protecting digital assets and enhancing security measures.
How do managed cybersecurity solutions impact incident response and compliance?
Companies utilizing managed protection providers (MSSPs) have reported enhanced incident response times and improved compliance with regulatory frameworks, highlighting the effectiveness of these solutions.
What does the shift towards managed services represent in cybersecurity?
The shift towards managed services represents a fundamental transformation in how businesses approach digital security, integrating these solutions into their operational strategies to strengthen their protective posture.
Why is adopting managed cybersecurity solutions considered a strategic imperative?
As cyber threats continue to escalate, adopting managed cybersecurity solutions is seen as a strategic imperative because it fortifies defenses and positions businesses for success in a complex digital environment.