
In a world where cyber threats are increasingly sophisticated and prevalent, the stakes have never been higher for C-suite leaders tasked with safeguarding their organizations' sensitive information. This article delves into ten essential safe web browsing tips specifically designed for executives, offering practical strategies that not only enhance security but also foster a culture of vigilance among employees. As cybercriminals constantly adapt their tactics, how can leaders ensure their teams are equipped to navigate these treacherous waters effectively? The following insights will illuminate key practices that can significantly bolster an organization's cybersecurity posture.
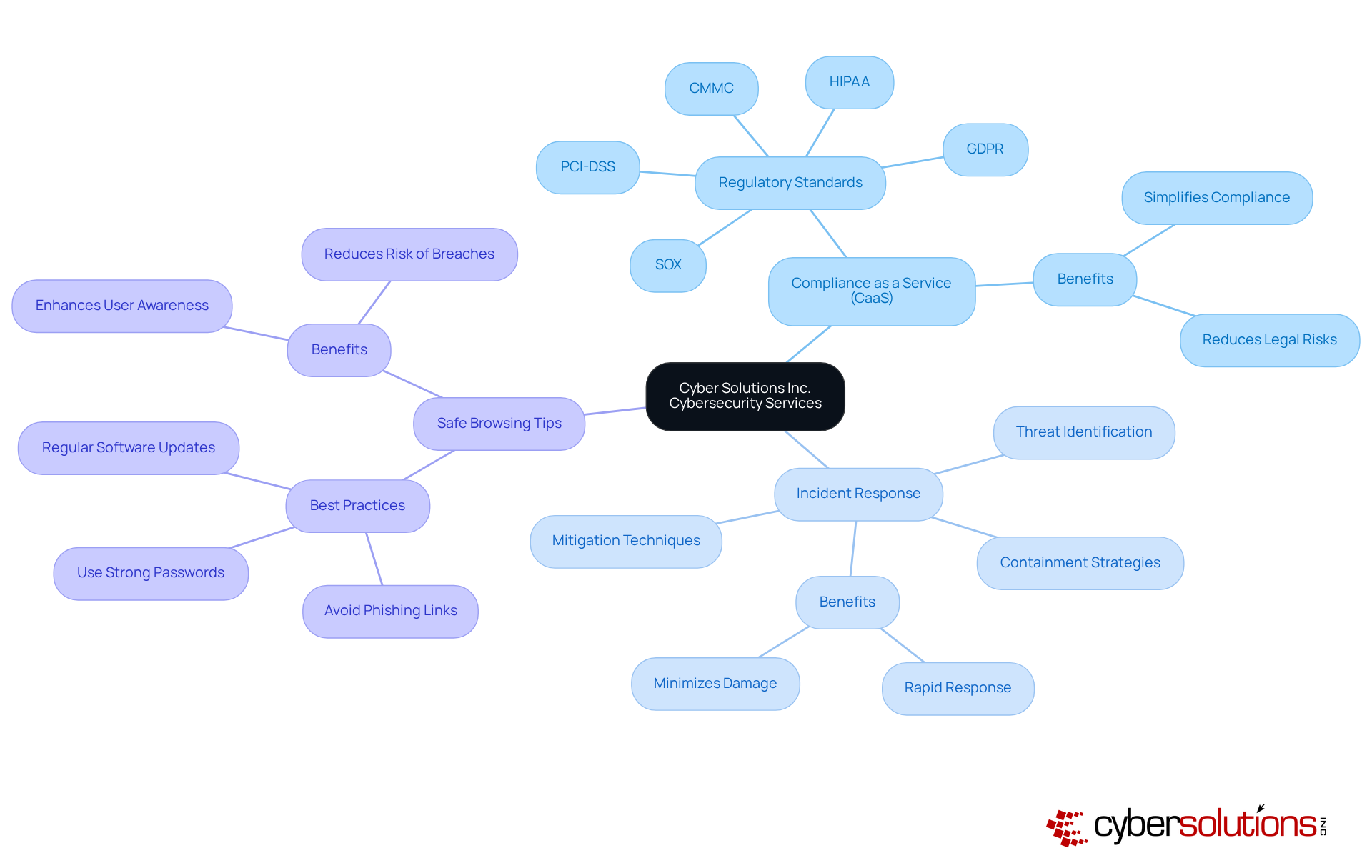
In today's digital landscape, the importance of cybersecurity cannot be overstated. Cyber Solutions Inc. provides a comprehensive range of cybersecurity services designed to offer for businesses. With offerings such as , which simplifies adherence to , along with that rapidly identify, contain, and mitigate , can ensure their teams are equipped to navigate these challenges securely.
The current landscape of cybersecurity threats poses significant risks for organizations, particularly in sectors where sensitive information is at stake. By utilizing these thorough and following , entities can effectively reduce risks linked to web browsing and from emerging . This proactive approach not only enhances security but also fosters trust among stakeholders, ultimately supporting and compliance.
In summary, Cyber Solutions Inc. stands ready to empower businesses with the necessary tools to combat , ensuring a secure and compliant operational environment.
Regularly updating your browser is a critical yet straightforward strategy that aligns with to bolster . This proactive measure is one of the that addresses that cybercriminals actively seek to exploit. A recent revealed that over 1,000 vulnerabilities were fixed in the latest , significantly reducing . C-suite leaders must establish and enforce policies mandating that all employees adhere to by updating their browsers to the latest versions. Implementing not only mitigates the but also enhances overall .
Furthermore, implementing can further strengthen defenses by ensuring that only approved applications run on your network, effectively blocking unauthorized software and malware. Real-world examples, such as the cyber-attack on Suffolk County Council, demonstrate that organizations prioritizing and have successfully thwarted potential breaches. This reinforces the necessity of these practices in today’s digital landscape. As one expert noted, 'Proactive measures and continuous vigilance are crucial for safeguarding digital assets against evolving threats.

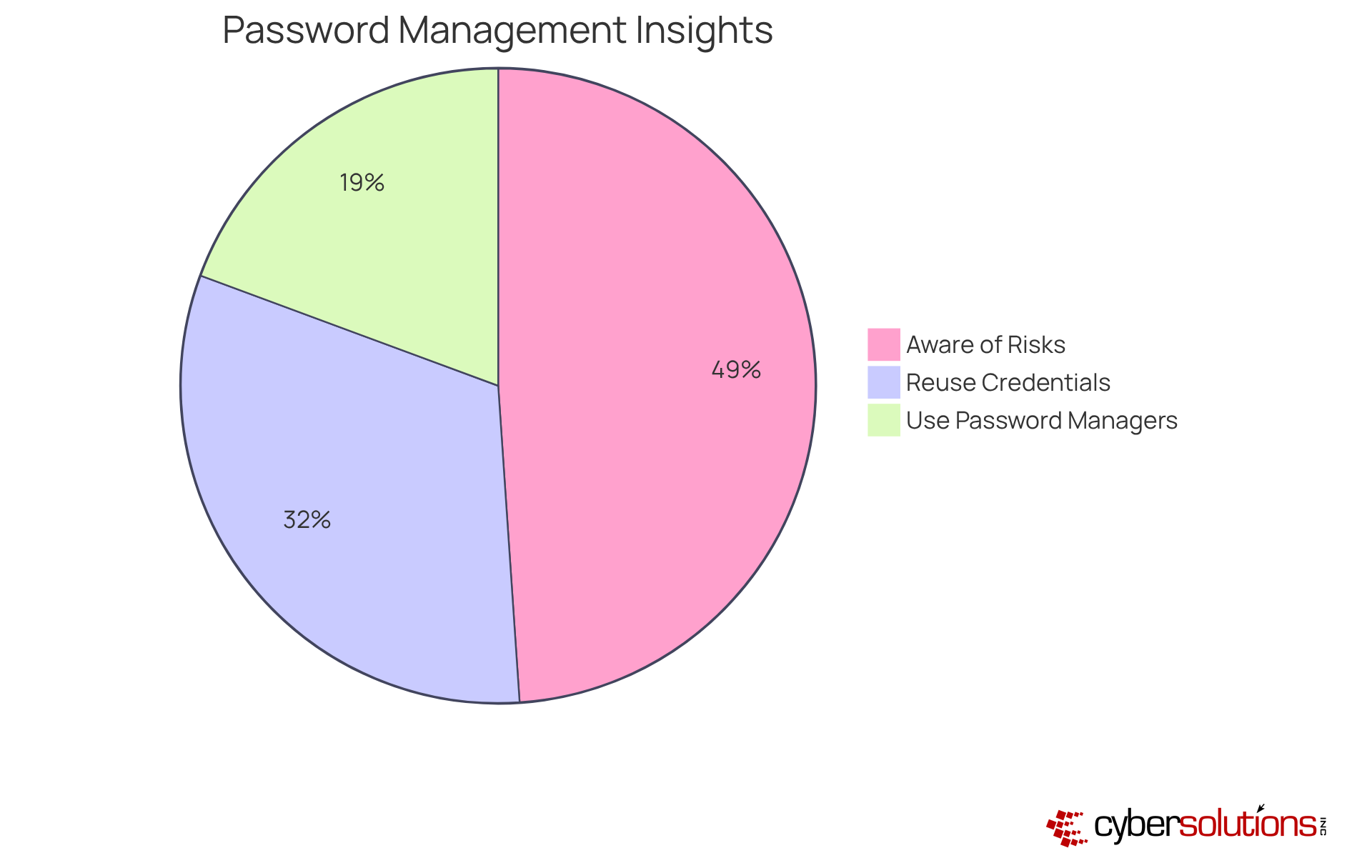
In today's digital landscape, employing robust and distinctive credentials for every account is crucial for protecting sensitive information. C-suite executives must promote the use of , which not only create complex codes but also keep them secure. This practice effectively minimizes the risk of reusing credentials, a significant vulnerability, as despite knowing the associated risks. Notably, , highlighting a concerning gap between understanding and behavior.
Moreover, organizations that adopt can enhance their overall security stance. These tools support adherence to , which require specific . Currently, 36% of American adults subscribe to , with 30% utilizing these tools to safeguard their access codes, indicating a growing awareness of their significance.
Cybersecurity specialists emphasize that robust and distinct access keys are essential; however, they also stress that once a key is compromised, its strength becomes meaningless. By utilizing , entities can not only enhance but also reduce the risks linked to credential theft, which is involved in . Furthermore, 81% of hacking-related breaches in corporate environments arise from weak or reused access credentials. This is essential for C-suite executives seeking to safeguard their organizations from evolving .
Activating across all accounts is imperative for . In a landscape rife with threats, relying solely on passwords is simply insufficient. 2FA introduces a crucial —such as a text message or an authentication app—making unauthorized access significantly more challenging for attackers.
by , thereby against . This proactive measure not only but also instills confidence among stakeholders regarding the organization's .

C-suite leaders must strongly advise employees against using for accessing sensitive information. In today's digital landscape, statistics reveal that 73% of , often connecting to unsecured networks in public spaces. This alarming practice exposes companies to considerable risks, as is a frequent target for .
If accessing confidential information is unavoidable, employees should or a . Implementing these measures can drastically reduce the likelihood of information interception by malicious actors. Moreover, businesses should proactively instruct their workforce on the and provide to promote the use of company-sanctioned tools and secure connections. This approach not only but also fortifies the overall of the organization.

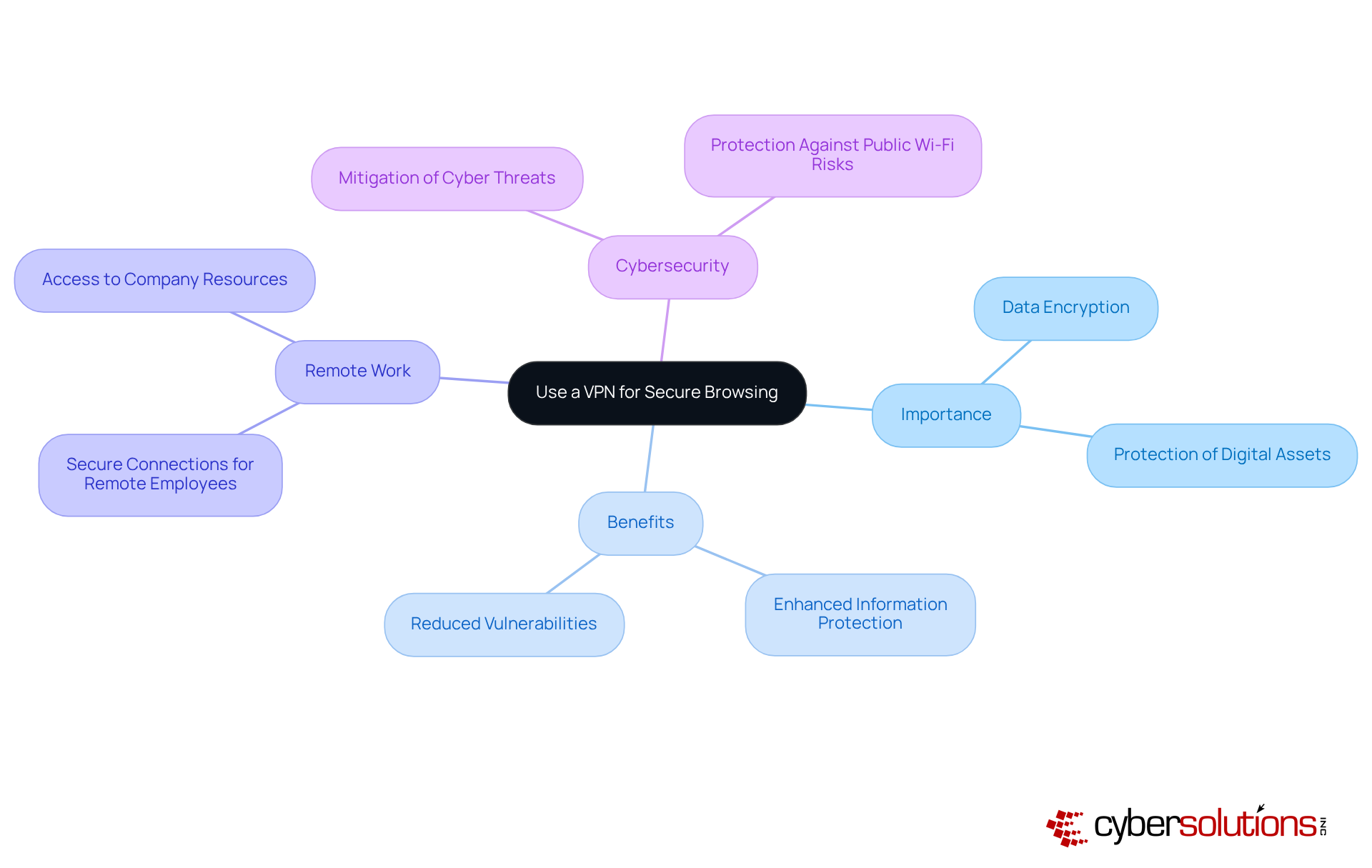
Implementing a VPN is not just a precaution; it is essential for securing internet connections, especially when dealing with sensitive information. In an era where are rampant, a , significantly reducing the risk of interception by cybercriminals. This makes it an indispensable tool for who prioritize the .
For organizations with remote employees, VPN solutions do more than just ; they bolster . Numerous success stories illustrate this point, with businesses reporting enhanced information protection and reduced vulnerabilities following the implementation of VPN technology. As remote work becomes increasingly prevalent, the demand for grows, ensuring that remains protected, even on public Wi-Fi networks.
By adopting a VPN, leaders can foster a , empowering employees to work confidently from any location. This approach not only preserves the integrity of communications and information but also reinforces the organization's commitment to cybersecurity. In a landscape fraught with challenges, the adoption of VPN technology is a proactive step toward safeguarding the future.
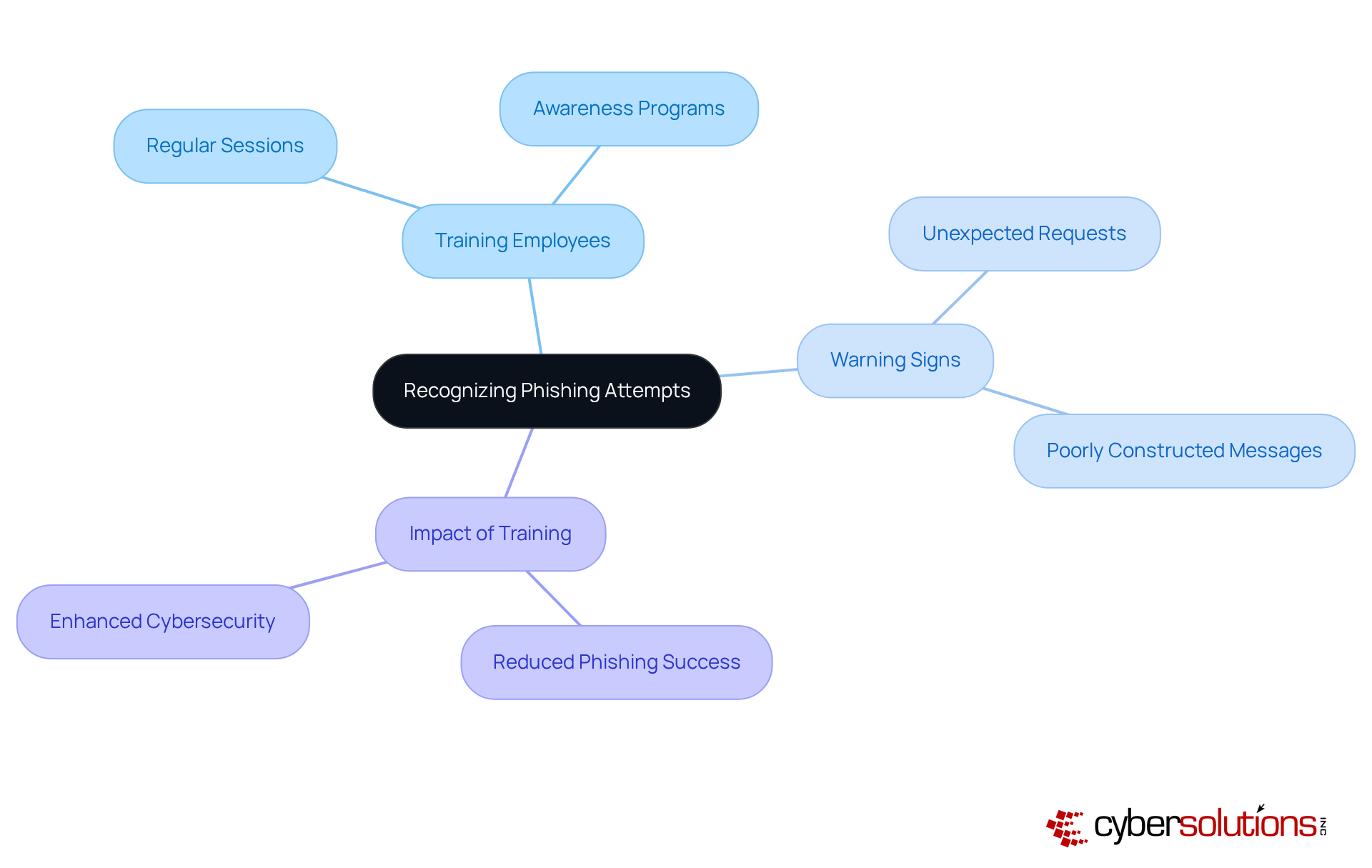
must prioritize training employees to identify , which frequently manifest as suspicious emails or links. In today's digital landscape, where , with the skills to recognize warning signs, such as unexpected requests for or poorly constructed messages. This proactive approach is vital in thwarting phishing attacks, particularly when studies indicate that over 15% of employees fall victim to such schemes.
Organizations that have implemented have reported significant reductions in successful . This showcases the effectiveness of these initiatives and underscores the . By doing so, companies can enhance their overall and protect sensitive data from malicious actors. In an era where the stakes are higher than ever, ; it is a necessity.
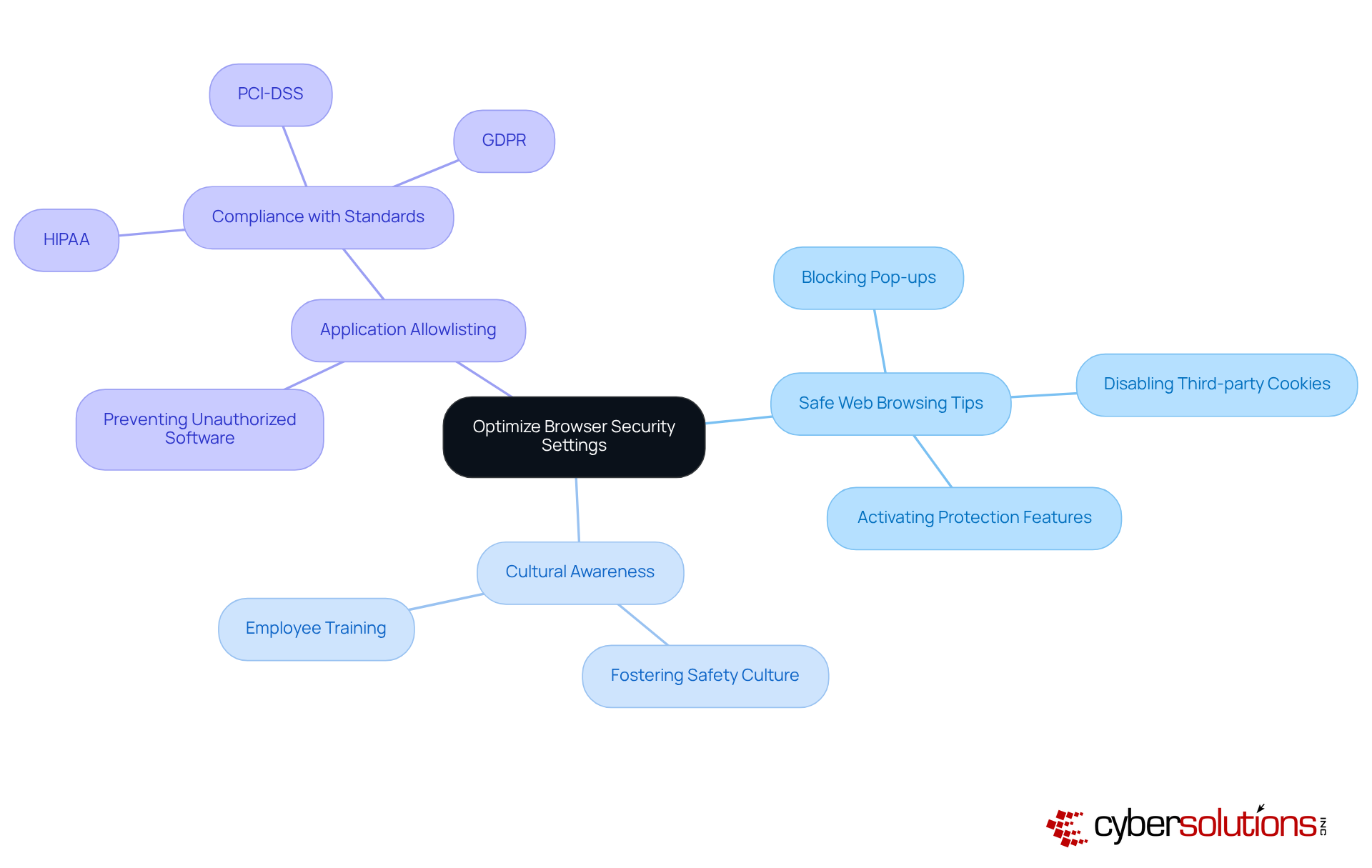
Implementing , such as customizing , is essential for safeguarding against malware and various online threats. C-suite leaders must actively foster a culture of awareness regarding safety among employees by encouraging them to review and customize their browser settings, incorporating . Key adjustments as include:
Research indicates that 76% of Americans believe companies should improve their information protection efforts, underscoring the increasing need for . Furthermore, 92% of Americans express concern about their online privacy, highlighting the necessity for organizations to take proactive measures in this area. Notably, 44% of data breaches involve exposure of personal information, emphasizing the stakes involved in neglecting browser security.
In addition to browser settings, implementing can significantly enhance a company's . By allowing only approved applications to run, organizations can proactively prevent malware, ransomware, and unauthorized software from executing. This approach not only reduces the attack surface but also helps for standards such as HIPAA, PCI-DSS, and GDPR.
Organizations that implement , along with and , not only reduce risks but also enhance their overall cybersecurity stance. By creating an environment where employees are prepared to handle their browser protection efficiently, companies can greatly lessen their susceptibility to cyber threats by providing . C-suite leaders should implement these changes as to ensure a safer browsing experience for their teams.
Installing trustworthy protection software is vital for defending against malware and other cyber threats. C-suite leaders must ensure that all devices within the organization are equipped with current , which offers against potential attacks. Organizations focusing on have noted , with efficient software solutions able to block more than 90% of recognized malware threats.
The effect of keeping up-to-date cannot be emphasized enough; outdated systems are prime targets for cybercriminals, as they often exploit unpatched vulnerabilities. Entities that neglect to enhance their protective measures encounter a 200% rise in data breaches, highlighting the importance of proactive .
Incorporating into your security framework is a critical step in enhancing your entity's defenses. This approach prevents unauthorized applications from executing and significantly , making it harder for attackers to exploit vulnerabilities. By permitting only sanctioned applications to operate, entities can successfully prevent malware, ransomware, and zero-day attacks before they inflict damage. Additionally, supports , ensuring that your organization adheres to strict data protection protocols.
Expert insights show that combining advanced protective solutions, such as Next-Generation Antivirus (NGAV) with machine learning capabilities, improves the ability to identify and counteract emerging threats. Organizations employing AI and automation for protection save an average of $2.22 million each year compared to those that do not, demonstrating the . These solutions not only safeguard sensitive data but also bolster overall organizational resilience against cyberattacks.
Recent advancements in include features like automated endpoint isolation, which can contain malware and prevent the spread of infections, and secure web gateways, which provide an additional layer of defense by monitoring and filtering web traffic in real time, along with . Continuous monitoring of application activity is also crucial, as it ensures immediate identification and blocking of unauthorized software attempts. By implementing these latest protective solutions, including , organizations can significantly reduce the risks linked to malware and ensure a strong cybersecurity stance.

Consistent oversight and evaluation of are paramount in maintaining a robust protective posture against . C-suite leaders must champion the and endorse the exclusive use of those sourced from trusted providers. This proactive strategy significantly mitigates the risk of vulnerabilities that cybercriminals may exploit. For instance, during the Cyberhaven attack, nearly 400,000 users were impacted due to a compromised extension, underscoring the potential hazards of unmonitored browser tools. Furthermore, statistics reveal that a considerable percentage of employees manage , frequently without sufficient oversight, leading to security gaps.
To alleviate these risks, organizations should implement comprehensive that delineate clear guidelines on approved extensions and conduct regular audits to identify potentially harmful ones. Expert recommendations indicate that thorough inspections of installed extensions, along with ongoing about , are essential safe web browsing tips for . By cultivating a culture of vigilance and compliance regarding , organizations can fortify their overall and effectively guard against emerging .
 for better security. Each box represents an action or decision point, guiding you through the process of review, approval, and education.](https://cdn.prod.website-files.com/66b3b47207dab975dd682b0d/69016642fbbc2aee3c4cdd9c_bgmurcic-follow-the-steps-in-this-chart-to-see-how-to-effectively-manage-browser-extensions-for-better-security-each-box-represents-an-action-or-decision-point-guiding-you-through-the-process-of-review-approval-and-education.webp)
In a landscape where cyber threats are continually evolving, the imperative for C-suite leaders to prioritize safe web browsing practices cannot be overstated. By adopting a proactive approach to cybersecurity, executives can significantly bolster their organization’s defenses against potential breaches. The strategies outlined here underscore the necessity of implementing robust security measures—from regular browser updates to the use of strong passwords and two-factor authentication—ensuring that sensitive information remains well-protected.
Key insights, such as the importance of:
highlight the multifaceted nature of online security. Each recommendation serves as a crucial component in constructing a comprehensive cybersecurity framework that not only safeguards data but also fosters trust among stakeholders. Organizations that embrace these safe web browsing tips are better equipped to navigate the complexities of the digital landscape.
The significance of these practices extends beyond mere compliance; they embody a commitment to protecting digital assets in a world where security breaches can lead to dire consequences. C-suite leaders are urged to champion these initiatives within their organizations, cultivating a culture of vigilance and responsibility. By taking decisive action and prioritizing cybersecurity, businesses can not only shield their sensitive information but also ensure long-term success and resilience in the face of emerging threats.
What services does Cyber Solutions Inc. provide for cybersecurity?
Cyber Solutions Inc. offers a comprehensive range of cybersecurity services, including Compliance as a Service (CaaS) for regulatory adherence and Incident Response solutions to identify, contain, and mitigate cyber threats.
Why is it important for organizations to follow safe web browsing tips?
Following safe web browsing tips helps organizations reduce risks associated with web browsing, safeguard sensitive information, enhance security, foster trust among stakeholders, and support business continuity and compliance.
How can regularly updating a browser improve cybersecurity?
Regularly updating a browser addresses known vulnerabilities that cybercriminals exploit, significantly reducing potential attack vectors and enhancing overall organizational security.
What is application allowlisting and how does it contribute to cybersecurity?
Application allowlisting is a security practice that ensures only approved applications run on a network, effectively blocking unauthorized software and malware, thereby strengthening defenses against cyber threats.
What is the significance of using strong passwords for online accounts?
Using strong and unique passwords for every account is crucial for protecting sensitive information and minimizing the risk of credential theft, which is involved in a significant percentage of data breaches.
How can credential managers enhance security for organizations?
Credential managers create complex passwords and securely store them, reducing the risk of reusing credentials and helping organizations adhere to security frameworks that require specific credential management practices.
What statistics highlight the risks associated with weak or reused passwords?
59% of users admit to reusing credentials despite knowing the risks, and 81% of hacking-related breaches in corporate environments arise from weak or reused access credentials.
What proactive strategies can C-suite executives implement to safeguard their organizations from cyber threats?
C-suite executives can implement safe web browsing tips, enforce browser updates, utilize application allowlisting, and promote the use of credential managers to enhance security and protect against evolving cyber threats.