
In today's digital landscape, where cyber threats are not just common but increasingly sophisticated, businesses are confronted with the formidable task of protecting their digital assets. Managed security services cloud solutions have emerged as a crucial lifeline, equipping organizations with the expertise and resources needed to enhance their cybersecurity posture and ensure operational resilience. As companies navigate this intricate environment, one pressing question arises: how can they effectively leverage these services to safeguard against threats while simultaneously driving efficiency and compliance in their operations?
Cyber Solutions Inc. stands at the forefront of managed security services cloud, providing a comprehensive suite that significantly bolsters . In a world where cyber threats loom large, the importance of robust cybersecurity cannot be overstated. With 24/7 surveillance, rapid , and meticulous compliance oversight, organizations are equipped to withstand and recover from effectively.
Recent statistics reveal that companies leveraging see a remarkable . This underscores the vital role these services play in enhancing operational resilience. As the is projected to grow from USD 39.47 billion in 2025 to USD 66.83 billion by 2030, it’s evident that businesses are increasingly recognizing the necessity of outsourcing their cybersecurity needs.
Consider the real-world implications: organizations that partner with not only achieve better outcomes but also enhance their - an essential factor in today’s stringent digital landscape. The BFSI sector exemplifies this trend, , driven by the imperative to secure financial transactions and protect sensitive customer data.
The benefits of managed protection extend beyond mere threat detection; they encompass cost-effectiveness, scalability, and access to cutting-edge . As organizations navigate an evolving threat landscape, the latest trends indicate a shift towards AI-driven threat identification and proactive incident response strategies. This evolution further emphasizes the importance of tailored protective measures in fostering long-term resilience.
In conclusion, Cyber Solutions Inc. distinguishes itself as a leader in delivering managed protection services that not only safeguard digital assets but also empower businesses to thrive in an increasingly complex and demanding environment.

is a crucial pillar of Cyber Solutions' . In today's digital landscape, where are ever-evolving, the cannot be overstated. By leveraging advanced danger detection technologies, enterprises can identify and respond to potential risks in real-time, significantly reducing the likelihood of and operational disruptions.
This proactive approach not only protects sensitive information but also lessens the , which can average a staggering $4.45 million per breach. For instance, organizations that implement have reported enhanced visibility into their security posture, enabling them to swiftly detect and remediate vulnerabilities. Recent advancements in automation and AI have streamlined these processes, allowing for quicker recognition of threats and more efficient incident response.
As cyber threats continue to evolve, utilizing managed security services cloud for continuous monitoring remains essential for and ensuring . Are you prepared to safeguard your organization against these persistent threats? Cyber Solutions offers the expertise and tools necessary to navigate this increasingly complex digital landscape.

Investing in is not just a choice; it's a necessity for businesses aiming to thrive in today's digital landscape. are evolving rapidly, and organizations must adapt to protect their assets effectively. By outsourcing cybersecurity needs, companies can significantly reduce costs associated with hiring and training internal personnel, which often poses a .
Companies that choose to outsource their cybersecurity functions can achieve average . This allows them to allocate resources more effectively, enhancing their overall operational efficiency. Moreover, the managed security services cloud provides access to advanced technologies and specialized knowledge that would typically be prohibitively expensive for many organizations to obtain independently. This in managed security services cloud not only strengthens protective measures but also fosters a more robust .
Organizations utilizing report . This ultimately leads to a more . Additionally, Cyber Solutions employs a layered recovery approach, featuring a to ensure that threats are contained swiftly. Financial analysts note that the return on investment from managed protective offerings can be substantial, with numerous companies experiencing faster product launches and decreased downtime.
Is your organization ready to embrace the future of cybersecurity? By partnering with Cyber Solutions, you can navigate the complexities of cybersecurity with confidence, ensuring your business remains resilient against emerging threats.

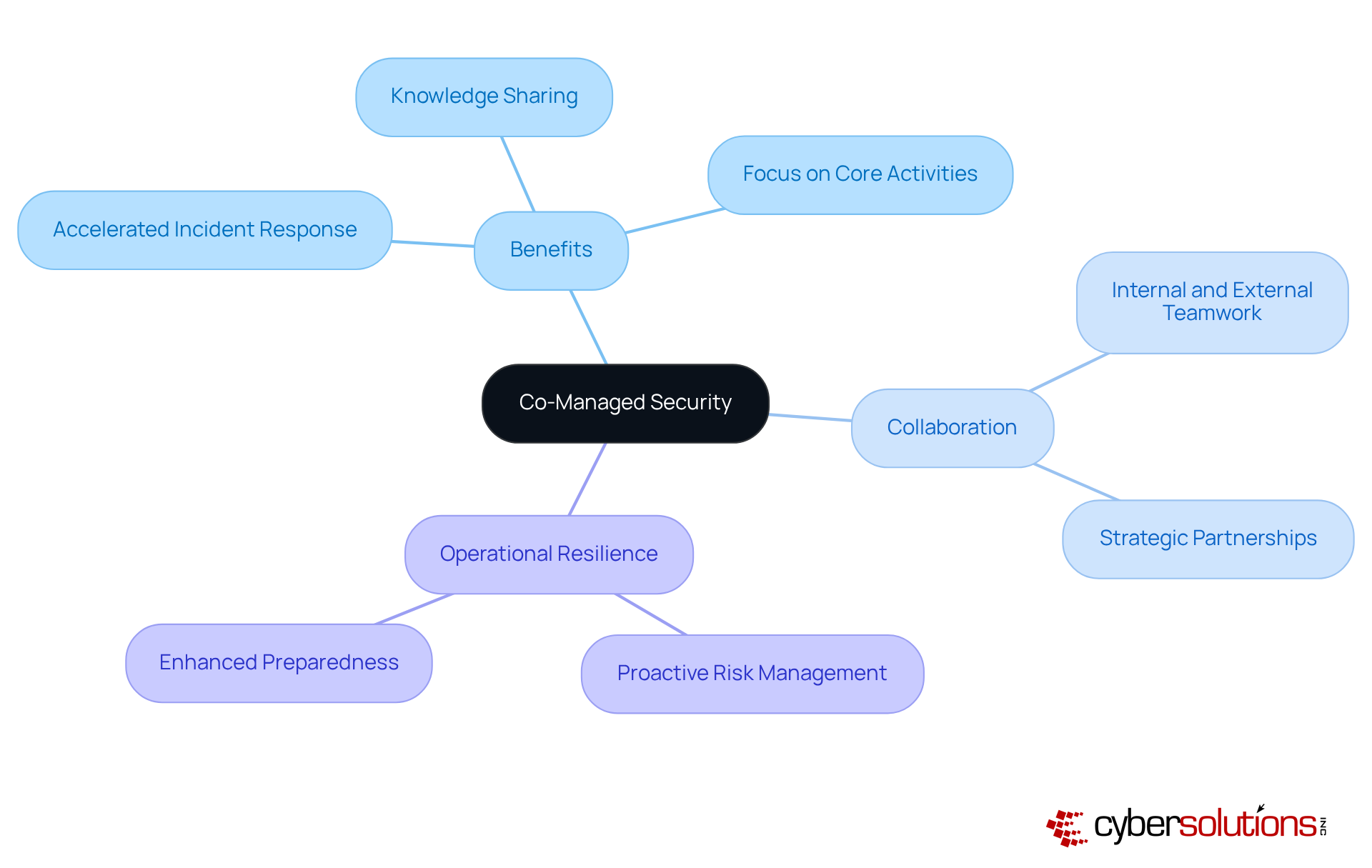
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations striving to protect sensitive information. from Cyber Solutions Inc. offer a strategic advantage for entities looking to bolster their . By partnering with , companies can effectively tackle without overburdening their existing personnel.
This collaboration not only accelerates times but also fosters essential knowledge sharing, significantly . As , leveraging external expertise allows internal teams to concentrate on core activities while ensuring robust defenses against evolving threats.
The partnership between internal and external resources is vital for navigating the complexities of modern cyber risks. This approach ultimately leads to and a proactive management strategy. Are you ready to elevate your ? Cyber Solutions is here to help you face these challenges head-on.
In today's digital landscape, are not just a necessity; they represent a critical component of organizational resilience. Cyber Solutions Inc. stands out by seamlessly integrating their with existing vendor solutions. This approach allows organizations to without the burden of complete overhauls.
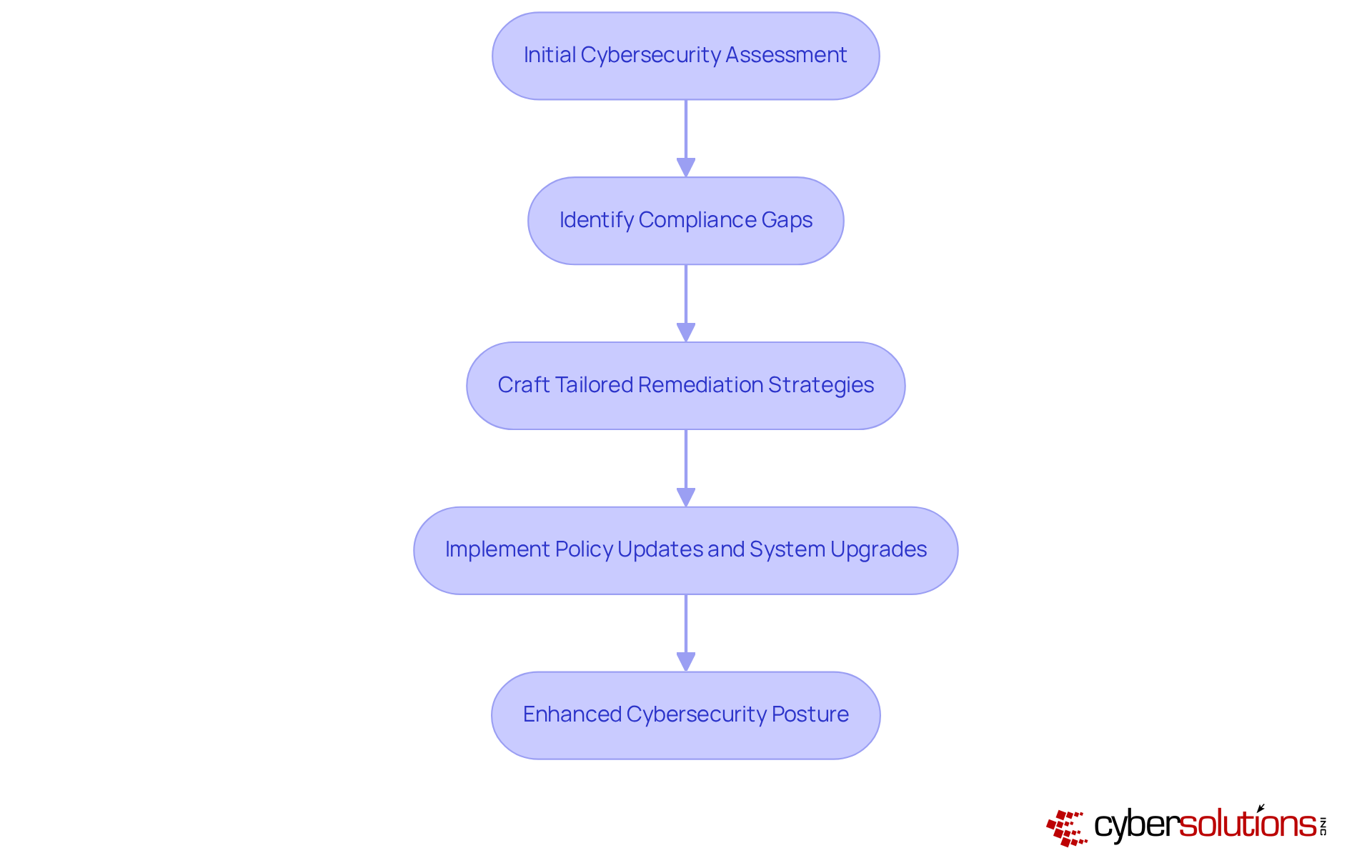
But why is this integration so vital? The reality is that organizations face an ever-evolving array of and compromise sensitive data, highlighting the need for managed security services cloud. By conducting an initial and gap analysis, Cyber Solutions identifies compliance gaps and crafts , including policy updates and system upgrades. This proactive method not only but also maximizes ROI by improving efficiency and reducing costly downtime.
Imagine a scenario where all elements of your . This is achievable with Cyber Solutions, as they enable companies to attain higher effectiveness in their protective measures. By adhering to , organizations can ensure that their sensitive information remains secure.
In conclusion, the integration of managed security services cloud with vendor solutions is not merely an option; it's a aiming to fortify their defenses against cyber threats. Are you ready to take the next step in enhancing your cybersecurity posture?
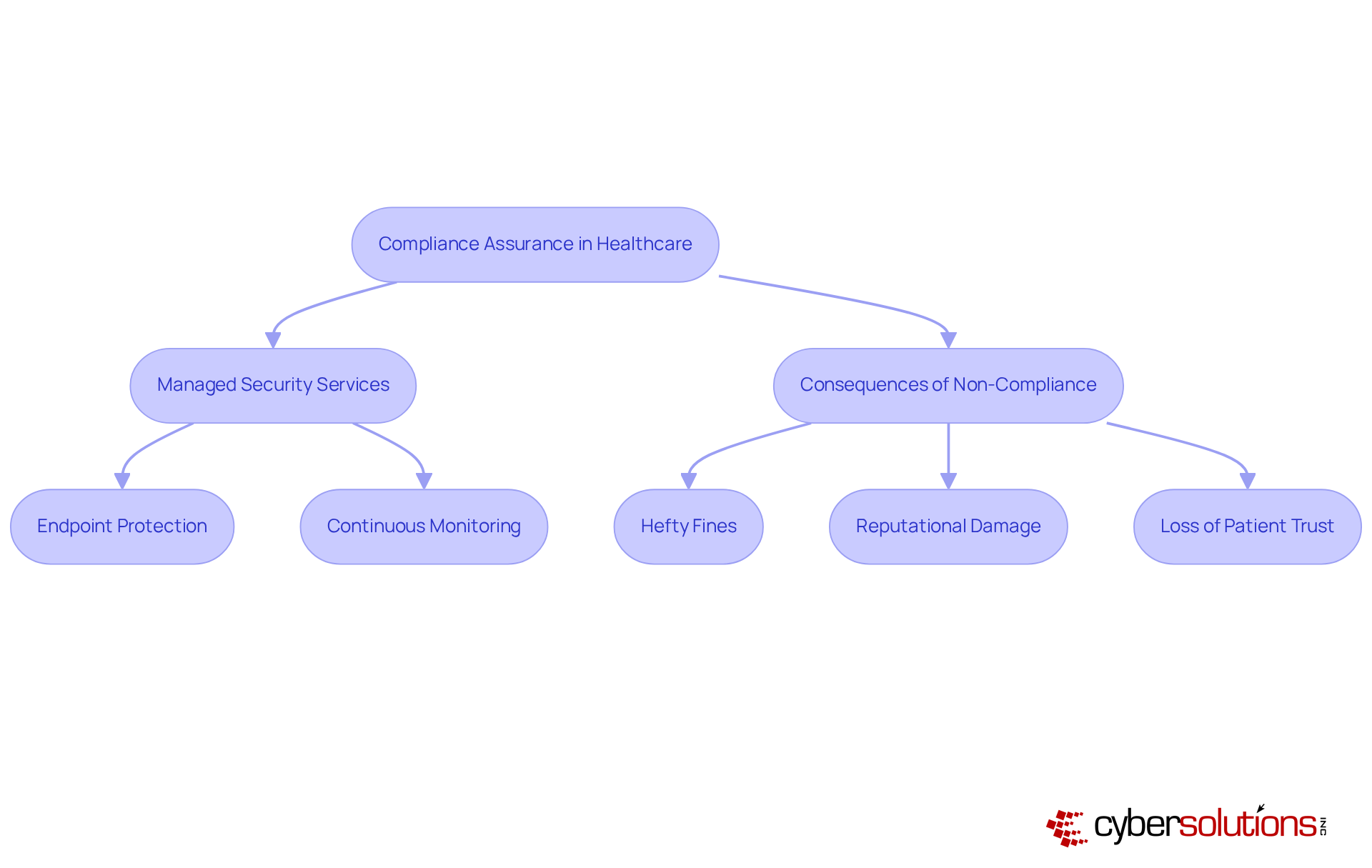
In today's digital landscape, the importance of cybersecurity in healthcare cannot be overstated. With increasing threats from cybercriminals, healthcare organizations face that demand immediate attention. The from Cyber Solutions Inc. provide comprehensive , guiding entities through complex regulatory environments. By embedding protection into every aspect of their IT offerings, Cyber Solutions ensures that clients remain compliant with .
Cyber Solutions' tailored managed security services cloud and Cybersecurity Services are specifically designed for regulated industries. These services include proactive measures like:
These measures not only mitigate risks but also and trustworthiness in the market. For CFOs and C-Suite leaders focused on , this approach is not just beneficial; it’s essential.
Consider the implications of non-compliance:
Can your organization afford to take that risk? By partnering with Cyber Solutions, healthcare organizations can , ensuring they are not only compliant but also positioned for growth in a competitive landscape.
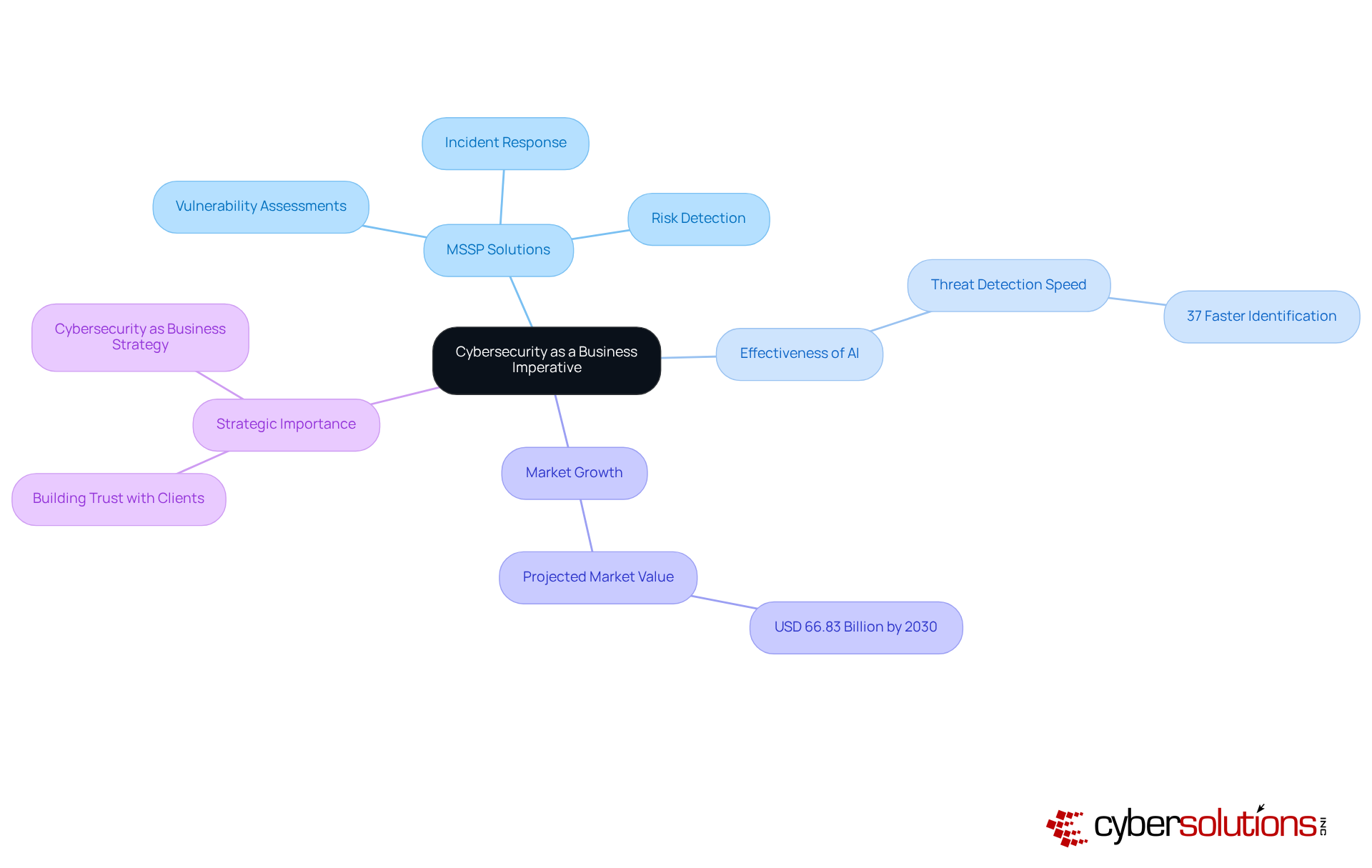
In today's digital landscape, cybersecurity is not just an IT concern; it's a critical business imperative. Cyber Solutions Inc. stands at the forefront of the landscape, delivering innovative solutions that effectively tackle the evolving nature of cyber risks. Their comprehensive offerings - ranging from to rapid and thorough - are meticulously designed to protect businesses from a multitude of cyber threats.
Statistics underscore the effectiveness of these advanced MSSP solutions. Organizations leveraging AI-driven risk detection capabilities can identify threats 37% faster than those relying solely on traditional methods. Moreover, the global is projected to soar, reaching USD 66.83 billion by 2030, driven by the increasing demand for . This growth signals a broader acknowledgment among C-suite leaders that .
As organizations face increasingly sophisticated cyber threats, the leadership at Cyber Solutions Inc. emphasizes the importance of embedding cybersecurity into the overall business strategy. By framing cybersecurity as a facilitator of business success, they build trust and highlight the necessity of investing in robust protection measures. This approach ensures that clients are well-equipped to navigate the complexities of modern digital environments.
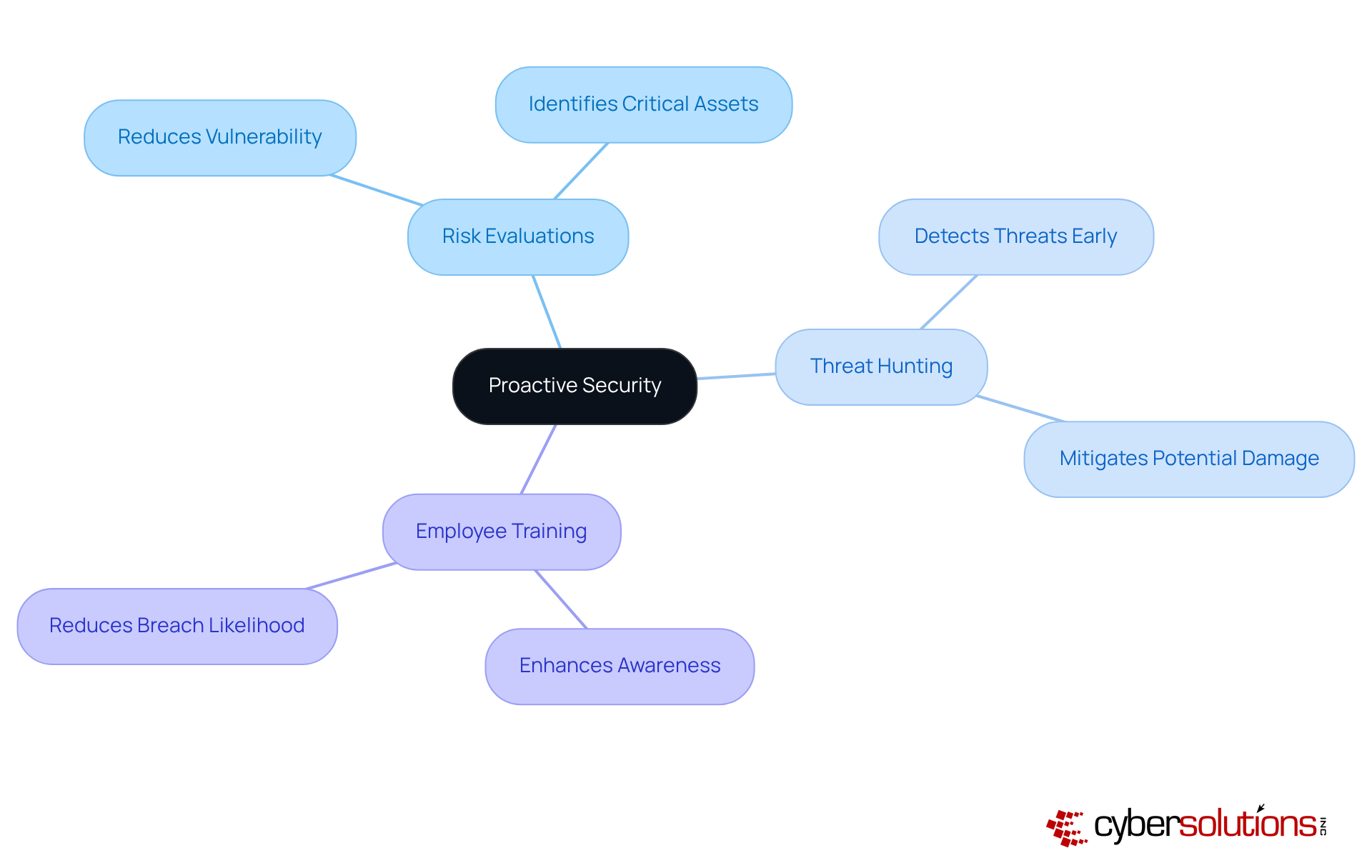
is not just beneficial; it’s essential for Cyber Solutions Inc. In today’s landscape, where , organizations must concentrate on strategies that foresee and mitigate potential risks before they escalate. , active , and are crucial in fostering a culture of awareness.
Organizations that prioritize these proactive measures can significantly reduce their vulnerability to cyberattacks. In fact, effective has been shown to decrease the likelihood of breaches by up to 65%. As , the implementation of threat hunting becomes increasingly vital. This approach enables organizations to detect and address dangers before they can inflict harm.
Security experts emphasize that is not merely a reactive measure; it’s a fundamental component of a . By cultivating an environment where employees are consistently educated about security risks, businesses can enhance their overall resilience against the growing sophistication of cyber threats. Are you ready to take the necessary steps to protect your organization?
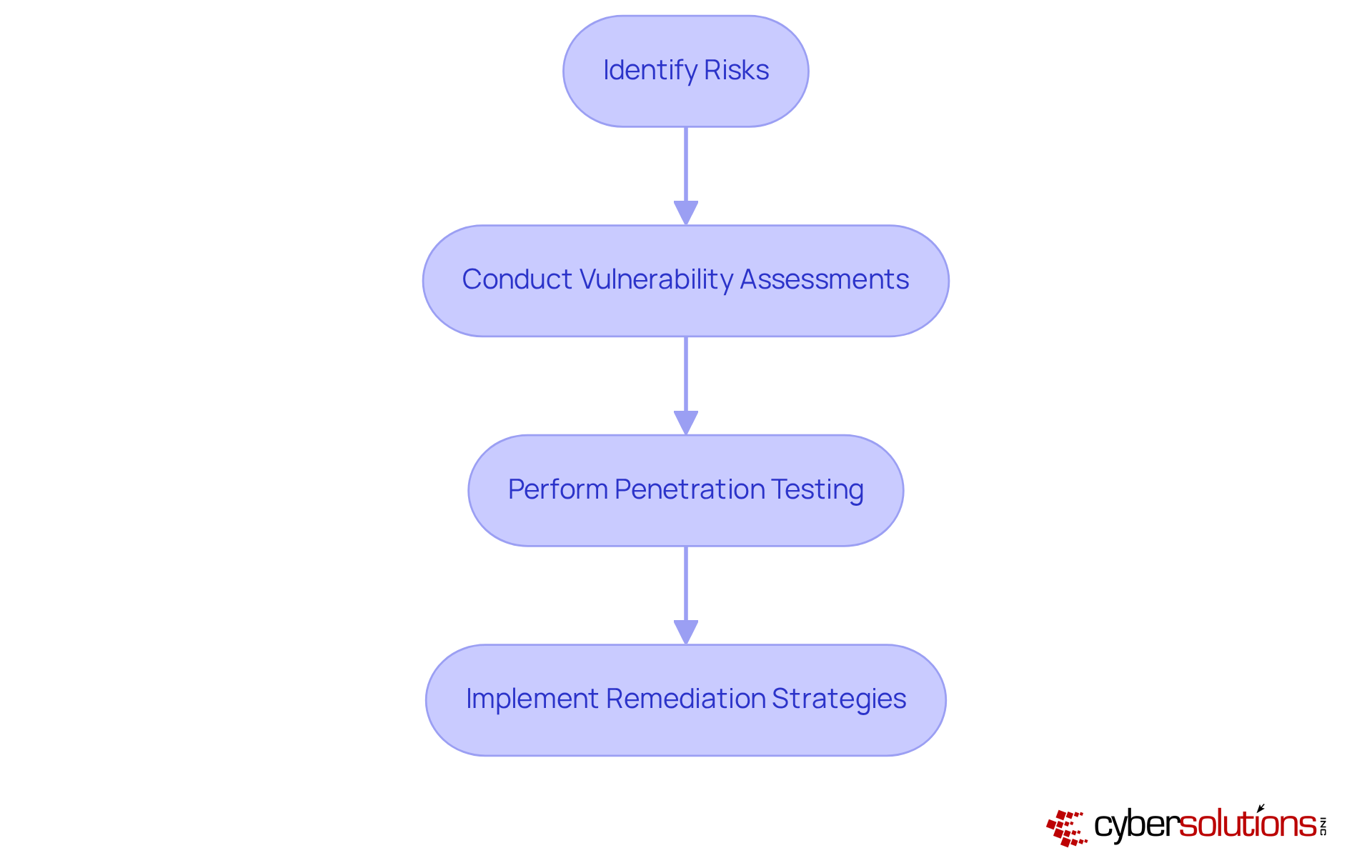
Cybersecurity is no longer just an IT concern; it’s a critical business imperative. Cyber Solutions Inc. implements a robust that prioritizes the identification and mitigation of risks through a . This program includes regular and , essential for uncovering potential weaknesses in a company's defenses. By tailoring remediation strategies to fit each unique environment, Cyber Solutions empowers businesses to , significantly reducing their risk exposure.
Current trends reveal a startling reality: the has plummeted to just five days. This alarming statistic underscores the urgency for companies to conduct frequent assessments. Experts assert that regular penetration testing is not merely a compliance checkbox; it’s a vital component of a . This proactive stance enables organizations to stay ahead of and adapt to the ever-evolving cybersecurity landscape.
Successful case studies illustrate how organizations have effectively mitigated risks through consistent penetration testing and . For instance, companies that have integrated automated vulnerability management processes report increased effectiveness in detecting and prioritizing vulnerabilities, ultimately leading to better protective measures. By embedding these practices into their operational frameworks, businesses can ensure .
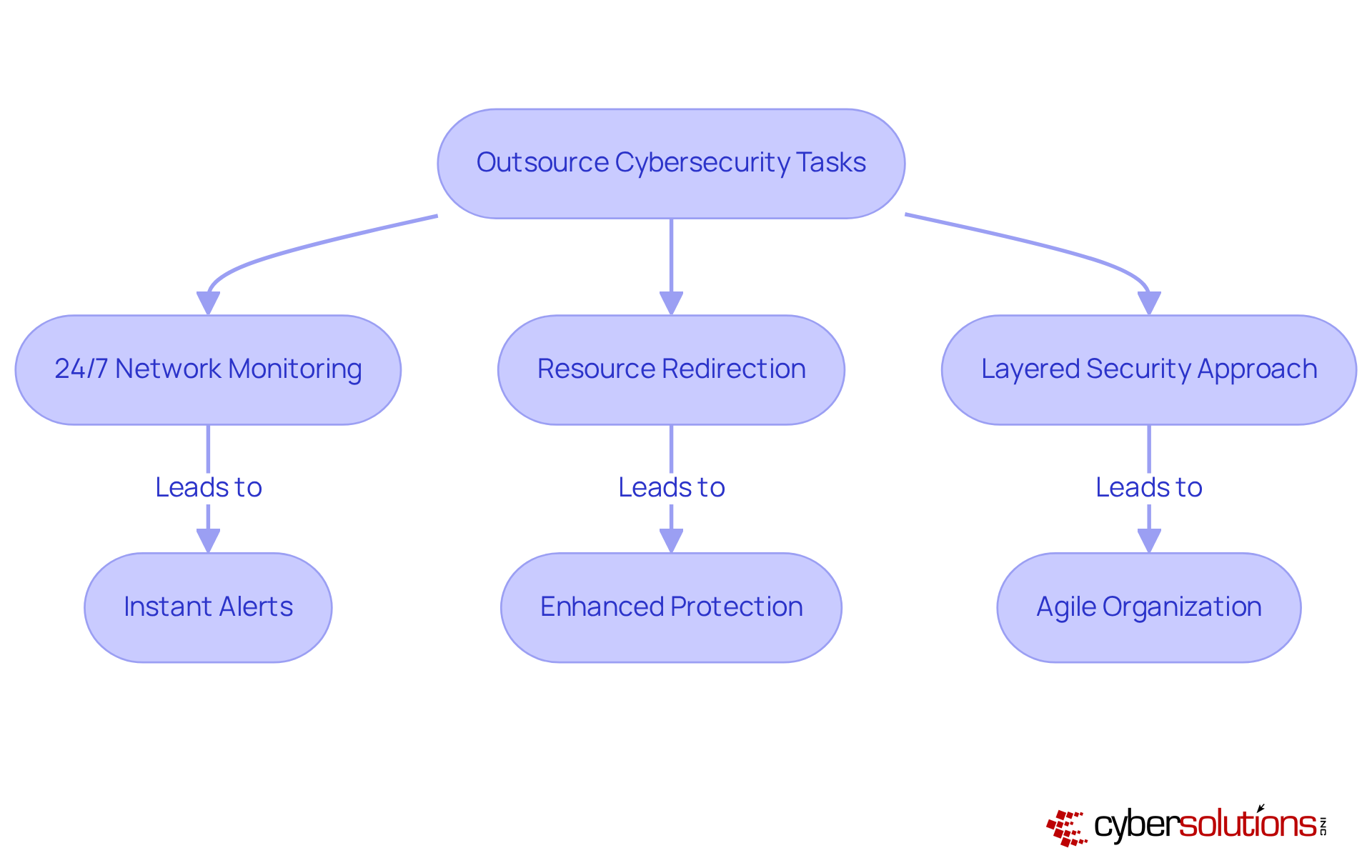
In today's digital landscape, ; it's a critical component of operational success. Managed services from Cyber Solutions Inc. significantly enhance protection while driving . With of your network, Cyber Solutions identifies anomalies and that empower swift action to prevent downtime or breaches.
By outsourcing cybersecurity tasks to , organizations can redirect internal resources toward essential business activities, ensuring their protection needs are managed by specialists. This strategic advantage enables companies to operate more effectively, ensuring that are tailored to their specific requirements.
The outcome? A more agile and resilient organization, adept at navigating the ever-evolving digital landscape. Cyber Solutions employs a layered approach that includes:
Fostering . Are you ready to elevate your and safeguard your organization against emerging threats?
The importance of managed security services in building business resilience is undeniable. In a world where cyber threats are becoming increasingly sophisticated, organizations must prioritize comprehensive protection strategies. Cyber Solutions Inc. stands out as a leader in this field, providing tailored managed security services that not only protect digital assets but also enable businesses to flourish in the face of evolving threats.
Key insights reveal the diverse advantages of these services. With:
Organizations can achieve operational efficiency while meeting regulatory compliance. The integration of cutting-edge technologies and proactive security measures underscores the critical need for robust cybersecurity frameworks in today’s digital landscape.
Businesses must grasp the strategic value of investing in managed security services. By collaborating with experts like Cyber Solutions Inc., organizations can strengthen their defenses, minimize vulnerabilities, and confidently navigate the complexities of the cyber landscape. Embracing these solutions is not just a reactive approach; it’s a proactive strategy for ensuring long-term resilience and success in an increasingly digital world.
What services does Cyber Solutions Inc. provide?
Cyber Solutions Inc. offers comprehensive managed security services that include 24/7 surveillance, rapid incident response, and compliance oversight to enhance business resilience against cyber threats.
How do managed protection solutions improve threat detection and response?
Companies using managed protection solutions have shown a 60% improvement in their ability to detect and respond to threats, significantly enhancing operational resilience.
What is the projected growth of the managed security services market?
The global market for managed security services is expected to grow from USD 39.47 billion in 2025 to USD 66.83 billion by 2030.
Which sector is the largest adopter of managed protection services?
The Banking, Financial Services, and Insurance (BFSI) sector is the largest adopter of managed protection services, driven by the need to secure financial transactions and protect sensitive customer data.
What are the benefits of utilizing managed protection services?
Benefits include cost-effectiveness, scalability, access to advanced cybersecurity expertise, improved compliance with regulatory standards, and enhanced threat detection capabilities.
How does continuous monitoring contribute to cybersecurity?
Continuous monitoring allows organizations to identify and respond to potential risks in real-time, reducing the likelihood of data breaches and operational disruptions.
What financial impact can cyber incidents have on organizations?
The average cost of a data breach can be around $4.45 million, making proactive cybersecurity measures essential for financial protection.
How much can companies save by outsourcing their cybersecurity functions?
Companies that outsource their cybersecurity can achieve cost reductions of 30% to 60%, allowing for better resource allocation and operational efficiency.
What is the role of automation and AI in managed security services?
Automation and AI streamline threat detection and incident response processes, enabling quicker recognition of threats and more efficient remediation.
What support does Cyber Solutions provide for incident recovery?
Cyber Solutions employs a layered recovery approach that includes a 24-hour on-site support team to swiftly contain threats and ensure business continuity.