
Creating secure copies of information is not just a technical necessity; it’s a critical business imperative that can determine the fate of an organization. For C-suite leaders, mastering the art of backup and data recovery is essential - not only for safeguarding assets but also for ensuring operational resilience against ever-evolving threats. With staggering statistics revealing that a significant percentage of businesses face irretrievable data loss, one must ask: how can executives effectively navigate the complexities of data protection to secure their organizations against potential disasters?
In today’s landscape, the stakes are higher than ever. Cybersecurity threats are rampant, and healthcare organizations are particularly vulnerable. The implications of data breaches can be devastating, leading to financial loss, reputational damage, and compromised patient care. Therefore, understanding the unique challenges faced by CFOs in this arena is crucial.
Cyber Solutions can address these challenges effectively, providing the tools and strategies necessary to protect sensitive information. By investing in robust data protection measures, organizations can not only mitigate risks but also foster trust among stakeholders. The question remains: are you prepared to safeguard your organization’s future?
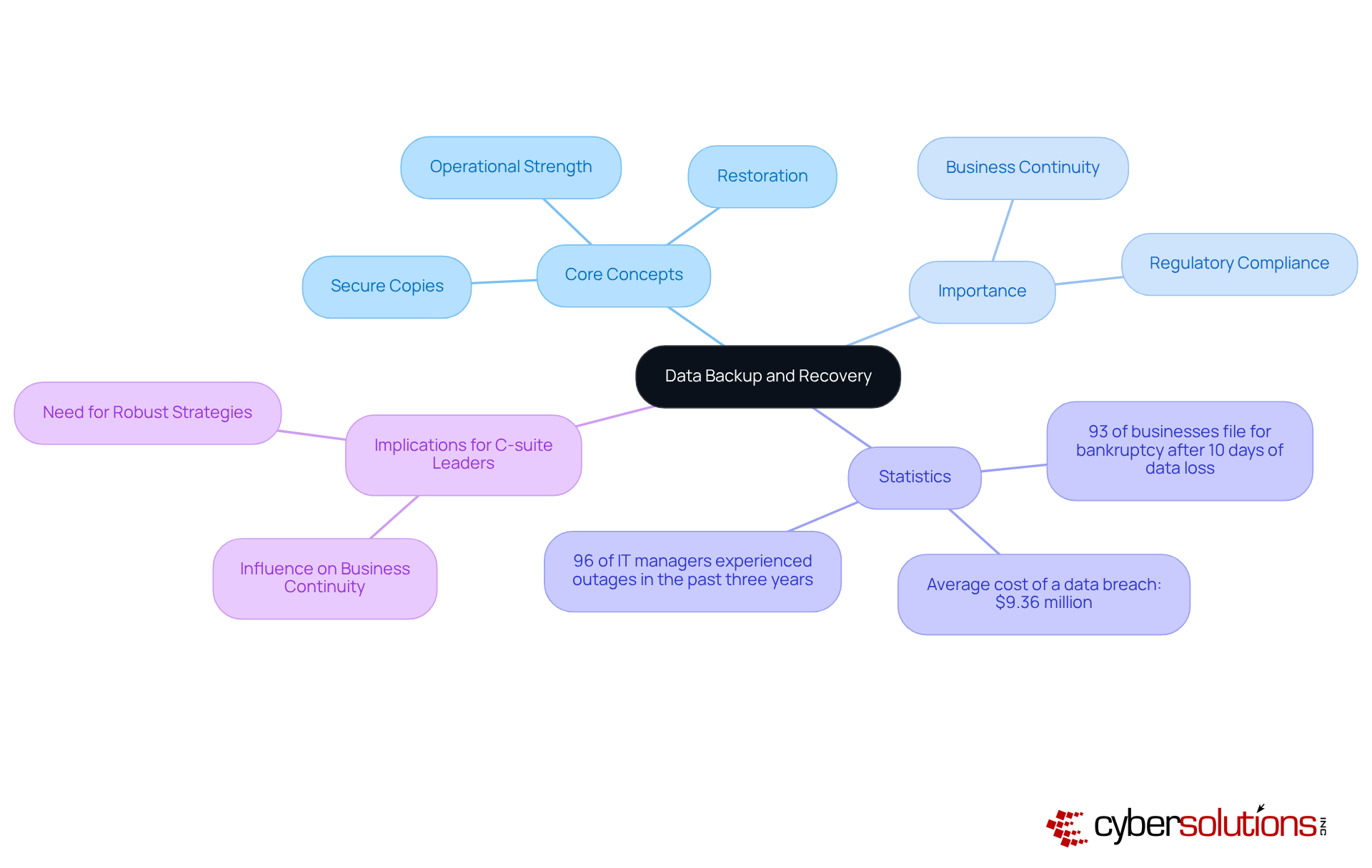
Creating secure copies of information is crucial for backup and data recovery to protect against theft, corruption, or disasters. Restoration, on the other hand, involves retrieving this information when needed. For C-suite leaders, understanding these concepts is not just beneficial; it’s essential. They directly influence business continuity and regulatory compliance.
Efficient tactics for backup and data recovery significantly reduce risks associated with information loss. They also bolster operational strength, enabling organizations to swiftly recover from events like cyberattacks or natural disasters. In fact, organizations that prioritize these practices report a marked decrease in downtime and financial losses during recovery efforts. Consider this: 93% of businesses that experience prolonged information loss lasting over 10 days file for bankruptcy within a year. This statistic underscores the necessity of robust strategies for backup and data recovery.
Moreover, the average cost of a data breach in the United States hovers around $9.36 million, highlighting the severe financial implications of inadequate information protection. Practical examples abound, showcasing how organizations have enhanced their operational resilience through comprehensive information restoration strategies. This reality emphasizes the critical need for C-suite leaders to prioritize these initiatives in their business continuity planning.
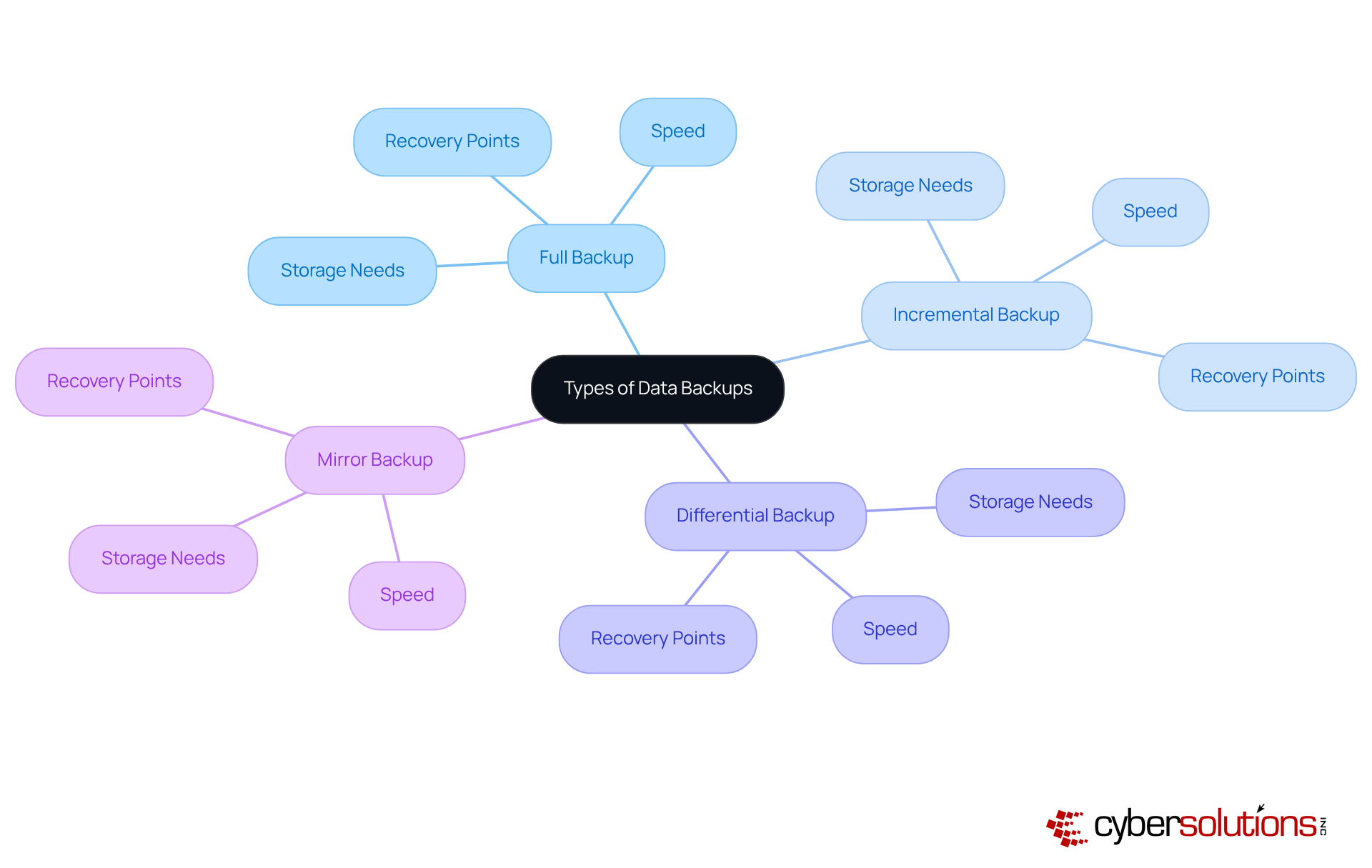
Data copies are crucial for safeguarding organizational information, manifesting in various forms: full, incremental, differential, and mirror copies. A complete copy captures all information at a specific moment, providing a comprehensive recovery point, but it requires significant storage space and time. In contrast, incremental saves only preserve changes made since the last save, making them more storage-efficient and quicker to execute. Differential saves find a middle ground by capturing all changes since the last complete save, offering faster restoration than incremental saves while accumulating more storage needs over time. Mirror copies create an accurate, real-time replica of the information, ensuring immediate protection against loss.
C-suite executives must evaluate the significance of their organization's information and restoration objectives when selecting a backup strategy. Adopting the 3-2-1 guideline - maintaining three copies of information on two distinct media types, with one copy stored offsite - greatly enhances protection and restoration capabilities. This approach not only mitigates risks associated with information loss but also aligns with best practices observed in organizations that have successfully navigated recovery challenges. Regular assessments of backups are vital to ensure their effectiveness, and implementing both off-site and on-site recovery strategies is essential for maintaining information integrity and accessibility. In today's evolving threat landscape, a multi-layered protection strategy is imperative; relying solely on the 3-2-1 rule without additional security measures can leave organizations vulnerable.
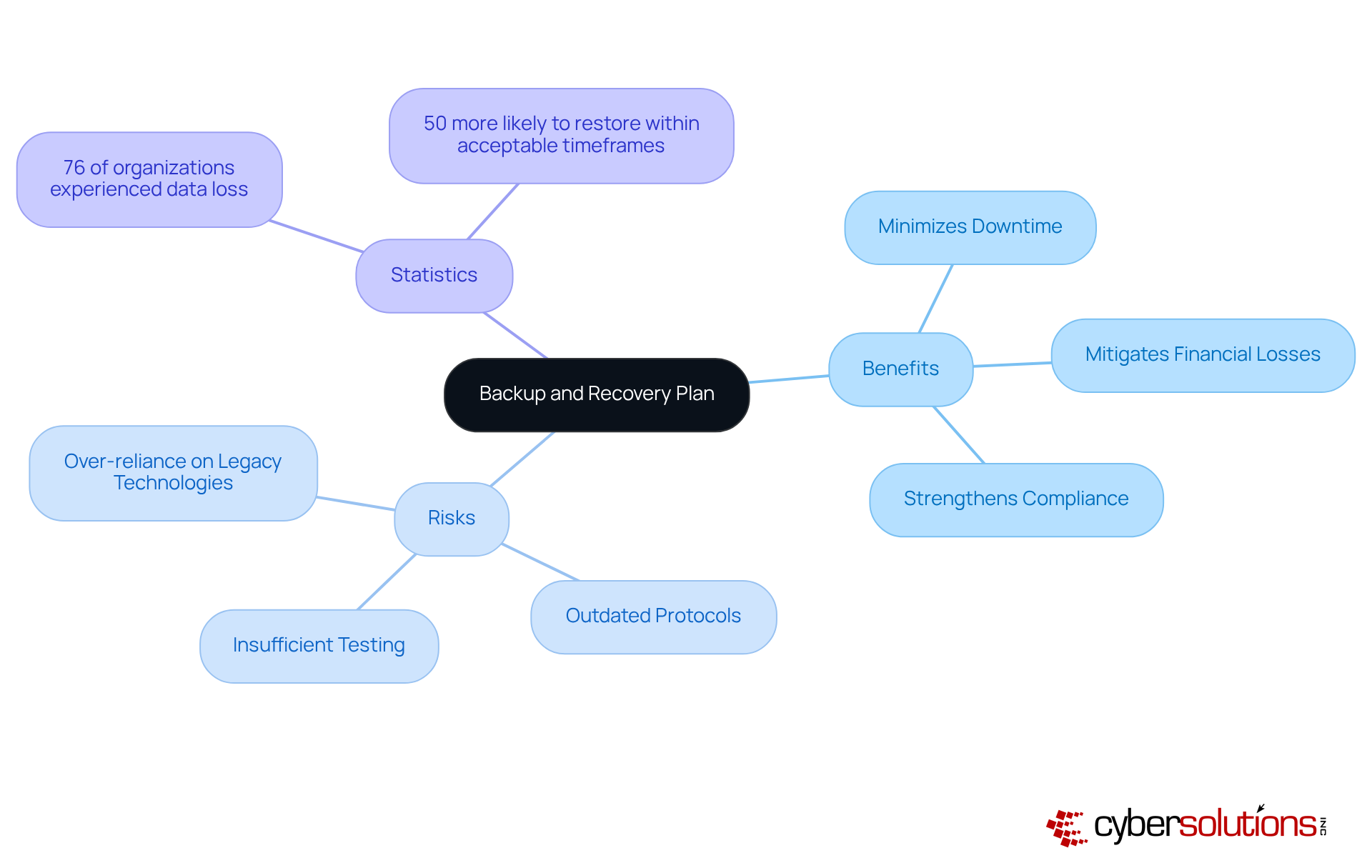
A robust backup and data recovery strategy is essential for safeguarding information and ensuring swift restoration in the event of an interruption. This plan not only minimizes downtime and mitigates financial losses but also strengthens compliance with regulatory requirements. However, organizations face significant risks when their strategies for backup and data recovery fall short. Common pitfalls in backup and data recovery include:
All of which can severely undermine recovery efforts.
Consider this: an astounding 76% of organizations have experienced significant information loss, with 45% of those incidents resulting in irretrievable data. C-suite leaders must prioritize regular reviews and updates of their contingency plans, integrating lessons learned from past incidents and aligning with industry best practices. Notably, organizations with clearly defined backup and data recovery strategies are 50% more likely to restore from information loss events within acceptable timeframes. This statistic underscores the strategic importance of proactive protection measures.
In today’s digital landscape, the importance of robust methods for backup and data recovery cannot be overstated. C-suite leaders, particularly in healthcare, face unique challenges that demand immediate attention. Here are essential strategies to enhance your organization’s data security:
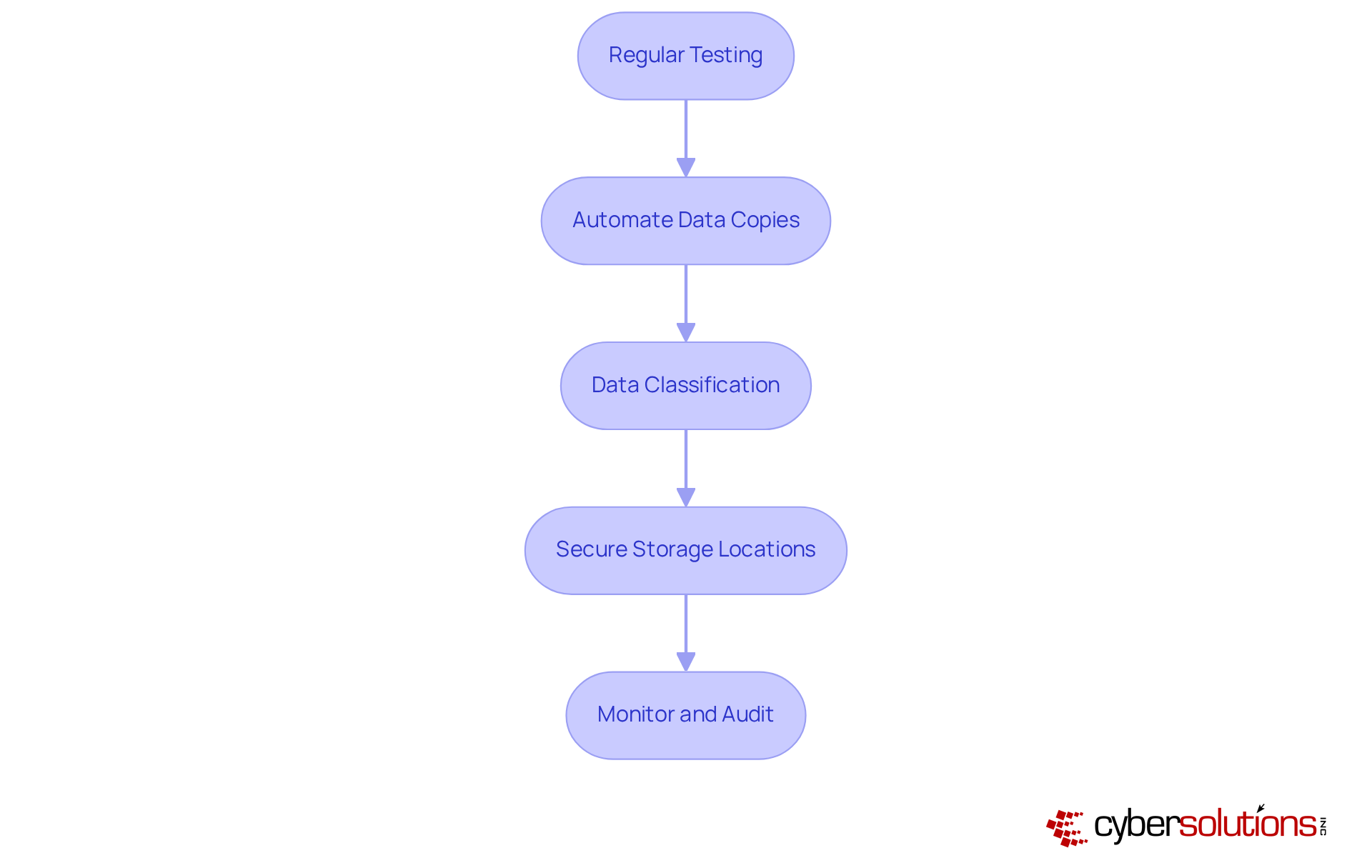
Regular Testing: Conduct frequent assessments of retrieval and recovery procedures. This ensures that backup and data recovery processes can reinstate information swiftly and accurately, minimizing downtime and disruption.
Automate Data Copies: Leverage automation tools to schedule regular data backups. This significantly reduces the risk of human error, ensuring that your data is consistently protected.
Data Classification: Categorize information based on its significance. This prioritization allows for more effective preservation efforts and resource allocation, ensuring that critical data receives the attention it deserves.
Secure Storage Locations: Store copies in multiple locations, including offsite and cloud solutions. This strategy safeguards against physical disasters, providing an extra layer of security for your data.
Monitor and Audit: Regularly monitor backup systems and conduct audits. This practice helps identify vulnerabilities and ensures compliance with regulatory standards, reinforcing your organization’s commitment to data security.
By adopting these best practices, organizations can significantly enhance their data protection strategies, ensuring business continuity and resilience in the face of evolving cybersecurity threats.
Understanding the significance of data backup and recovery is crucial for C-suite leaders. In today's unpredictable business environment, these practices not only safeguard critical information but also ensure the continuity of operations amidst unforeseen disruptions. By prioritizing robust backup and recovery strategies, executives can effectively mitigate risks, comply with regulations, and protect their organizations from potential financial losses.
Key points highlighted throughout this discussion include:
The exploration of different types of backups - such as full, incremental, and mirror - illustrates the need for a well-rounded approach to information preservation. Regular testing, automation, and secure storage are essential strategies that directly contribute to an organization's resilience against data loss.
In conclusion, the call to action for C-suite leaders is clear: prioritize the implementation of robust data backup and recovery strategies. By doing so, organizations not only protect their valuable information but also reinforce their operational integrity in an increasingly complex digital landscape. Embracing these best practices is not merely a response to current threats; it is a proactive measure that lays the foundation for sustainable business success in the future.
What is data backup and recovery?
Data backup refers to creating secure copies of information to protect against theft, corruption, or disasters, while data recovery involves retrieving this information when needed.
Why is understanding data backup and recovery important for C-suite leaders?
Understanding these concepts is essential for C-suite leaders as they directly influence business continuity and regulatory compliance.
How do efficient backup and recovery tactics benefit organizations?
Efficient tactics significantly reduce risks associated with information loss and bolster operational strength, enabling organizations to swiftly recover from events like cyberattacks or natural disasters.
What is the impact of prolonged information loss on businesses?
Organizations that experience prolonged information loss lasting over 10 days are at a high risk, with 93% filing for bankruptcy within a year.
What is the average cost of a data breach in the United States?
The average cost of a data breach in the United States is approximately $9.36 million.
How can organizations enhance their operational resilience?
Organizations can enhance their operational resilience through comprehensive information restoration strategies, which are critical for effective business continuity planning.