
In today's digital landscape, where cyber threats are escalating in both frequency and sophistication, businesses must prioritize the protection of their digital assets. Endpoint Detection and Response (EDR) has emerged as a crucial solution, empowering organizations to monitor, detect, and respond to cyber risks in real-time. As companies confront the serious implications of data breaches and the demands of regulatory compliance, grasping the significance of EDR within the cybersecurity framework is essential.
How can organizations effectively leverage EDR to bolster their security posture amidst the complexities of modern cyber threats? By understanding and implementing EDR strategies, businesses can not only safeguard their assets but also navigate the intricate landscape of cybersecurity with confidence.
The term signifies not just an , but a necessity in today’s digital landscape. With cyber threats evolving at an alarming rate, organizations must continuously monitor, identify, and respond to dangers targeting - laptops, desktops, and servers. Unlike traditional antivirus programs that primarily address known threats, EDR employs sophisticated analytics and machine learning to detect and respond to emerging risks in real-time. This proactive approach is essential, especially considering that a staggering 90% of successful cyberattacks originate from .
By consistently gathering and analyzing data from these endpoints, and potential threats, enabling organizations to mitigate risks before they escalate into significant incidents. The is highlighted by its capability to drastically reduce the average time to identify a breach, currently at 207 days, while . As companies face a , understanding the is crucial for to maintain robust protection and ensure compliance with regulatory standards.
Moreover, Cyber Solutions complements EDR with and alert services that swiftly address anomalies and potential vulnerabilities. With , businesses can effectively prevent downtime or breaches. Continuous monitoring is vital; it helps detect suspicious activities before they escalate into threats, safeguarding organizations from ransomware, phishing, and other malware attacks.
The EDR market is projected to reach USD 32.47 billion by 2033, expanding at a CAGR of 24.6%. This growth highlights the increasing significance and adoption of EDR technologies, which exemplifies the within the cybersecurity landscape. Furthermore, EDR can be integrated with other protective technologies, such as SIEM systems, to provide a more comprehensive defense strategy. Are you ready to fortify your organization’s cybersecurity posture?

In today’s digital landscape, the stakes are higher than ever when it comes to cybersecurity, especially in healthcare. With evolving in sophistication, organizations must prioritize robust security measures. The term '' emphasizes that has emerged as a cornerstone of modern cybersecurity strategies, providing immediate insights into endpoint actions. This capability allows teams to swiftly identify and neutralize threats, ensuring that patient data remains secure.
As regulatory requirements for data protection and privacy tighten, the understanding of becomes even more critical. It not only enhances security but also supports . Organizations leveraging EDR have reported improved compliance outcomes, as these tools facilitate the necessary documentation and monitoring mandated by regulatory frameworks. In fact, by 2026, the impact of EDR on compliance will be even more pronounced, as organizations increasingly depend on these solutions to navigate the complexities of data protection regulations.
Expert opinions underscore the necessity of EDR, highlighting the to address current regulatory compliance challenges. How can organizations effectively showcase adherence to data protection standards while simultaneously mitigating advanced cyber threats? The answer lies in that provide comprehensive visibility and control over endpoint activities. With projected to surpass $10.5 trillion in 2026, the urgency of adopting EDR solutions cannot be overstated.
Moreover, considering that 68% of data breaches stem from human error, the importance of EDR in mitigating risks associated with human factors is paramount. Cyber Solutions stands ready to assist with expert malware removal and system reconstruction services, ensuring that compromised endpoints are thoroughly cleaned, patched, and reimaged as necessary. This layered recovery approach includes identifying vulnerabilities, applying security patches, and reconfiguring systems to bolster overall endpoint security.
By incorporating swift , Cyber Solutions empowers organizations to uphold compliance with industry regulations while effectively managing cyber risks. The time to act is now-don’t let your organization fall victim to the rising tide of cyber threats.

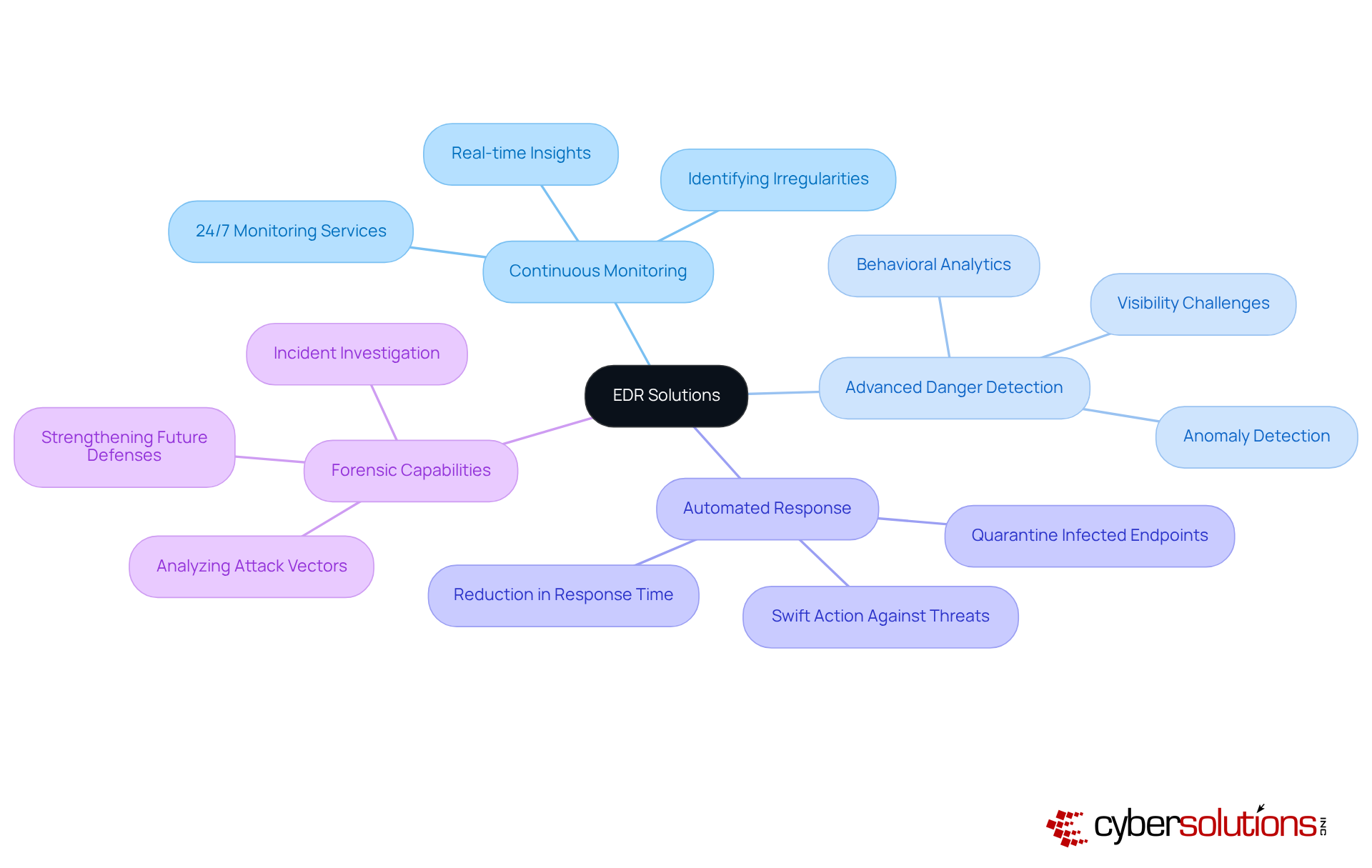
In today's digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations that rely heavily on technology. The EDR meaning in cyber security highlights solutions that stand out with key features like:
Continuous observation allows to monitor endpoint activities in real-time, providing organizations with immediate insights into potential risks. This capability is bolstered by that detect irregularities and vulnerabilities, ensuring that suspicious activities are identified and addressed before they escalate into significant threats.
Advanced risk detection employs behavioral analytics to spot anomalies that may signal a security breach, addressing a critical need for visibility. In fact, 63% of organizations report that lack of visibility is a major barrier to effective endpoint security. are vital, enabling organizations to act swiftly against identified threats. For example, can isolate compromised endpoints or initiate remediation processes automatically, significantly cutting down the average response time to detected threats. Research indicates that organizations using automated EDR tools can achieve a remarkable 65% reduction in the time needed to identify incidents, thereby enhancing overall protection efficiency.
Moreover, EDR solutions offer robust that empower teams to investigate incidents post-breach. This includes analyzing the attack vector and understanding the breach's nature, which is crucial for strengthening future defenses. As cyber threats continue to evolve, it is essential for organizations to understand the edr meaning in cyber security, as it highlights the importance of integrating and automated responses in , along with comprehensive 24/7 network monitoring and alert services, to bolster their cybersecurity posture and effectively mitigate risks. Additionally, Cyber Solutions provides tailored access controls and firewall services that adapt as businesses grow, ensuring that security measures remain effective amidst changing operational needs.
In today's rapidly evolving digital landscape, the importance of cybersecurity cannot be overstated, especially in healthcare. The concept of (EDR), which illustrates the , emerged in the early 2010s, with Anton Chuvakin of Gartner coining the term in 2013. The term represents a , which struggle to keep pace with increasingly sophisticated . Initially designed to address the shortcomings of legacy systems, EDR has transformed dramatically over the years.
The integration of , particularly , has revolutionized EDR capabilities. These innovations enable solutions to detect not only known threats but also previously unidentified vulnerabilities. For example, the introduction of AI in 2018 marked a pivotal shift, enhancing both risk detection and response efficiency. As continue to evolve, evidenced by a staggering 79% increase in indicators of attack since January 2020, the remains a crucial element of modern cybersecurity strategies. It adapts to the dynamic landscape, effectively countering the challenges posed by contemporary cyber adversaries.
The critical role of EDR is further underscored by high-profile incidents such as the NotPetya ransomware attack in 2017 and the SolarWinds breach in 2021. These events highlight the necessity for organizations to implement . As CFOs and decision-makers navigate these challenges, investing in comprehensive becomes imperative. By prioritizing the EDR meaning in cyber security, organizations can safeguard themselves against the ever-growing spectrum of , ensuring a secure environment for their operations.

Understanding the significance of Endpoint Detection and Response (EDR) in cybersecurity is crucial for modern businesses navigating an increasingly perilous digital landscape. In a world where cyber threats are evolving at an alarming rate, can organizations afford to rely solely on traditional security measures? EDR transcends these outdated approaches by offering real-time monitoring and response capabilities, empowering organizations to proactively combat the diverse array of cyber threats targeting their endpoint devices. Integrating EDR into security frameworks is not just advantageous; it is a critical necessity for maintaining robust protection and ensuring compliance with regulatory standards.
Key insights throughout this discussion highlight the importance of:
that EDR solutions provide. Organizations adopting EDR can significantly reduce the time it takes to identify and respond to breaches, thereby enhancing their overall security posture. Moreover, the ability to integrate EDR with other security technologies, such as SIEM systems, further fortifies defenses against sophisticated cyber threats. The projected growth of the EDR market underscores its increasing relevance in cybersecurity strategies, especially as businesses face mounting regulatory requirements and the escalating costs associated with cybercrime.
The urgency for organizations to embrace EDR solutions cannot be overstated. As cyber threats become more complex and prevalent, the need for comprehensive visibility and control over endpoint activities is paramount. By prioritizing EDR, businesses not only bolster their cybersecurity defenses but also enhance their compliance with critical regulations. The time to act is now; investing in EDR is an investment in the future security and resilience of any organization.
What does EDR stand for in cybersecurity?
EDR stands for Endpoint Detection and Response, which is a critical cybersecurity measure focused on monitoring, identifying, and responding to threats targeting endpoint devices like laptops, desktops, and servers.
How does EDR differ from traditional antivirus programs?
Unlike traditional antivirus programs that primarily address known threats, EDR utilizes advanced analytics and machine learning to detect and respond to emerging risks in real-time, providing a more proactive approach to cybersecurity.
Why is EDR important in today's digital landscape?
EDR is essential due to the evolving nature of cyber threats, with 90% of successful cyberattacks originating from endpoint devices. It helps organizations mitigate risks by identifying suspicious activities before they escalate into significant incidents.
How does EDR improve incident response times?
EDR solutions significantly reduce the average time to identify a breach, which is currently 207 days, and enhance incident response times, enabling organizations to react swiftly to potential threats.
What additional services do Cyber Solutions provide to complement EDR?
Cyber Solutions offers 24/7 network monitoring and alert services that quickly address anomalies and potential vulnerabilities, providing instant alerts and real-time insights to prevent downtime or breaches.
What is the projected growth of the EDR market?
The EDR market is projected to reach USD 32.47 billion by 2033, expanding at a compound annual growth rate (CAGR) of 24.6%, indicating the increasing significance and adoption of EDR technologies.
Can EDR be integrated with other security technologies?
Yes, EDR can be integrated with other protective technologies, such as Security Information and Event Management (SIEM) systems, to create a more comprehensive defense strategy against cyber threats.