Introduction
In today's world, where cyber threats are not just increasing but evolving in sophistication, organizations face a pressing challenge: safeguarding their digital assets. Effective cybersecurity risk assessments are not merely a box to check for compliance; they are vital for identifying vulnerabilities and defending against potential attacks. As leaders navigate this intricate landscape, they must ask themselves: how can they ensure their risk assessments are not only comprehensive but also proactive and adaptable to the ever-changing threat environment?
The implications for organizations, particularly in sectors like healthcare, are profound. Cybersecurity is no longer just an IT issue; it’s a critical component of organizational resilience. With the stakes higher than ever, CFOs and decision-makers must understand the unique challenges they face in protecting sensitive data and maintaining trust.
To address these challenges effectively, Cyber Solutions offers a robust framework that empowers organizations to stay ahead of threats. By implementing thorough risk assessments, leaders can gain insights into their vulnerabilities and develop strategies that not only mitigate risks but also enhance their overall security posture.
In this complex landscape, the need for proactive measures is clear. Organizations must prioritize cybersecurity as a fundamental aspect of their operations, ensuring they are equipped to respond to the dynamic nature of cyber threats.
Identify Core Elements of Cybersecurity Risk Assessments
To effectively evaluate security threats, organizations must first recognize the essential components of their safety environment. This understanding is crucial in today’s landscape, where cybersecurity threats are increasingly sophisticated and pervasive. Here are the fundamental elements that should be considered:
- : Cataloging all critical assets-hardware, software, and data-is vital. This inventory not only clarifies what needs protection but also serves as the foundation of a robust security strategy. Cybersecurity leaders consistently emphasize that knowing your assets is paramount.
- : Identifying potential dangers, such as malware, phishing attacks, and insider threats, enables organizations to anticipate challenges. With approximately 90% of , proactive is not just beneficial; it’s essential.
- : Evaluating existing vulnerabilities in systems and processes helps pinpoint weaknesses that could be exploited. Conducting effective s can significantly reduce the likelihood of successful attacks, safeguarding the organization’s integrity.
- : Understanding the potential effects of a successful attack on business operations, reputation, and finances is crucial for prioritizing threats. Organizations that neglect to assess these impacts risk severe financial repercussions, with the .
- : Recognizing applicable , ensures that entities meet their legal obligations while addressing digital security challenges. Compliance is not merely a checkbox; it is integral to maintaining trust and operational integrity.
Incorporating as a proactive measure can further enhance these assessments. By ensuring that only authorized applications can run, organizations can significantly minimize their attack surface and reduce risks associated with unapproved software. Features like centralized management and continuous monitoring of application activity facilitate early , aligning with compliance needs and bolstering overall security posture. By focusing on these essential elements, organizations can establish a strong framework for their cyber security risk assessments, effectively addressing the most pressing vulnerabilities while aligning with strategic business goals.

Analyze the Threat Landscape and Vulnerabilities
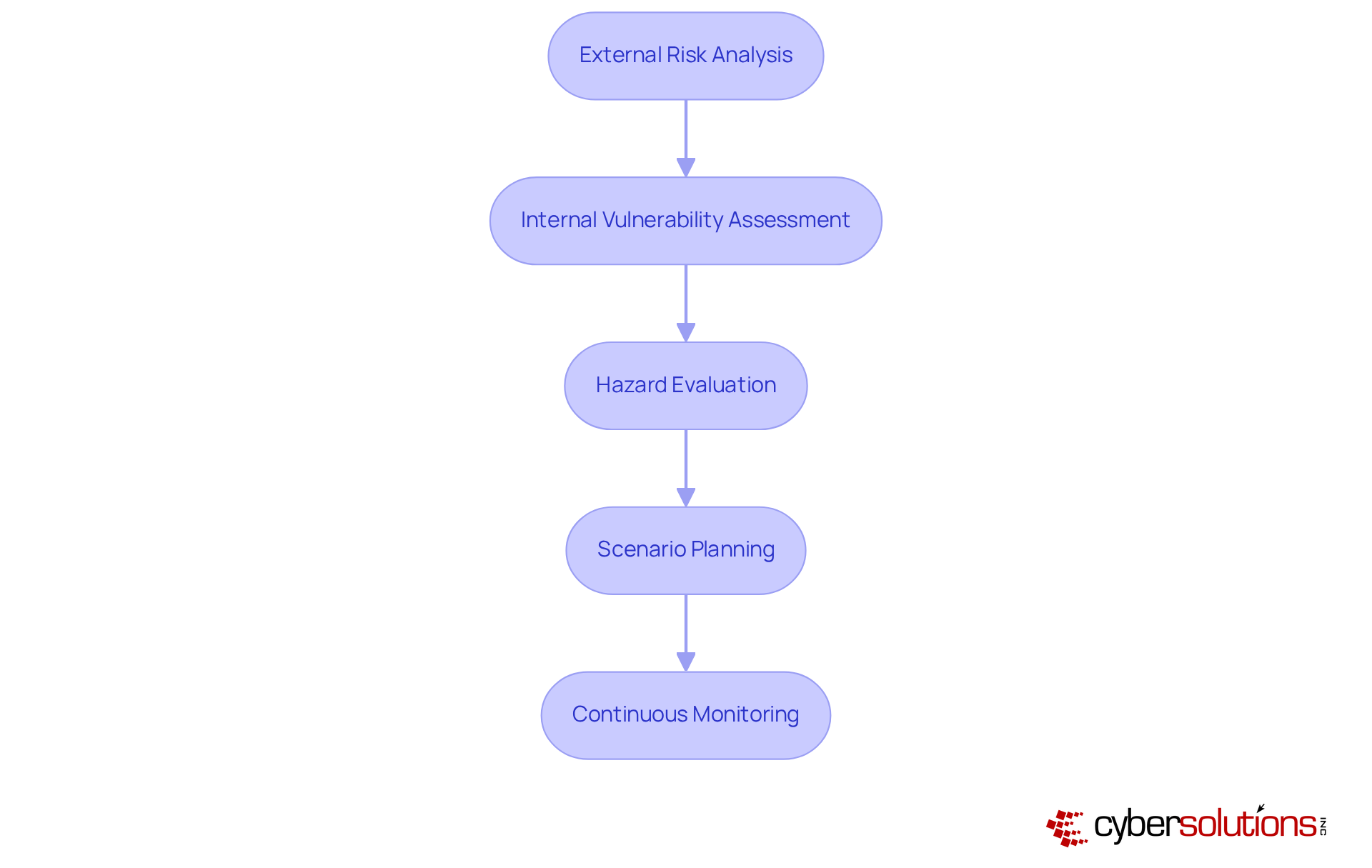
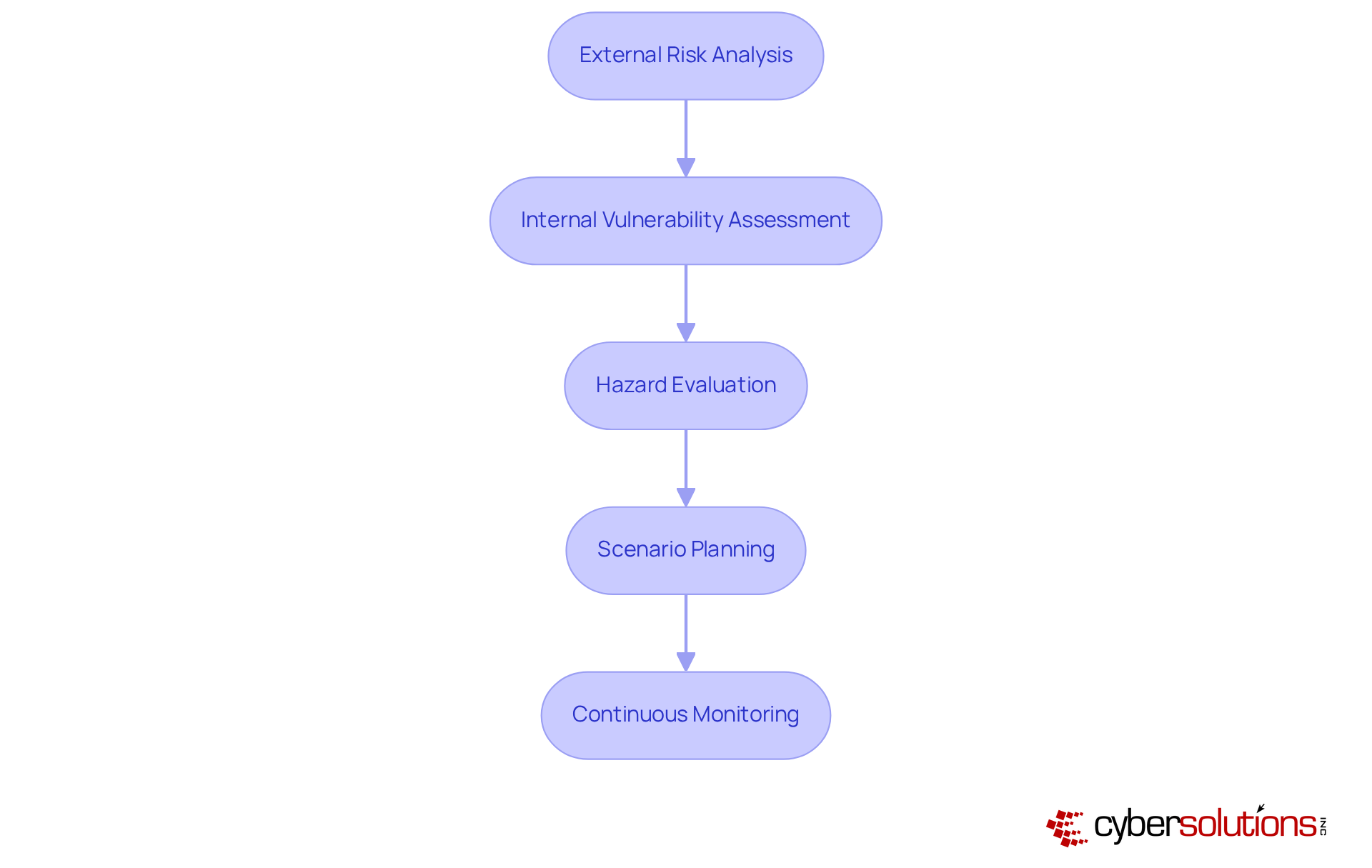
A thorough examination of the risk environment, including , is crucial for any organization, especially in the face of escalating cybersecurity threats. Understanding both external and internal dangers is essential when performing to safeguard your operations. Here are key steps to consider:
- : Stay informed about , including ransomware, phishing, and advanced persistent threats (APTs). Utilize intelligence reports and industry publications to keep up with evolving tactics and techniques.
- Internal Vulnerability Assessment: Regularly perform on your internal systems to uncover weaknesses such as outdated software, misconfigured settings, and insufficient employee training. Notably, 87% of data breaches stem from stolen credentials, underscoring the importance of robust internal security measures.
- : Assign danger scores to recognized threats based on their likelihood and potential impact. This prioritization helps address the most critical vulnerabilities first by utilizing , ensuring effective resource allocation.
- : Develop scenarios for potential attacks to visualize how they might unfold and their operational impact. This proactive exercise is essential for crafting effective response strategies and enhancing organizational resilience.
- Continuous Monitoring: Implement tools for ongoing observation of both external risks and , which includes conducting . This ensures that your organization can swiftly react to new threats, especially as .
By thoroughly examining the , enterprises can create a dynamic risk profile that adapts to the ever-evolving digital security environment. This proactive approach ultimately strengthens their safety stance and operational integrity.
Implement a Structured Cybersecurity Risk Assessment Process
To effectively implement a cybersecurity risk assessment, organizations must follow a structured process that not only enhances their but also mitigates risks:
- Define Objectives and Scope: Clearly outline the goals of the assessment and the extent of the evaluation. This includes determining which assets, systems, and processes will be assessed, ensuring alignment with organizational priorities and .
- Gather Data: Collect relevant data on assets, threats, vulnerabilities, and existing security controls. This foundational data is critical; after all, statistics show that . Comprehensive data gathering is essential for to identify potential weaknesses.
- Conduct Risk Assessment: Examine the gathered information to pinpoint threats, considering both the probability of occurrence and the potential impact on the organization. With , .
- : Based on the analysis, formulate strategies to mitigate identified threats. This may involve implementing new security controls, enhancing employee training, or revising policies to effectively address vulnerabilities.
- : Create a comprehensive report detailing the assessment results, danger levels, and recommended actions. This documentation is crucial for accountability and future reference, providing a 'single source of truth' for audits and ongoing management efforts.
- : Periodically review and revise the assessment process to reflect changes in the threat landscape, business operations, and regulatory requirements. Ongoing updates are essential, especially as , highlighting the evolving nature of security challenges.
By adhering to this organized approach, organizations can ensure that their are comprehensive, consistent, and actionable, ultimately bolstering their resilience against ever-evolving digital threats.

Maintain Continuous Assessment and Adaptation
In today’s rapidly evolving cybersecurity landscape, continuous evaluation and adaptation are vital for effective threat management, especially in healthcare. The stakes are high, and organizations must be proactive to safeguard sensitive information.
Conducting regular is crucial. These help organizations gauge their current security posture and pinpoint emerging vulnerabilities. Aim to perform these assessments at least annually or whenever significant changes occur within the organization.
- Real-Time Monitoring: Leverage , such as those provided by Cyber Solutions, to detect and respond to threats as they emerge. These tools can identify various anomalies, including unusual traffic patterns and unauthorized access attempts. With , companies can act swiftly on instant alerts and insights, significantly reducing the average time to detect breaches. This proactive approach is essential; studies indicate that organizations adopting such tools can decrease breach detection time by up to 108 days.
- : Establishing is another key practice. By integrating lessons learned from past incidents into future assessments and strategies, organizations can enhance their resilience. This iterative process ensures that entities are better equipped to tackle upcoming challenges.
- Training and Awareness: is paramount. A well-informed workforce acts as a critical line of defense against . Research shows that organizations with regular training programs experience fewer incidents. In fact, 51% of companies increased their in the past year, underscoring the growing recognition of its importance.
- Adjustment to Regulatory Changes: is essential. Organizations must modify their management strategies accordingly to ensure compliance. Those that proactively adapt to regulatory shifts are better positioned to mitigate challenges associated with non-compliance, which can lead to substantial financial penalties. For instance, the reached $10.93 million in 2023, highlighting the financial repercussions of inadequate protective measures.
By focusing on continuous assessment and adaptation, organizations can significantly bolster their cybersecurity posture and effectively navigate the ever-evolving landscape of risks.

Conclusion
Organizations today are navigating an increasingly complex cybersecurity landscape, making effective risk assessments more critical than ever. Understanding and implementing the core elements of cybersecurity risk assessments empowers leaders to proactively safeguard their assets and mitigate potential threats. Recognizing key components such as:
- Asset identification
- Risk identification
- Vulnerability assessment
- Impact analysis
- Compliance requirements
is essential in establishing a robust cybersecurity framework.
Essential practices emerge from this discussion, including the necessity for:
- Continuous monitoring
- Real-time threat detection
- Regular employee training
A structured approach to conducting risk assessments not only identifies vulnerabilities but also facilitates the development of targeted strategies for risk reduction. By maintaining an adaptive mindset, organizations can respond to the evolving threat landscape and ensure compliance with regulatory changes, ultimately protecting their operations and reputation.
The significance of ongoing cybersecurity risk management cannot be overstated. Organizations are urged to embrace these best practices and prioritize continuous assessment to enhance their security posture. As cyber threats continue to evolve, taking decisive and informed action will empower leaders to safeguard their organizations and foster resilience in an uncertain digital environment.
Frequently Asked Questions
What are the core elements of cybersecurity risk assessments?
The core elements include Asset Identification, Risk Identification, Vulnerability Assessment, Impact Analysis, and Compliance Requirements.
Why is asset identification important in cybersecurity?
Asset identification is vital because it catalogs all critical assets-hardware, software, and data-clarifying what needs protection and serving as the foundation of a robust security strategy.
What types of risks should organizations identify?
Organizations should identify potential dangers such as malware, phishing attacks, and insider threats, as approximately 90% of cyber incidents originate from phishing emails.
How does a vulnerability assessment contribute to cybersecurity?
A vulnerability assessment evaluates existing weaknesses in systems and processes, helping to pinpoint areas that could be exploited and significantly reducing the likelihood of successful attacks.
What is the significance of impact analysis in cybersecurity?
Impact analysis helps organizations understand the potential effects of a successful attack on business operations, reputation, and finances, which is crucial for prioritizing threats and avoiding severe financial repercussions.
What are compliance requirements in the context of cybersecurity?
Compliance requirements involve recognizing applicable regulatory frameworks, such as HIPAA and PCI-DSS, to ensure that organizations meet their legal obligations while addressing digital security challenges.
How can application allowlisting enhance cybersecurity risk assessments?
Application allowlisting ensures that only authorized applications can run, minimizing the attack surface and reducing risks associated with unapproved software, while also facilitating early risk identification and aligning with compliance needs.
List of Sources
- Identify Core Elements of Cybersecurity Risk Assessments
- The Top 20 Expert Quotes On Cyber Risk and Security (https://surtech.co.za/20-expert-quotes-on-cyber-risk-and-security)
- 137 Key Cybersecurity Statistics for 2026 and Beyond | Huntress (https://huntress.com/blog/cybersecurity-statistics)
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- zengrc.com (https://zengrc.com/blog/the-statistical-analysis-of-measuring-cybersecurity-risk)
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- Analyze the Threat Landscape and Vulnerabilities
- The Top Cybersecurity Threats in 2026 & How to Prevent Them | Prime Secured (https://primesecured.com/top-cybersecurity-threats-2026-and-prevention)
- What Every Company Needs To Know About Cybersecurity In 2026 (https://cybersecurityventures.com/what-every-company-needs-to-know-about-cybersecurity-in-2026)
- 2026 Global Threat Report | Latest Cybersecurity Trends & Insights | CrowdStrike (https://crowdstrike.com/en-us/global-threat-report)
- Cybersecurity Trends in 2026: Rising Threats & Strategies | TierPoint, LLC (https://tierpoint.com/blog/cybersecurity/cybersecurity-trends)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Implement a Structured Cybersecurity Risk Assessment Process
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Why and How to Perform Cybersecurity Risk Assessments in 2026 (https://maddevs.io/blog/how-to-perform-cybersecurity-risk-assessments)
- zengrc.com (https://zengrc.com/blog/the-statistical-analysis-of-measuring-cybersecurity-risk)
- 50 Risk Management Quotes: Wisdom for Smart Decision-making | ITD World (https://itdworld.com/blog/leadership/risk-management-quotes)
- Maintain Continuous Assessment and Adaptation
- For cyber risk assessments, frequency is essential (https://csoonline.com/article/4117003/cyber-risk-assessments-risk-assessment-helps-cisos.html)
- Top Cybersecurity Statistics: Facts, Stats and Breaches for 2025 (https://fortinet.com/resources/cyberglossary/cybersecurity-statistics)
- Cyber threats to watch in 2026 – and other cybersecurity news (https://weforum.org/stories/2026/02/2026-cyberthreats-to-watch-and-other-cybersecurity-news)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- 50+ Risk Management Statistics to Know in 2026 (https://secureframe.com/blog/risk-management-statistics)