
Understanding compliance in business transcends mere adherence to laws; it stands as a strategic imperative that can define an organization's success or failure. In a regulatory landscape that grows increasingly complex, leaders must grasp that effective compliance not only mitigates risks but also cultivates trust among stakeholders.
However, with such high stakes, what challenges do businesses encounter in implementing robust compliance strategies? More importantly, how can they transform these challenges into opportunities for growth?
Understanding what does is essential, as it is not just about following laws and regulations; it’s a strategic necessity that can make or break an organization. Adhering to a wide range of laws, rules, guidelines, and specifications is crucial for operational success. This includes industry standards, governmental regulations, and internal policies. By ensuring compliance, organizations can effectively mitigate risks associated with legal penalties, financial losses, and reputational damage. In today’s complex regulatory landscape, understanding transcends mere obligation; it becomes a cornerstone of and a catalyst for building .
Consider , which adopted document automation to streamline compliance with both internal quality standards and external regulations. This move significantly reduced administrative burdens and improved document accuracy. Such integration not only enhances compliance but also boosts operational efficiency, demonstrating that effective strategies can lead to substantial benefits.
Statistics reveal that 60% of compliance challenges stem from sectors like Fintech and climate change risk evaluations. This underscores the urgent need for robust regulatory frameworks. Moreover, effective , which highlight what compliance means in business, are essential for and reputation management, equipping companies to handle unexpected events and enhancing their resilience.
Expert insights emphasize that compliance is vital for maintaining investor confidence and protecting sensitive data, especially in the digital age where regulations like hold significant weight. By fostering a culture of compliance through comprehensive training and awareness, organizations can strengthen their security posture and reduce the likelihood of unintentional violations. Are you ready to elevate your compliance strategy and safeguard your organization’s future?

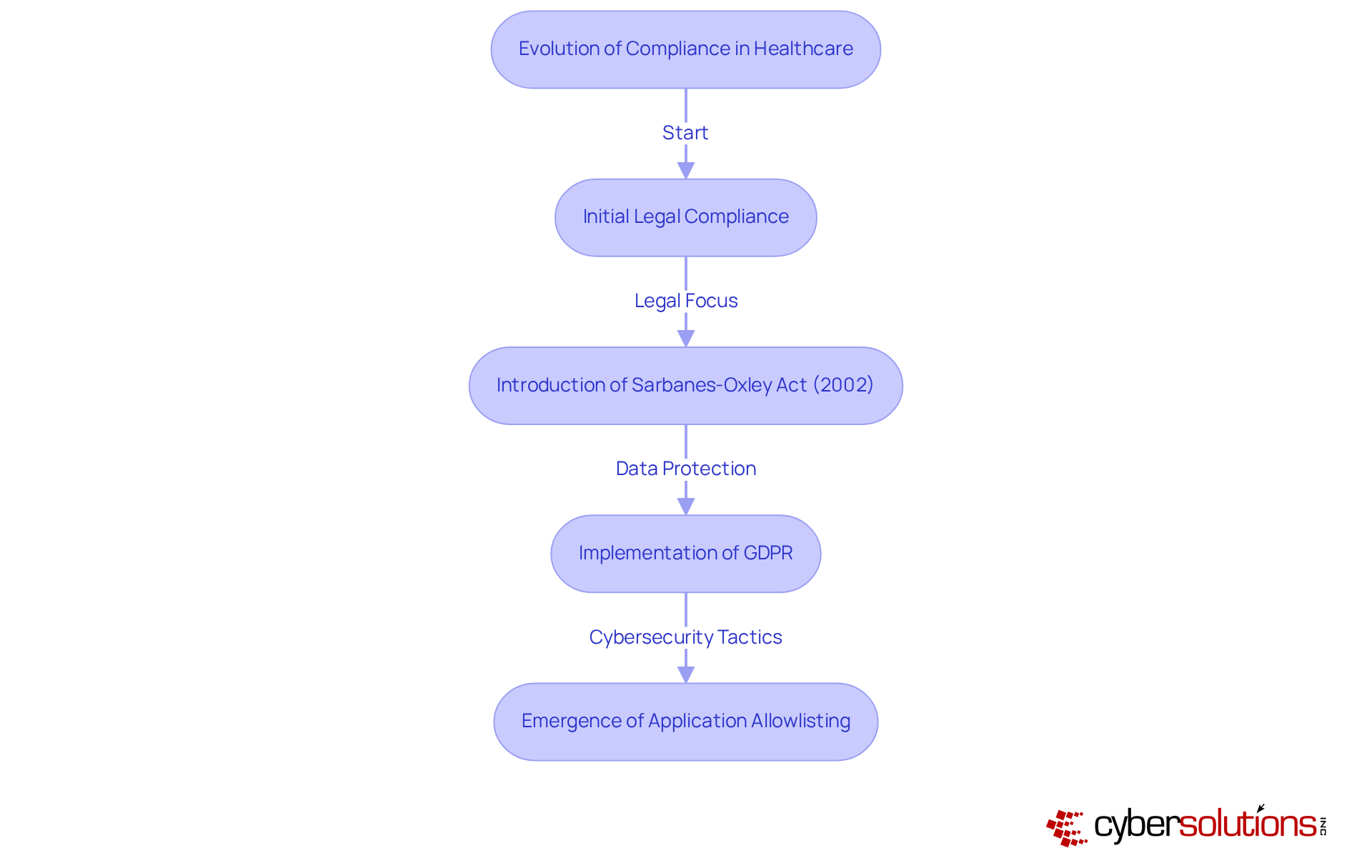
In today’s rapidly evolving landscape, the importance of cybersecurity in healthcare cannot be overstated. With increasing regulatory oversight and the rise of robust , has transformed significantly over the decades. Initially focused on legal compliance, the concept now raises the question of , as it encompasses ethical considerations and comprehensive risk management strategies. High-profile financial scandals and data breaches have driven the introduction of stricter regulations, such as the Sarbanes-Oxley Act of 2002, which mandated enhanced in response to corporate fraud. Similarly, the General Data Protection Regulation (GDPR) implemented in Europe underscores a growing emphasis on .
These developments highlight what compliance means in business as a crucial component of corporate strategy, fundamentally shaping how businesses operate and engage with stakeholders. In this context, emerges as an essential cybersecurity tactic. This approach not only prevents unauthorized software from running but also aids organizations in meeting stringent . By limiting the applications that can operate, businesses can significantly reduce their attack surface, thereby minimizing vulnerabilities and .
This proactive method is vital for understanding regarding standards like and , ensuring that organizations maintain strict control over software usage while safeguarding sensitive information. Features of , such as continuous monitoring and centralized management, further bolster adherence efforts by enabling organizations to swiftly identify and block unauthorized applications. The historical context reveals a recurring pattern: public outrage over misconduct has consistently driven legislative changes, resulting in standards that address both legal obligations and ethical expectations.
As healthcare CFOs navigate these challenges, it’s imperative to recognize that robust cybersecurity measures are not just a regulatory requirement but a strategic necessity. How prepared is your organization to tackle these evolving threats?
In today's digital landscape, the importance of cannot be overstated. With increasing regulatory demands and the constant threat of cyberattacks, organizations must prioritize to protect sensitive information. Understanding what compliance means in business involves key components such as:
requires strict adherence to industry-specific laws and regulations, such as HIPAA for healthcare and PCI-DSS for payment processing. For entities managing federal data, compliance with CMMC standards is essential. This framework includes three tiers of cybersecurity practices designed to safeguard sensitive information:
Internal policies establish the entity's standards and procedures, while effective identifies potential adherence challenges and implements strategies to mitigate them. programs are crucial; in fact, 60% of risk and regulatory professionals indicate that cybersecurity will be a key training topic in the next two to three years. procedures enable organizations to assess their adherence status and make necessary adjustments.
Furthermore, leveraging solutions can streamline the process of meeting regulatory obligations, ensuring continuous alignment. Collectively, these components form a robust compliance framework that exemplifies what compliance means in business, fostering organizational integrity and accountability. In navigating the complexities of today's regulatory landscape, it is imperative for healthcare organizations to adopt these practices, ensuring they not only meet compliance requirements but also protect their most valuable asset: patient trust.

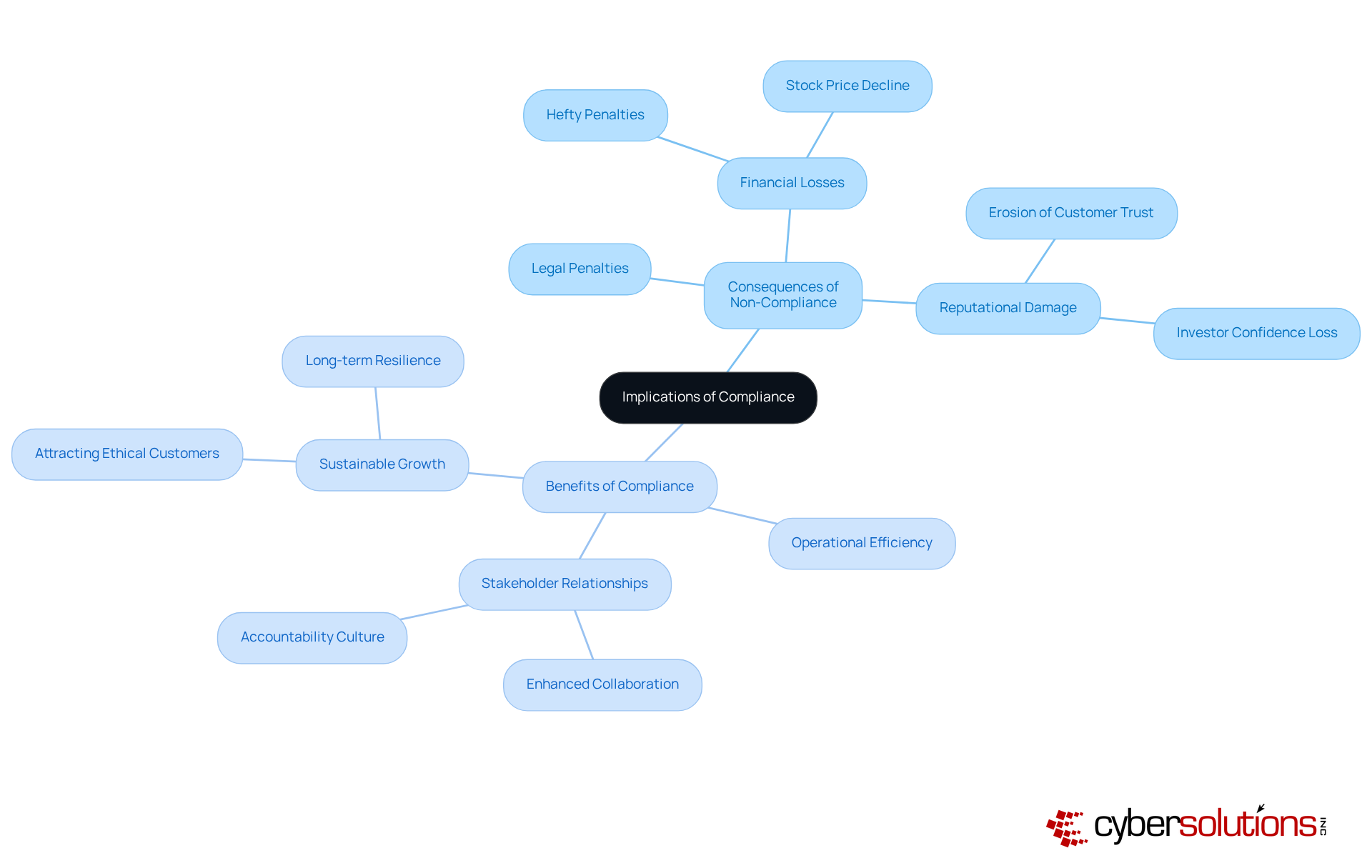
Organizations must understand what , as it holds significant weight and impacts both their legal standing and financial performance. The consequences of non-compliance can be severe, leading to , legal actions, and even the loss of business licenses. These repercussions not only deplete financial resources but also , eroding customer trust and investor confidence. For example, companies under often experience a sharp decline in stock prices, with research showing that as much as 30% of their market value.
Conversely, a robust regulatory program can enhance operational efficiency, foster a , and . Organizations that prioritize understanding what are better positioned to and adapt to the ever-changing business environment. This proactive stance not only mitigates risks but also sets the stage for sustainable growth, as these companies are more likely to attract and retain customers who value ethical practices. Ultimately, the extend beyond merely avoiding penalties; they bolster overall organizational resilience and enhance reputation in the marketplace.
Understanding compliance in business transcends mere adherence to laws and regulations; it stands as a strategic imperative that profoundly influences an organization's integrity, reputation, and operational success. Compliance is not just a checkbox; it serves as a foundational element that enables businesses to navigate complex regulatory landscapes while fostering trust among stakeholders. By prioritizing compliance, organizations position themselves to avoid legal pitfalls and enhance their overall performance and resilience in a competitive marketplace.
Key insights from this discussion reveal the multifaceted nature of compliance, which encompasses:
The evolution of compliance reflects a growing emphasis on ethical standards and proactive measures, such as application allowlisting and comprehensive training programs. These components work synergistically to create a robust compliance framework that safeguards sensitive information and enhances organizational accountability.
In light of these considerations, leaders must recognize the long-term benefits of a strong compliance strategy. Investing in compliance initiatives allows organizations to mitigate risks, protect their reputations, and ultimately drive sustainable growth. Embracing compliance as a core business principle not only ensures adherence to regulations but also strengthens relationships with customers and investors who value ethical business practices. The call to action is clear: prioritize compliance today to secure a prosperous and resilient future for your organization.
What does compliance mean in business?
Compliance in business refers to adhering to a wide range of laws, rules, guidelines, and specifications essential for operational success. It goes beyond merely following laws and regulations; it is a strategic necessity that helps mitigate risks associated with legal penalties, financial losses, and reputational damage.
Why is compliance important for organizations?
Compliance is crucial for organizations as it ensures operational integrity, builds stakeholder trust, and helps mitigate risks. It is also essential for maintaining investor confidence and protecting sensitive data, especially in the context of stringent regulations like GDPR.
How can organizations improve their compliance efforts?
Organizations can improve compliance by adopting effective strategies such as document automation to streamline processes, reducing administrative burdens, and enhancing document accuracy. Additionally, fostering a culture of compliance through comprehensive training and awareness can strengthen security and reduce the likelihood of violations.
What are some common challenges in compliance?
Common compliance challenges arise particularly in sectors like Fintech and climate change risk evaluations, with statistics indicating that 60% of challenges stem from these areas. This highlights the need for robust regulatory frameworks.
How does compliance contribute to business continuity and reputation management?
Effective compliance strategies are essential for business continuity and reputation management as they equip companies to handle unexpected events and enhance their resilience in a complex regulatory landscape.
What role does technology play in compliance?
Technology, such as document automation, plays a significant role in compliance by streamlining processes, improving accuracy, and reducing administrative burdens, thereby enhancing overall operational efficiency and compliance efforts.