
In an era where cyber threats are evolving at an alarming pace, the urgency for robust cybersecurity measures is paramount. Cyber assessment services offer organizations a thorough evaluation of their cybersecurity posture, uncovering vulnerabilities and ensuring adherence to vital regulations. As the threat landscape shifts, how can businesses effectively navigate the complexities of these assessments to safeguard their assets and bolster their resilience against future attacks? This article explores the significance of cyber assessment services, their key characteristics, and real-world applications, providing insights that empower organizations to strengthen their defenses.
In today's digital landscape, the importance of robust cybersecurity cannot be overstated, especially for organizations navigating complex regulatory environments. Cyber assessment services offer a systematic evaluation of a company's cybersecurity posture, emphasizing the identification of vulnerabilities, risk assessment, and ensuring compliance with relevant regulations. These services utilize a variety of methodologies, including:
to deliver comprehensive insights into security strengths and weaknesses.
By utilizing cyber assessment services, organizations engage in evaluations that provide critical knowledge, empowering them to implement effective strategies for risk reduction and enhance their overall security framework. Furthermore, Cyber Solutions offers Compliance as a Service (CaaS), simplifying the navigation of regulatory requirements through thorough risk assessments, policy development, and continuous monitoring of compliance. This proactive approach not only addresses immediate security concerns but also fosters long-term resilience.
When combined with our Incident Response services, which swiftly identify, contain, and mitigate threats, organizations can ensure business continuity while effectively managing their security landscape. In an era where cyber threats are ever-evolving, investing in comprehensive cybersecurity solutions is not just a necessity - it's a strategic imperative.

In the current landscape of increasingly sophisticated cyber threats, the significance of cyber assessment services is paramount. Organizations are confronted with a myriad of risks, including data breaches, ransomware attacks, and regulatory violations, all of which can result in substantial financial losses and reputational damage. For instance, the average cost of a data breach skyrocketed to $4.4 million in 2025, underscoring the urgent need for proactive cybersecurity measures.
Organizations can utilize Cyber Assessment Services to gain essential tools for identifying vulnerabilities and implementing robust security protocols. These services ensure compliance with critical regulations such as HIPAA and GDPR, which are vital in today’s regulatory environment. A structured response plan is crucial for effective incident management, allowing organizations to respond swiftly and efficiently to potential threats.
By prioritizing these evaluations, businesses can effectively safeguard their assets and maintain trust with clients and stakeholders. This proactive approach not only enhances their security posture but also boosts resilience against evolving cyber threats. In an era where the stakes are higher than ever, investing in cyber assessment services is not just a choice; it’s a necessity.

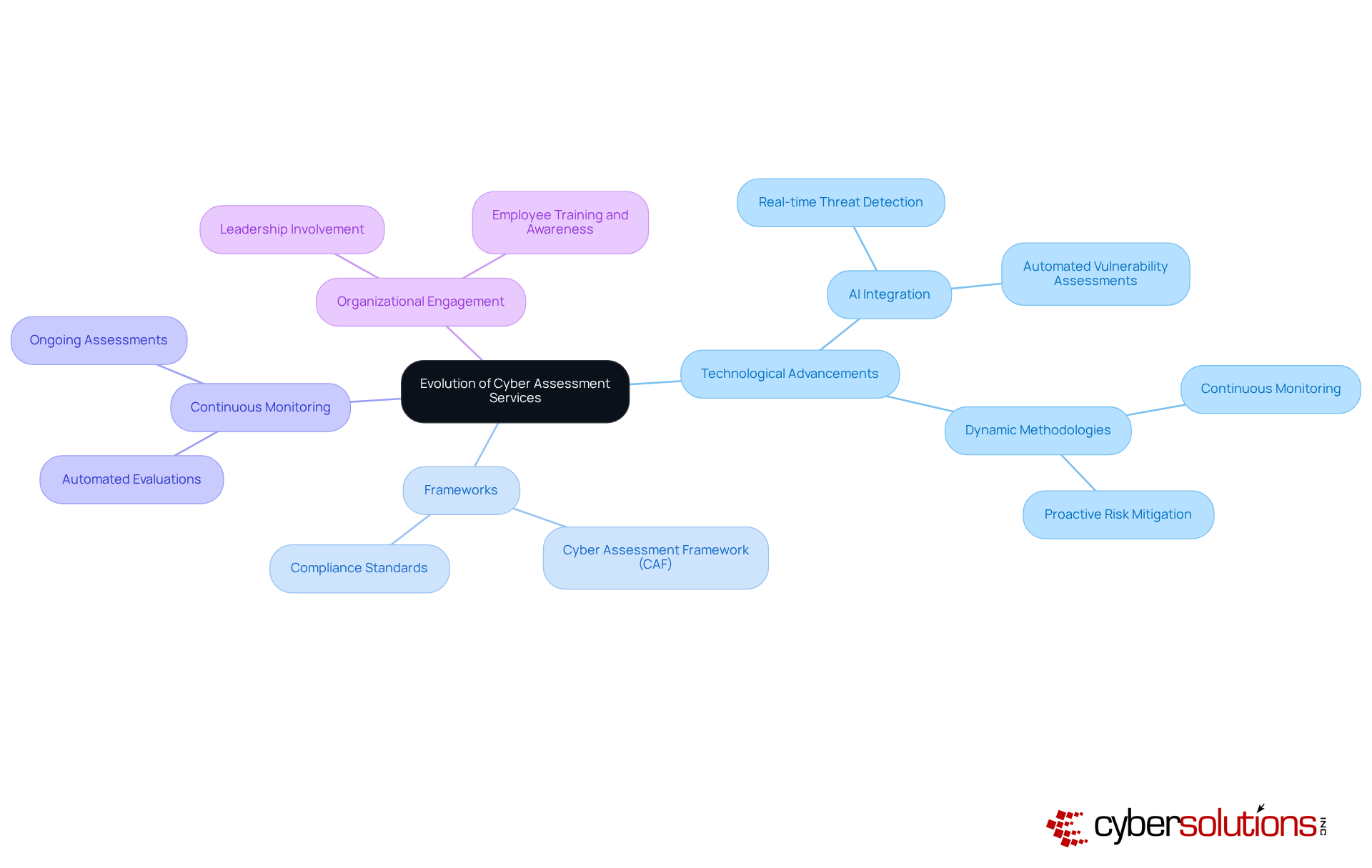
Cybersecurity is not just a technical necessity; it’s a fundamental pillar of organizational strategy, especially in healthcare. As the threat landscape becomes increasingly complex, organizations must adapt to protect sensitive data and maintain trust. Cyber assessment services have evolved significantly, transitioning from basic vulnerability assessments to sophisticated evaluations that utilize cutting-edge technologies. The integration of artificial intelligence and machine learning has revolutionized these services, enabling entities to proactively identify and mitigate risks more effectively.
AI-driven tools now analyze vast amounts of data to detect vulnerabilities and threats in real-time, drastically reducing response times to incidents. Frameworks like the Cyber Assessment Framework (CAF) standardize methodologies, ensuring consistent measurement of cybersecurity postures across various sectors. This standardization is crucial as organizations face stringent regulations and the need for compliance.
In this intricate threat environment, continuous monitoring and automated evaluations are no longer optional; they are essential. These advancements not only enhance the effectiveness of cyber assessment services but also promote adherence to regulatory requirements. Current trends indicate a shift towards dynamic assessment methodologies that prioritize resilience and adaptability. Companies are increasingly recognizing the necessity for ongoing assessments rather than sporadic reviews, fostering a culture of continuous improvement in security practices.
This evolution underscores a broader understanding that cybersecurity is integral to organizational success. It requires active engagement from leadership and all employees. Are you ready to embrace this shift and enhance your organization’s cybersecurity posture? The time for proactive measures is now.
In today's digital age, the importance of cybersecurity cannot be overstated, especially in healthcare. With the rise of sophisticated cyber threats, organizations face unique challenges that demand immediate attention and action. Cyber assessment services offer a comprehensive approach to risk evaluation by utilizing standardized frameworks such as the NIST Cybersecurity Framework and ISO/IEC 27001. These frameworks not only enhance the effectiveness of cyber evaluation services but also ensure compliance with increasingly stringent data protection laws expected in 2026.
Effective assessments encompass various components, including:
Statistics reveal that organizations employing standardized frameworks experience a 30% increase in the effectiveness of their cybersecurity measures. This structured approach is crucial for delivering actionable insights and tailored recommendations that meet the specific needs of each organization.
Collaboration between the evaluation team and internal stakeholders is vital for successful cyber evaluations. Engaging different departments ensures that findings are communicated clearly and that remediation efforts are prioritized. As cybersecurity experts emphasize, "Organizations that proactively embrace collaboration will embed resilience into their cultural fabric and operations."
Moreover, integrating automated tools into the assessment process significantly boosts efficiency and accuracy, allowing for timely identification of vulnerabilities. This proactive stance is essential as cyber threats continue to evolve, with 87% of security professionals reporting exposure to AI-enabled tactics in recent years. Understanding Compliance as a Service (CaaS) is critical, as it streamlines regulatory processes for small and medium-sized enterprises (SMEs) and provides comprehensive solutions for legal obligations, including audit preparation and ongoing monitoring.
By adopting best practices and fostering a culture of collaboration, organizations can markedly enhance their cybersecurity posture and resilience against emerging threats.

Cyber assessment services play a crucial role across various industries, especially in enhancing security and compliance. In the financial sector, for instance, banks routinely engage in penetration testing to simulate cyberattacks. This practice allows them to pinpoint vulnerabilities and strengthen their defenses against potential breaches. Given that financial breaches account for 10% of all cyberattacks, this proactive approach is essential for maintaining robust security measures.
Consider a notable case study involving a major bank that undertook a comprehensive cyber evaluation. This assessment uncovered critical weaknesses in its network infrastructure. Following the evaluation, the bank enhanced its security measures, resulting in a remarkable 30% reduction in successful phishing attempts within just six months. Such focused evaluations can lead to significant improvements in security posture, especially when combined with strategies like application allowlisting, which prevents unauthorized software from executing.
Moreover, government organizations frequently engage in cyber evaluations to ensure compliance with federal regulations, safeguarding sensitive information from cyber threats. For example, a recent evaluation by a federal agency revealed gaps in their data protection strategies, prompting immediate updates to their cybersecurity framework. This not only ensured compliance but also fortified their defenses against evolving cyber threats.
Statistics further highlight the urgency of these assessments: in 2024, healthcare entities reported an average of 40 cyberattacks per organization, underscoring the critical need for regular evaluations of security measures. By utilizing cyber assessment services alongside application allowlisting, organizations can effectively identify risks and implement meaningful enhancements that bolster their overall security posture and ensure compliance with regulatory standards.

In today’s rapidly evolving digital landscape, the importance of cybersecurity cannot be overstated, especially in healthcare. As organizations strive to protect sensitive patient data and maintain trust, the role of cyber assessment services becomes paramount. These services offer a structured evaluation of a company’s security posture, enabling healthcare organizations to identify vulnerabilities, assess risks, and ensure compliance with stringent regulations.
The current cybersecurity threats are not just abstract concepts; they pose real challenges for healthcare CFOs and decision-makers. With the rise of sophisticated cyberattacks, the implications for healthcare organizations are profound. Cyber assessment services, employing methodologies like vulnerability assessments and penetration testing, empower businesses to enhance their security frameworks. By integrating standardized frameworks, these assessments become comprehensive and effective, fostering a culture of resilience through proactive measures such as continuous monitoring and collaboration among stakeholders.
Real-world examples illustrate the tangible benefits of these services. For instance, organizations that have prioritized cyber assessments have significantly reduced vulnerabilities and improved compliance across various sectors, including finance and healthcare. This evolution, driven by advancements in technology like artificial intelligence, has transformed how organizations approach cybersecurity, making it essential to stay ahead of potential threats.
Ultimately, the call to action is clear: healthcare organizations must prioritize cyber assessment services as a critical component of their cybersecurity strategy. By investing in these evaluations, businesses not only shield themselves from potential breaches but also cultivate trust with clients and stakeholders. In a landscape where the stakes are continually rising, embracing a proactive approach to cybersecurity is not just advisable; it’s essential for long-term success and sustainability.
What are cyber assessment services?
Cyber assessment services provide a systematic evaluation of a company's cybersecurity posture, focusing on identifying vulnerabilities, assessing risks, and ensuring compliance with relevant regulations.
What methodologies are used in cyber assessment services?
The methodologies used include vulnerability assessments, penetration testing, and regulatory audits.
How do cyber assessment services benefit organizations?
They empower organizations with critical knowledge to implement effective strategies for risk reduction and enhance their overall security framework.
What is Compliance as a Service (CaaS)?
Compliance as a Service (CaaS) simplifies the navigation of regulatory requirements through thorough risk assessments, policy development, and continuous monitoring of compliance.
How do cyber assessment services contribute to long-term resilience?
They address immediate security concerns while fostering long-term resilience by ensuring ongoing compliance and enhancing security protocols.
Why is it important for organizations to invest in cyber assessment services?
Investing in cyber assessment services is crucial due to the increasing sophistication of cyber threats, which can lead to significant financial losses and reputational damage.
What are the potential consequences of not utilizing cyber assessment services?
Organizations may face data breaches, ransomware attacks, and regulatory violations, which can result in substantial financial losses and damage to their reputation.
How do cyber assessment services help with regulatory compliance?
They ensure compliance with critical regulations such as HIPAA and GDPR, which are essential in today’s regulatory environment.
What role does a structured response plan play in incident management?
A structured response plan allows organizations to respond swiftly and efficiently to potential threats, enhancing their incident management capabilities.
How do cyber assessment services enhance security posture?
By prioritizing evaluations, businesses can effectively safeguard their assets and maintain trust with clients and stakeholders, thereby boosting their resilience against evolving cyber threats.