
Understanding the complexities of IT infrastructure is essential for organizations aiming to maintain operational continuity in an unpredictable environment. Failover—an automatic switch to a backup system during a primary system failure—stands out as a vital element of business resilience. This article explores the significance of failover strategies, demonstrating how they not only protect against costly downtime but also boost overall operational efficiency. As businesses confront the daunting challenge of unexpected outages, one question emerges: how can organizations effectively implement failover systems to ensure seamless continuity and safeguard their bottom line?
? It is not merely a technical term; it serves as a vital lifeline for businesses. This automated process illustrates , as it allows a system to seamlessly switch to a standby or backup system when the primary one fails or experiences an outage. In today’s fast-paced IT landscape, it is crucial to understand what is failover. It ensures that remain operational, . It can manifest in various forms—hardware redundancy, software solutions, and network configurations—all working together to help organizations mitigate the risks associated with unexpected failures and disruptions.
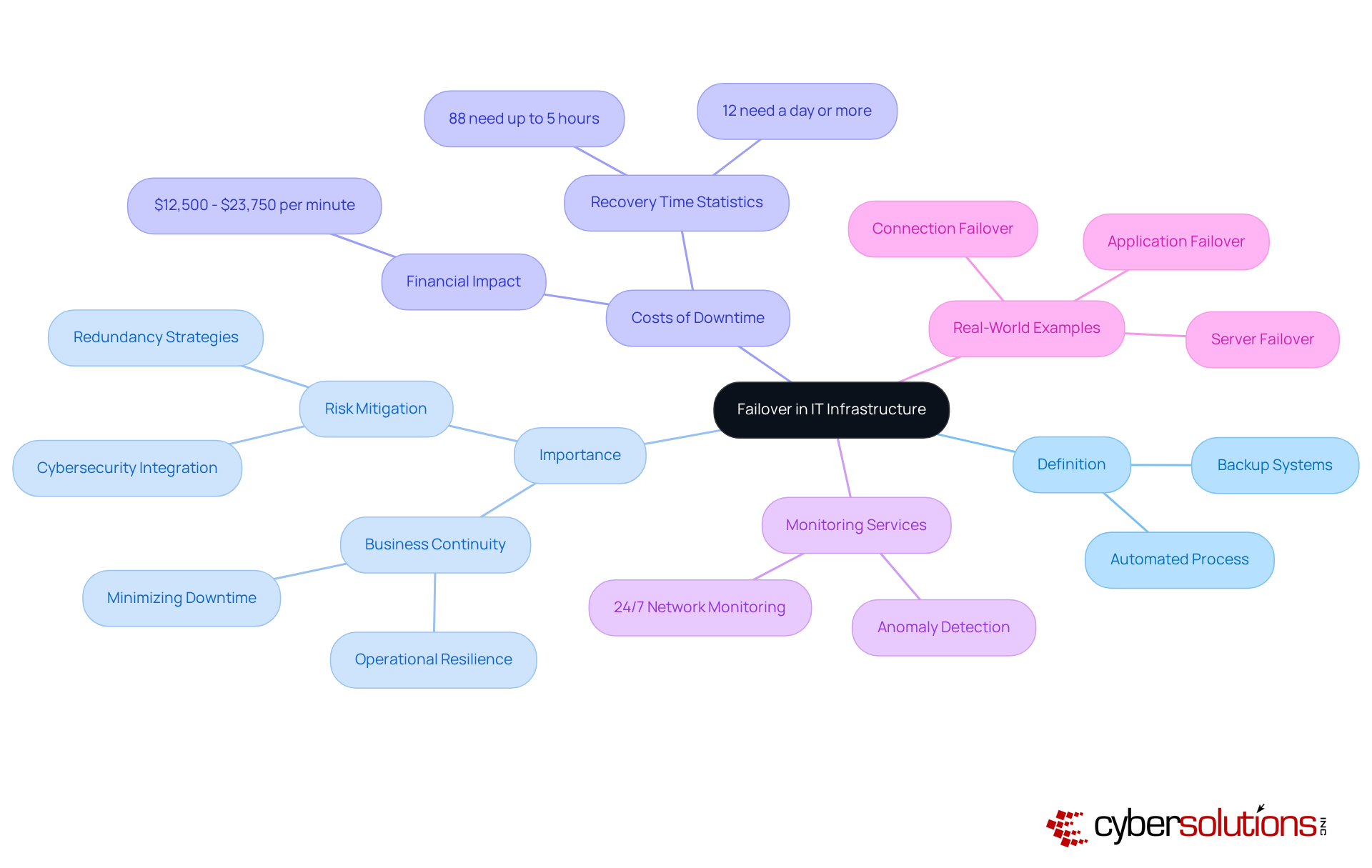
Consider the staggering costs associated with IT downtime: it can range from $12,500 to $23,750 per minute. These figures starkly illustrate the . Furthermore, research shows that 88% of geographically distributed companies take up to five hours to restore their network after a failure, with 12% requiring a day or more. Such statistics underscore the pressing need for robust to ensure .
To enhance , 24/7 are indispensable. Continuous oversight of network activities allows organizations to detect anomalies and potential vulnerabilities in real-time. This proactive approach enables swift action to prevent downtime or breaches, effectively safeguarding against threats like ransomware and phishing attacks. Ongoing observation ensures that questionable behaviors are identified and addressed before they escalate into major issues, highlighting the necessity of integrating with comprehensive cybersecurity plans.
Real-world examples further illustrate the effectiveness of these backup mechanisms. For instance, in a data center, when a server's power supply fails, a backup system activates a secondary power source, ensuring operations continue without interruption. Similarly, connection redundancy guarantees continuous network connectivity by redirecting traffic through alternative routes during internet service disruptions. This is vital for businesses that rely on constant internet access for operations such as credit card transactions and remote work. Such implementations not only protect against downtime but also enhance overall operational efficiency, making redundancy a cornerstone of modern IT strategies. Moreover, the failback procedure—reverting operations to the main setup after an interruption—is essential for ensuring continuity and minimizing disruptions.
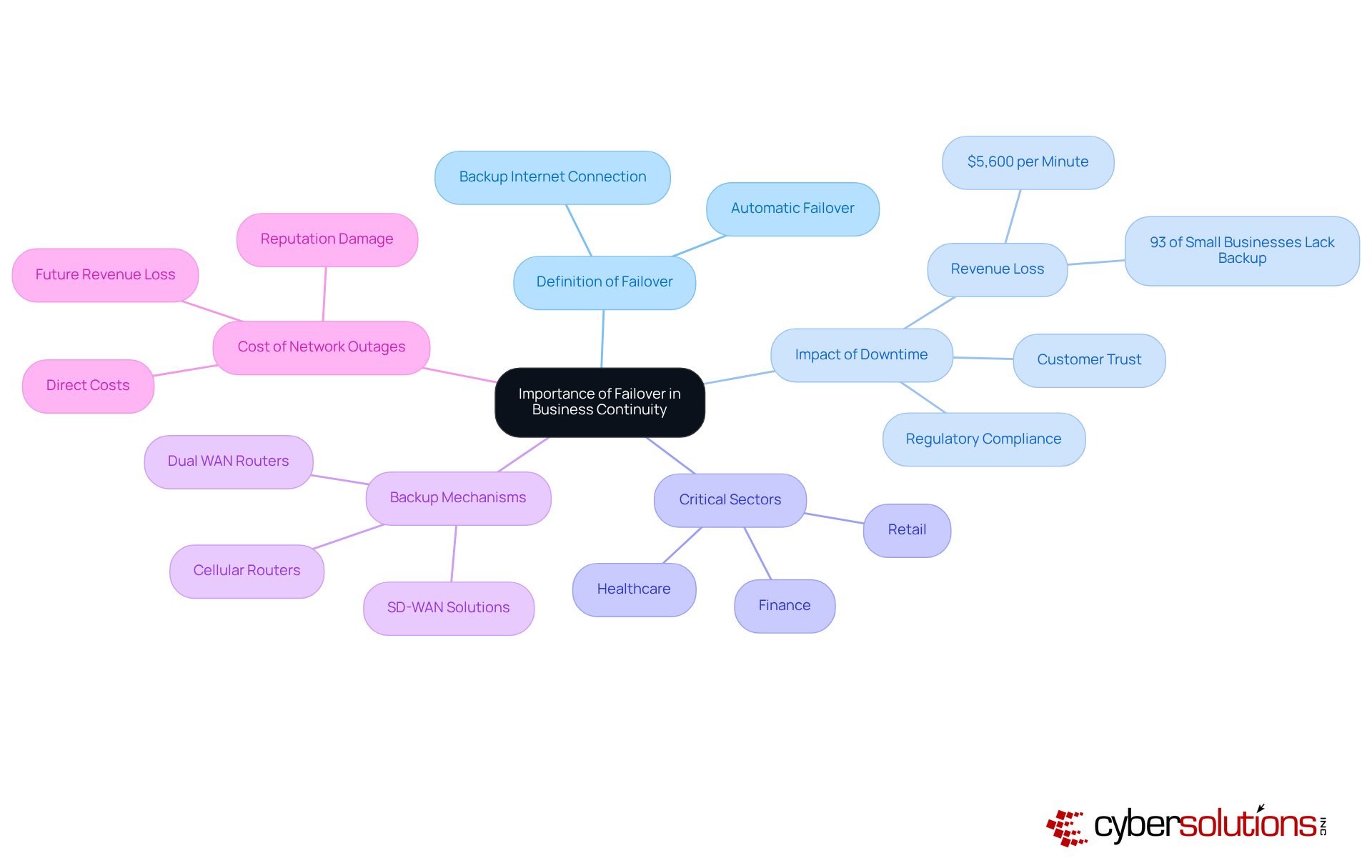
? It is not merely a technical necessity; rather, it serves as a cornerstone of effective . In an era where unforeseen disruptions can strike at any moment, organizations must ensure they can sustain operations seamlessly. By implementing robust , companies significantly mitigate the risks associated with downtime, which can lead to , diminished customer trust, and potential regulatory repercussions.
Consider critical sectors like healthcare and finance, where the integrity and accessibility of data are paramount. Here, are not merely beneficial; they are essential for keeping vital services operational. This capability safeguards sensitive information and ensures . The swift transition to backup systems not only enhances but also fosters a proactive risk management strategy.
Did you know that network outages can cost businesses approximately $5,600 every minute? This staggering figure underscores the and establishing strong solutions. It's not just a protective measure; it's a strategic investment in preserving business continuity and .
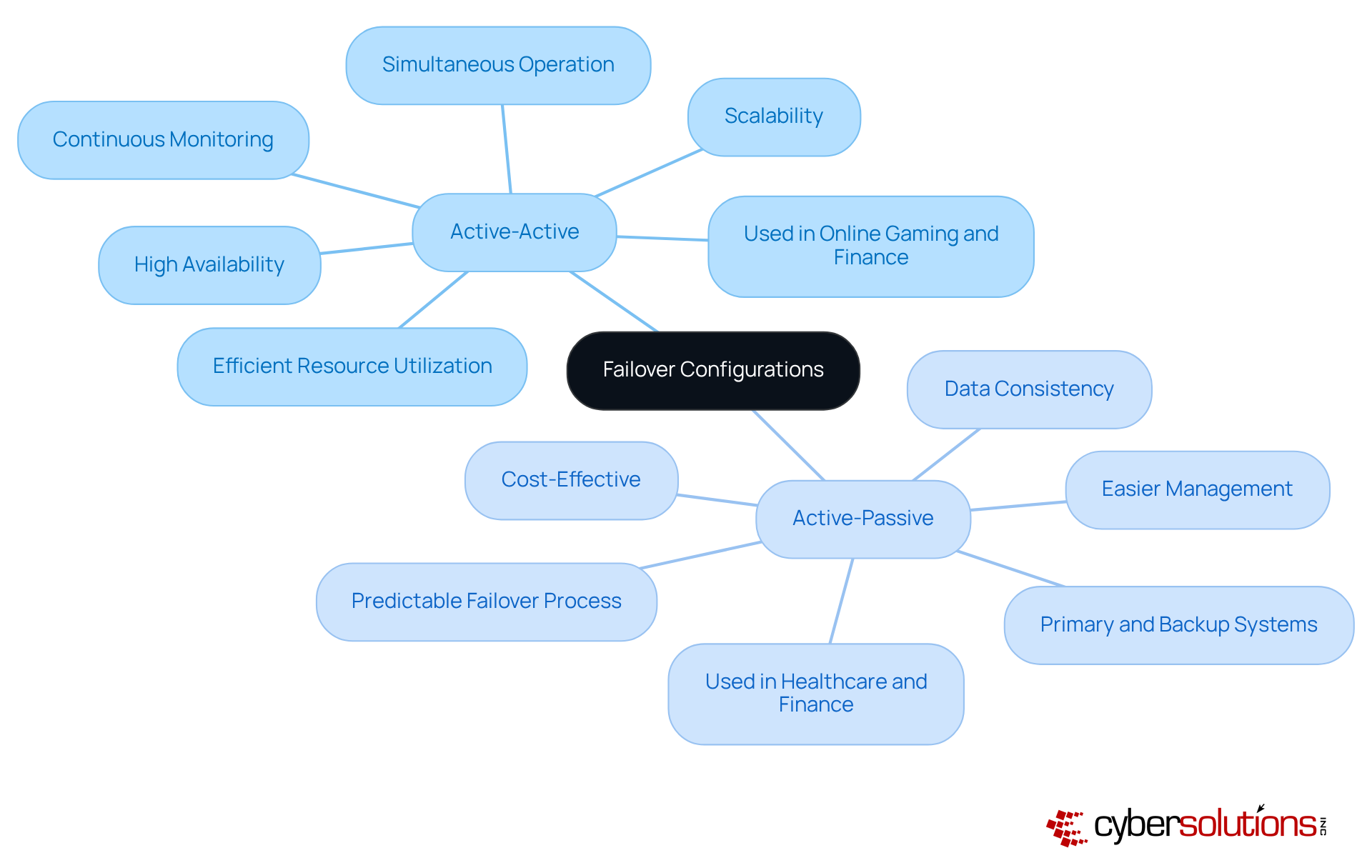
Understanding is essential for maintaining , as these setups come in various forms tailored to meet specific organizational needs. The two primary configurations are active-active and active-passive.
In an , multiple units operate simultaneously, sharing workloads and providing redundancy. This arrangement not only boosts performance but also ensures that if one component fails, others can seamlessly take over, resulting in nearly zero downtime. Industries like online gaming and finance reap significant benefits from this model, as it facilitates and rapid response times—critical factors for user satisfaction and operational efficiency. Continuous monitoring of these networks is vital for understanding , as it allows for quick identification of issues and minimizes potential disruptions. Cyber Solutions offers to detect anomalies and vulnerabilities, ensuring that suspicious activities are addressed before they escalate into threats.
Conversely, the features one primary system managing the workload while a backup system remains on standby, ready to engage in case of a failure. This approach is often preferred in sectors such as healthcare and finance, where are crucial. s are generally easier to manage and can be more cost-effective, making them suitable for applications where the criticality of operations does not require constant engagement of all nodes.
Choosing between these setups involves considering factors like cost, complexity, and the critical nature of the applications involved. While s may entail higher initial costs due to the need for all nodes to be operational, they provide . In contrast, active-passive setups may lead to longer outage durations during transitions but offer a straightforward path to on a budget.
Understanding what is failover and these configurations empowers organizations to implement the most effective tailored to their operational context, ensuring resilience against disruptions and maintaining .
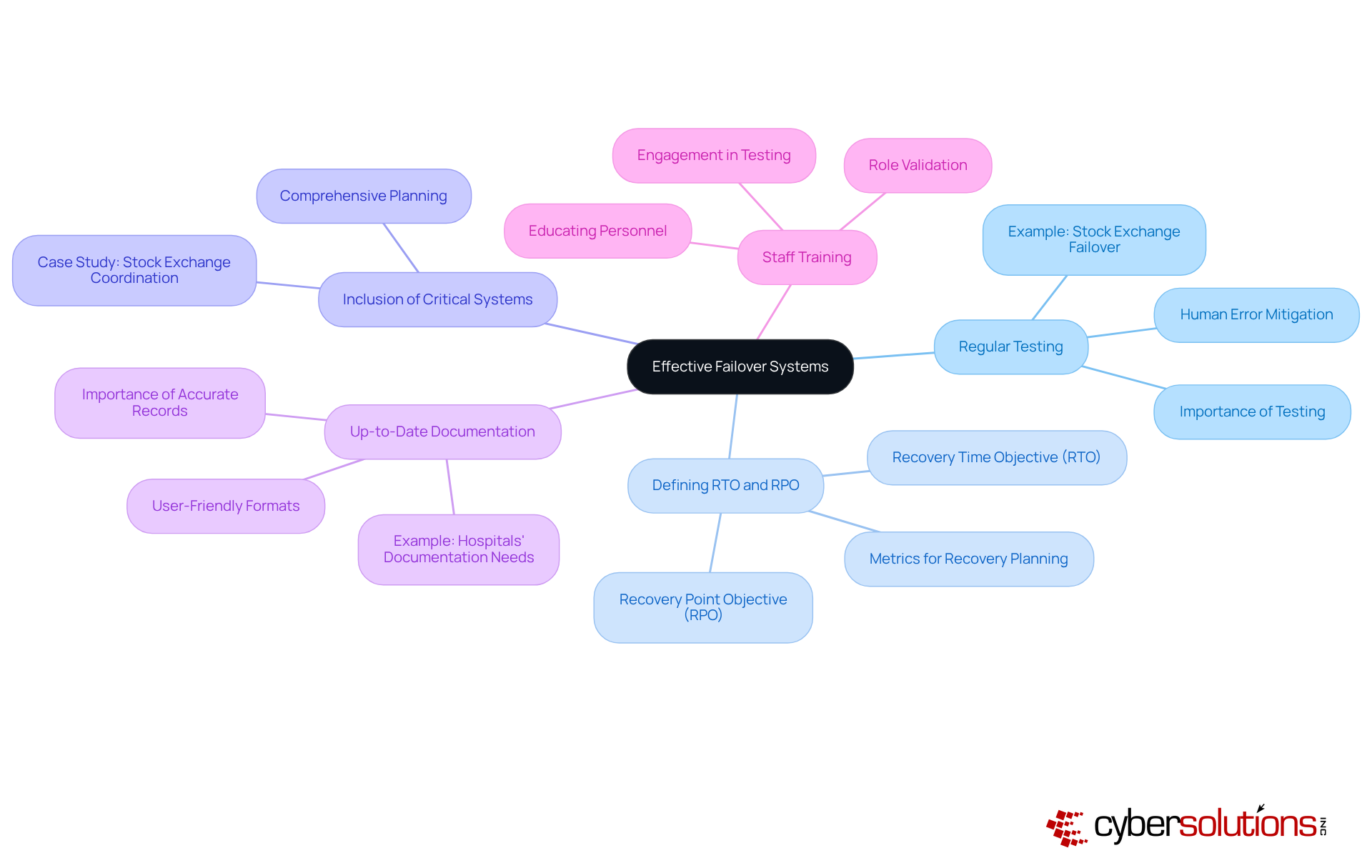
Implementing effective backup systems is not just a necessity; it’s a critical component of organizational resilience. In today’s fast-paced environment, where disruptions can occur at any moment, having a robust is essential. Here are key best practices that every organization should adopt:
By adhering to these best practices, organizations can bolster their resilience against disruptions and ensure a rapid recovery when failures occur. Are you ready to take the necessary steps to safeguard your organization?
Understanding the concept of failover is crucial for any organization that wants to maintain operational continuity amid unexpected disruptions. It’s not just a technical term; it’s a strategic approach that ensures critical systems stay functional, safeguarding business operations and preserving customer trust. By implementing effective failover mechanisms, businesses can significantly mitigate the risks associated with downtime, which can lead to severe financial and reputational consequences.
This article has delved into the multifaceted nature of failover, emphasizing its importance in business continuity planning and the various configurations available, such as active-active and active-passive setups. The staggering costs tied to network outages and the essential role that robust backup systems play in sectors like healthcare and finance have been highlighted. Moreover, best practices for implementing effective failover strategies—like regular testing, clear recovery objectives, and comprehensive staff training—have been discussed. These insights serve as a roadmap for organizations aiming to bolster their resilience against potential disruptions.
In an era where operational disruptions are increasingly prevalent, the significance of failover cannot be overstated. Organizations must prioritize the development and implementation of robust failover strategies to ensure they can swiftly recover from failures and continue serving their customers. By investing in effective backup systems and fostering a culture of preparedness, businesses not only protect their operations but also position themselves for long-term success in an unpredictable landscape.
What is failover in IT infrastructure?
Failover is an automated process that allows a system to switch to a standby or backup system when the primary system fails or experiences an outage. It is crucial for maintaining the operational continuity of critical workloads, applications, and services.
Why is failover important for businesses?
Failover is important because it minimizes downtime and preserves business continuity, helping organizations mitigate the risks associated with unexpected failures and disruptions.
What are the costs associated with IT downtime?
The costs of IT downtime can range from $12,500 to $23,750 per minute, highlighting the significant financial impact of unexpected outages.
How long does it typically take to restore a network after a failure?
Research shows that 88% of geographically distributed companies take up to five hours to restore their network after a failure, with 12% requiring a day or more.
What role does network monitoring play in failover strategies?
24/7 network monitoring and alert services are essential for detecting anomalies and potential vulnerabilities in real-time, enabling swift action to prevent downtime or breaches.
Can you provide examples of failover mechanisms in action?
In a data center, if a server's power supply fails, a backup system activates a secondary power source to ensure operations continue. Additionally, connection redundancy allows traffic to be redirected through alternative routes during internet service disruptions, maintaining continuous connectivity.
What is the failback procedure?
The failback procedure involves reverting operations to the main setup after an interruption, which is essential for ensuring continuity and minimizing disruptions.