
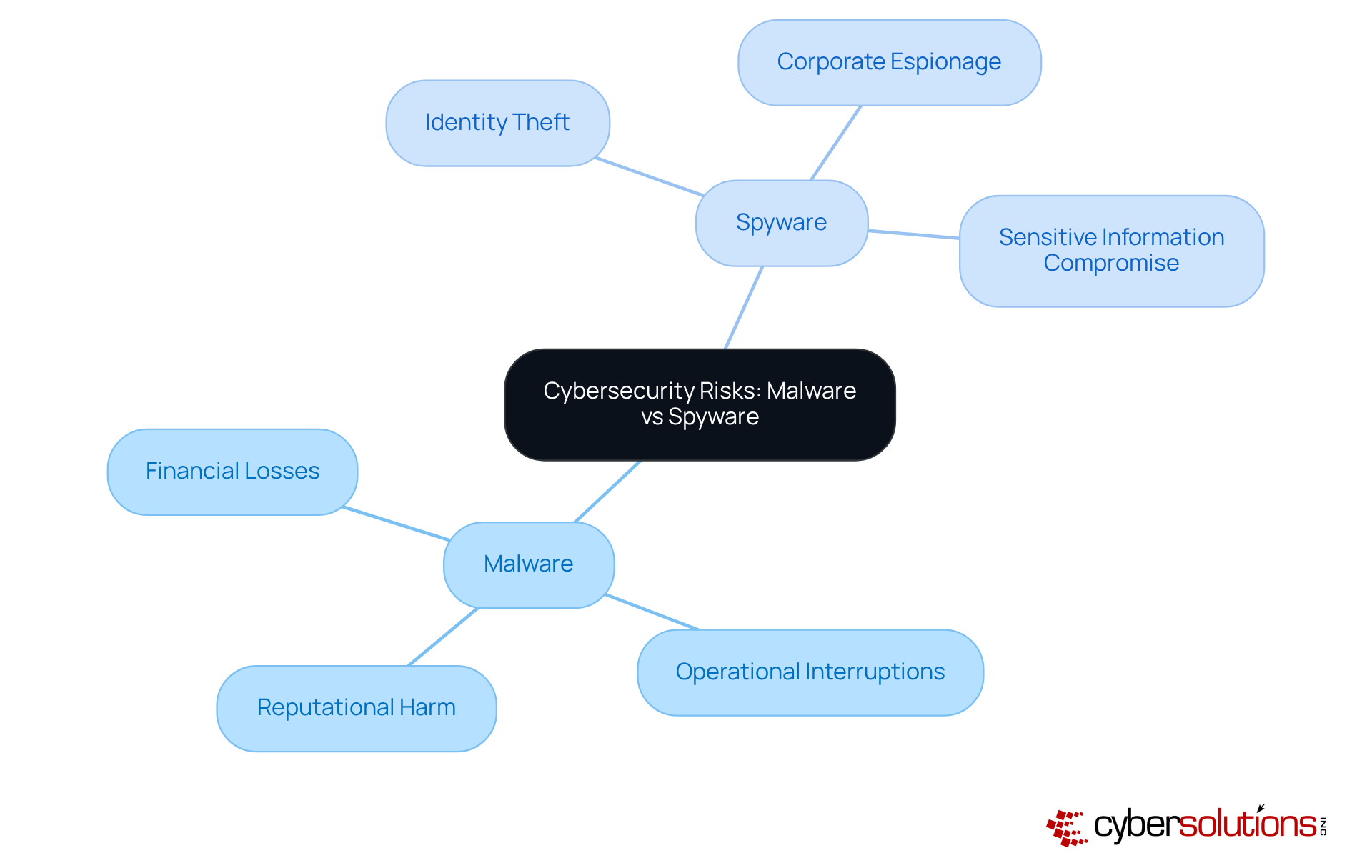
In today’s landscape, where digital threats are more pronounced than ever, grasping the differences between malware and spyware is essential for organizational leaders. These two forms of malicious software not only disrupt operations but also threaten sensitive data and financial stability. Understanding these distinctions is vital for C-suite executives as they navigate the unique challenges each type presents.
How prepared are organizations to confront these evolving threats? What proactive measures can be implemented to protect their assets? By delving into the nuances of malware and spyware, leaders can better equip their organizations to face these challenges head-on. Cybersecurity is not just a technical issue; it’s a critical component of organizational resilience.
Malware, short for , encompasses a wide range of harmful programs designed to disrupt, damage, or gain unauthorized access to computer systems. This category includes various types such as viruses, worms, ransomware, and spyware. As we look ahead to 2026, the landscape of malicious software is evolving rapidly, with over 1 billion variants in existence. This alarming statistic underscores the urgent need for organizations to implement robust cybersecurity measures.
Spyware, a specific type of harmful software, is crafted to secretly monitor user activities and collect sensitive information without consent. It often infiltrates systems through deceptive tactics, like phishing emails or malicious downloads. Shockingly, 93% of the components necessary for malicious software to function are already present in most computers, making it particularly insidious and challenging to detect.
While all spyware is harmful software, the discussion of clarifies that not all harmful software qualifies as spyware. This distinction highlights the necessity for tailored defenses against these unique threats. Recent statistics reveal that 40% of malicious software attacks result in . This reality emphasizes the critical need for organizations to understand these dangers and their implications. For instance, -a specific type of malicious software-have cost companies an average of $4.54 million, significantly impacting revenue and operational continuity.
Practical examples further illustrate the consequences of these threats. In 2023, the education sector experienced a staggering 94% revenue loss among ransomware victims, while the finance industry remains highly vulnerable, with over 60% of financial service companies exposing sensitive files to all employees. These figures highlight the pressing need for C-suite leaders to prioritize that effectively address both malware vs spyware.
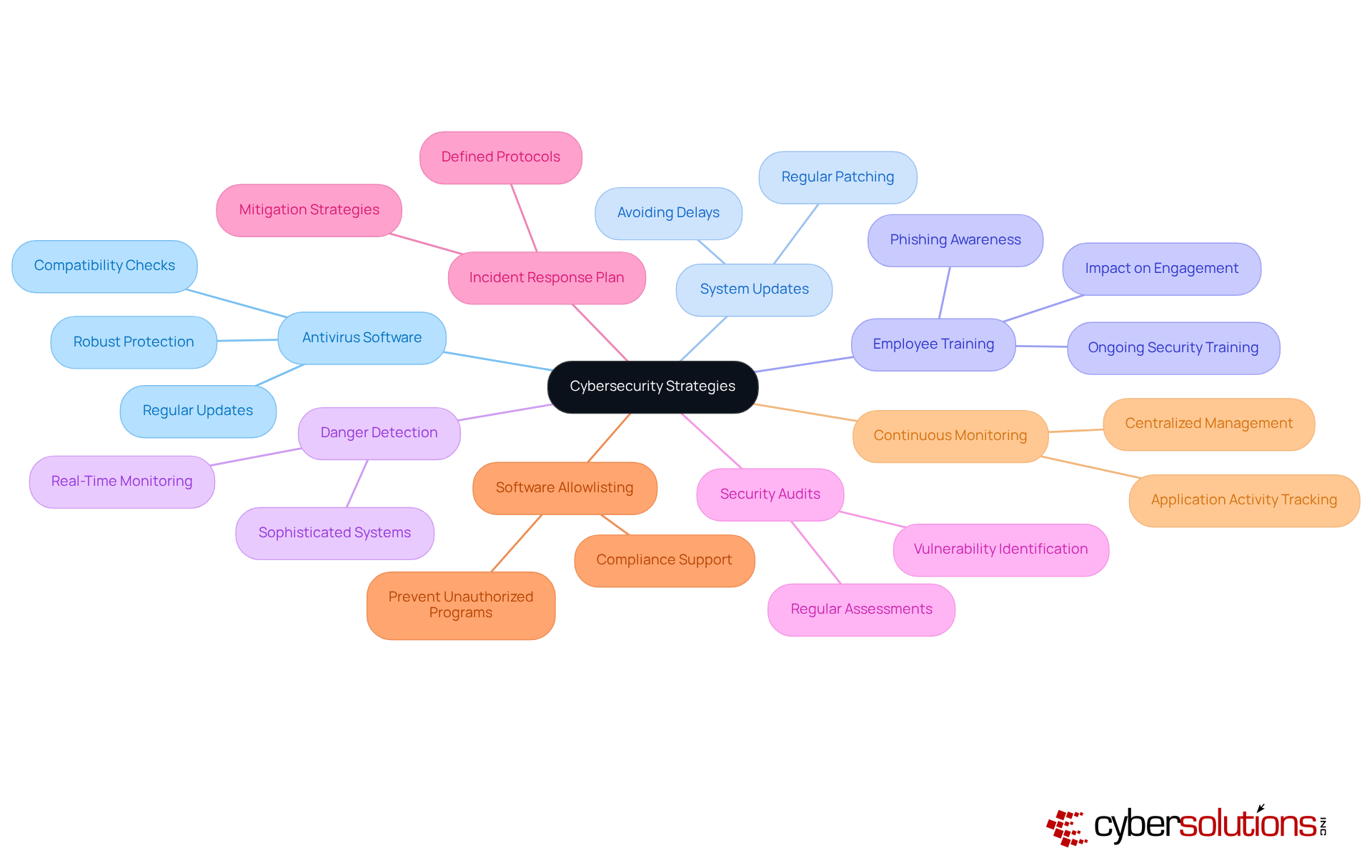
To combat these threats, software allowlisting emerges as a vital strategy. By permitting only pre-approved programs to run, organizations can proactively prevent unauthorized software from executing, thereby reducing the attack surface and minimizing vulnerabilities. This approach not only blocks malware and ransomware but also ensures compliance with such as HIPAA, PCI-DSS, and GDPR. Features like centralized management and continuous monitoring of software activity further enhance the effectiveness of allowlisting, ensuring prompt identification and blocking of threats. C-suite leaders must recognize as a cornerstone of their defense mechanisms.

Cybersecurity is not just a technical issue; it’s a critical concern for healthcare organizations today. With the rise of threats in the debate of designed to disrupt operations, steal sensitive data, and inflict harm through aggressive tactics like encryption and system corruption, the stakes have never been higher. Malicious software operates stealthily, focusing on data gathering without alerting users, making it particularly dangerous. While signs of malicious software, such as system slowdowns or crashes, can be evident, spyware often goes unnoticed, complicating detection efforts.
Consider this: that the can exceed $4.54 million. This staggering figure underscores the . Therefore, are not just advisable; they are essential. Organizations must implement and leverage to identify and mitigate these risks.
Moreover, . By blocking unauthorized programs from running, it minimizes the attack surface significantly. Ensuring that only authorized applications can operate not only strengthens defenses against malicious software but also helps .
Understanding these distinctions is crucial for building robust cybersecurity frameworks capable of effectively addressing both malicious software and tracking threats. Are your current strategies sufficient to protect your organization? It's time to take action and fortify your defenses.

Cybersecurity is not just a technical issue; it’s a critical concern that can make or break healthcare organizations today. With the debate of evolving in complexity and frequency, understanding its various forms - such as viruses, worms, , and Trojans - is essential. Did you know that ? This statistic underscores their prevalence and effectiveness in breaching systems. Ransomware, which encrypts files and demands payment for decryption, is increasingly common, with 59% of organizations reporting incidents in 2024.
Moreover, in the context of , malicious software can be categorized into types like adware, keyloggers, and tracking cookies, each serving specific . Adware generates revenue through advertisements while monitoring user behavior, whereas keyloggers capture keystrokes to extract sensitive information. In 2023, a staggering , highlighting its widespread impact.
Understanding these varieties, particularly malware vs spyware, is crucial for organizations aiming to implement targeted defenses and response strategies. plays a vital role in this defense strategy by or malicious programs from executing. This approach reduces the attack surface and minimizes vulnerabilities. Key features of software allowlisting include:
Additionally, are essential for addressing incidents when they occur. This proactive approach not only safeguards sensitive data but also ensures compliance with regulations such as , PCI-DSS, and GDPR. As the cybersecurity landscape evolves, staying informed about the latest trends in malicious software and surveillance programs, along with implementing robust solutions like application allowlisting, is essential for maintaining operational integrity.
In conclusion, the stakes are high, and the time to act is now. Are you prepared to protect your organization from these ever-evolving threats?

Cybersecurity is not just a technical issue; it’s a critical component of operational integrity in healthcare. The risks associated with can lead to substantial financial losses, operational interruptions, and reputational harm. The comparison of malware vs spyware highlights how attacks can result in , necessitating costly remediation efforts and potentially exposing organizations to legal liabilities.
Consider this: how prepared is your organization to handle a malware attack? The reality is that many healthcare organizations are vulnerable. 'Cyber Solutions' offers specialized designed to tackle these pressing issues efficiently. We guarantee that are sanitized, updated, and reimaged as required, ensuring your systems are fortified against future threats.
The discussion of malware vs spyware reveals that while spyware is less overt, it poses a significant risk by compromising sensitive information, leading to or corporate espionage. By implementing proactive measures such as application allowlisting, organizations can prevent unauthorized software from executing. This not only reduces vulnerabilities but also enhances overall security.
The cumulative effect of these risks can strain resources and hinder business growth. It’s essential for organizations to adopt , including robust and employee cyber hygiene training. Are you ready to take action and safeguard your organization’s future?
In today’s digital landscape, the importance of cybersecurity cannot be overstated, especially for organizations in the healthcare sector. With the rise of , a multi-layered security strategy is essential. This strategy must include:
Sophisticated danger detection systems are vital for identifying potential risks, while regular help uncover vulnerabilities before they can be exploited. Moreover, establishing a well-defined is crucial for mitigating damage in the event of a cyberattack. Implementing is another essential measure, proactively preventing unauthorized or malicious programs from executing. This significantly reduces the attack surface and aids organizations in meeting . By allowing only sanctioned programs to operate, Cyber Solutions ensures that businesses can effectively prevent ransomware and other threats.
Additionally, continuous monitoring of application activity and centralized management of allowlists enhance security and streamline policy enforcement. By integrating these strategies, organizations can significantly lower their risk exposure and strengthen their overall . Notably, companies that engage in ongoing experience a 70% reduction in security incidents. This statistic underscores the importance of equipping employees with the knowledge to navigate today’s complex threat landscape. Are you ready to take action and safeguard your organization against these evolving threats?
Understanding the distinction between malware and spyware is not just important; it’s essential for C-suite leaders who are committed to safeguarding their organizations against the ever-evolving landscape of cyber threats. Malware encompasses a broad category of malicious software, including harmful programs like viruses and ransomware. In contrast, spyware specifically targets user data through covert monitoring. By recognizing these differences, leaders can implement tailored cybersecurity strategies that effectively mitigate risks associated with both threats.
The alarming prevalence of these threats cannot be overstated. Statistics reveal that a significant portion of organizations experience data breaches and financial losses due to malware attacks. This reality underscores the necessity of proactive measures. One vital strategy is software allowlisting, which prevents unauthorized applications from executing, thereby reducing vulnerabilities and ensuring compliance with regulatory standards.
As the stakes continue to rise, organizations must adopt a multi-layered cybersecurity approach. This includes robust detection systems, comprehensive employee training, and regular system updates. C-suite leaders must prioritize these initiatives to fortify their defenses against malware and spyware. Ultimately, this commitment protects sensitive information and maintains operational integrity. Taking decisive action now will pave the way for a more secure future in an increasingly complex digital landscape.
What is malware?
Malware, short for malicious software, refers to a variety of harmful programs designed to disrupt, damage, or gain unauthorized access to computer systems. This includes viruses, worms, ransomware, and spyware.
What is spyware?
Spyware is a specific type of malware that secretly monitors user activities and collects sensitive information without consent, often infiltrating systems through deceptive tactics like phishing emails or malicious downloads.
How prevalent is malware?
As of 2026, there are over 1 billion variants of malware, highlighting the urgent need for organizations to implement robust cybersecurity measures.
What percentage of malicious software attacks result in data theft?
Recent statistics indicate that 40% of malicious software attacks lead to data theft or leaks of sensitive information.
What are the financial impacts of ransomware attacks?
Ransomware attacks have cost companies an average of $4.54 million, significantly affecting their revenue and operational continuity.
Which sectors are particularly vulnerable to ransomware?
In 2023, the education sector saw a 94% revenue loss among ransomware victims, while the finance industry remains vulnerable, with over 60% of financial service companies exposing sensitive files to all employees.
What is software allowlisting?
Software allowlisting is a cybersecurity strategy that permits only pre-approved programs to run on a system, helping to prevent unauthorized software from executing and minimizing vulnerabilities.
How does software allowlisting enhance cybersecurity?
By blocking unauthorized programs, allowlisting reduces the attack surface, strengthens defenses against malware and ransomware, and helps ensure compliance with regulatory standards such as HIPAA, PCI-DSS, and GDPR.
What are the signs of malicious software?
Signs of malicious software may include system slowdowns or crashes, although spyware often operates unnoticed, complicating detection efforts.
Why is it essential for organizations to implement effective cybersecurity strategies?
The financial ramifications of malware attacks can be significant, with costs averaging over $4.54 million per attack. Therefore, effective detection and response strategies are crucial for protecting sensitive data and maintaining operational integrity.